Analyzing TNEF files
Yesterday I came across a file type I rarely have to analyze: "Transport Neutral Encapsulation Format". It's an attachment file format used by Outlook and Exchange.
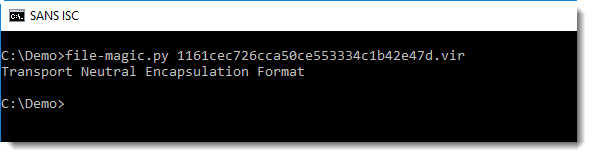
Here is how the file command identifies it:
There are different free and opensource programs and libraries that can parse this file format. There's a Python module tnefparse that comes with a parsing program:
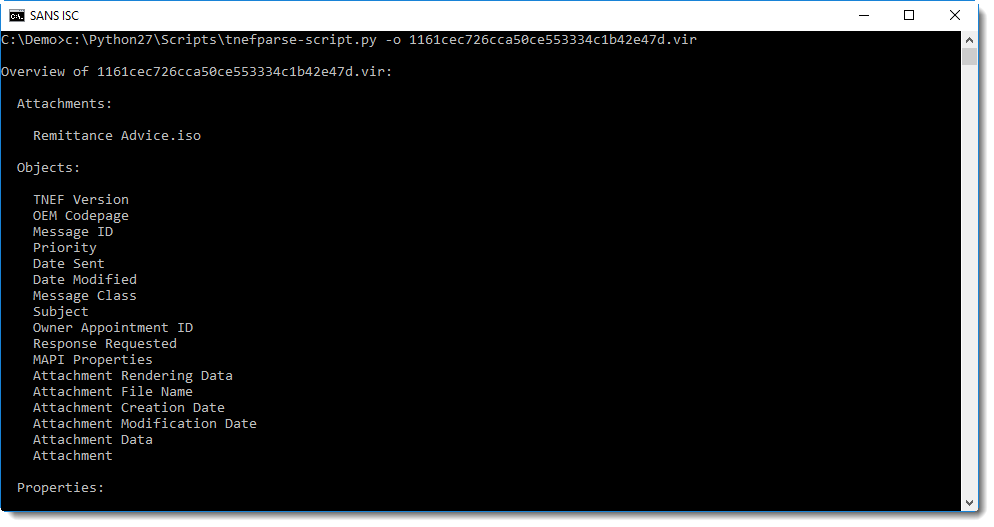
So this TNEF file contains one attached file: an .iso file.
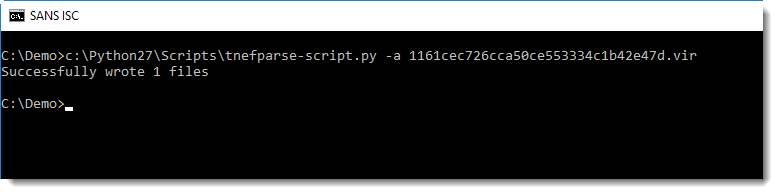
tnefparse can extract this .iso file:
I've covered the analysis of .iso files before in this diary entry.
With 7-zip, I can look into the .iso file:
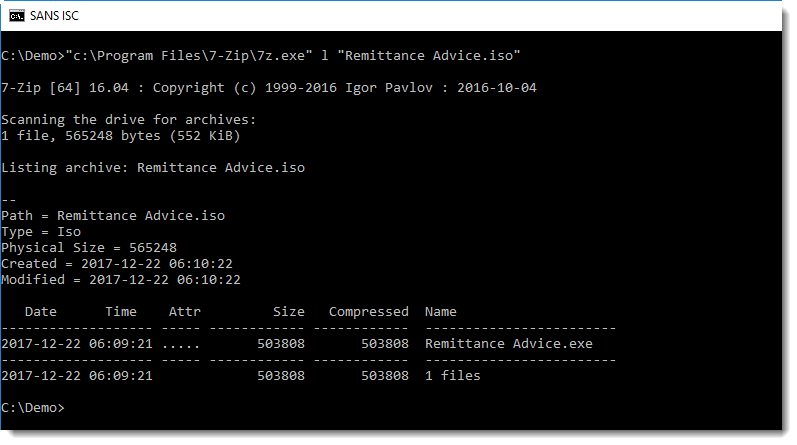
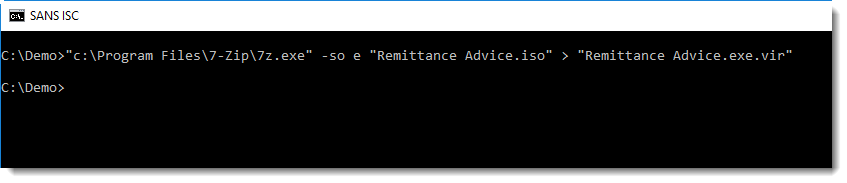
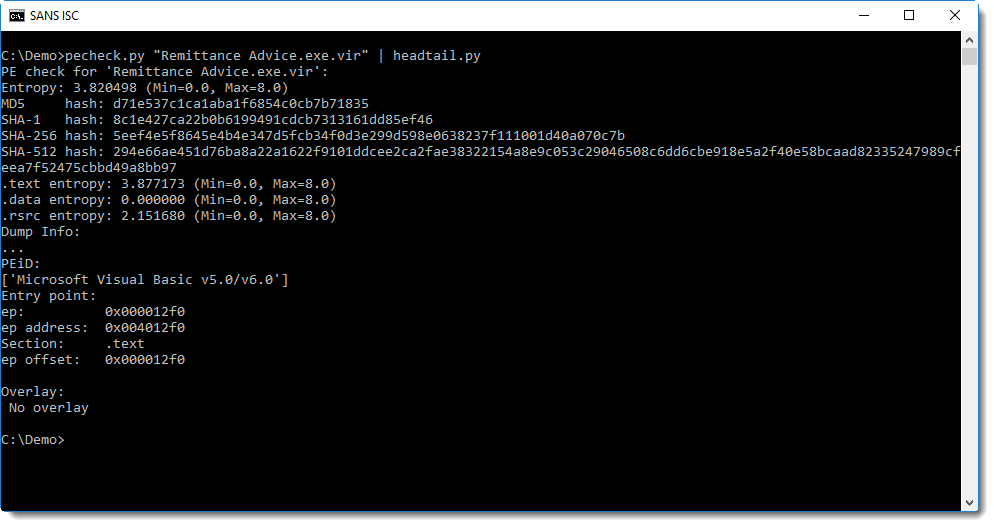
And extract the .exe (MD5 d71e537c1ca1aba1f6854c0cb7b71835) file:
Didier Stevens
Microsoft MVP Consumer Security
blog.DidierStevens.com DidierStevensLabs.com
Click HERE to learn more about classes Didier is teaching for SANS
×
![modal content]()
Diary Archives


Comments