An Introduction to VolUtility
If you would like to practice memory forensics using Volatility but you don't like command line tools and you hate to remmber plugins then VolUtility is your friend.
Volutility1 2 is a web frontend for Volatility framework.
Installation
In this dairy, I will install VolUtlity on Linux SIFT3 workstation.
- Update your SIFT workstation and install django with the following commands:
|
$ sudo apt-get update && sudo apt-get upgrade $ sudo pip install pymongo django
|
- Install MongoDB :
In this dairy I am not going to discuss how to install MongoDB , for futher details about how to install MongoDB please refer to:
https://docs.mongodb.com/v3.2/tutorial/install-mongodb-on-ubuntu/
- Install Volatility
|
$ git clone https://github.com/volatilityfoundation/volatility $ cd volatility $ sudo python setup.py install |
- Get VolUtility
|
$ git clone https://github.com/kevthehermit/VolUtility |
Configuration
In this diary I am going to use the default config file “volutility.conf.sample”
Running
cd in to the VolUtility folder and run the following command , in this diary I will use port 8000 as a listening port
|
$ ./manage.py runserver 0.0.0.0:8000 |
Usage
VolUtility operates on the principal of sessions. Each memory image has its own session that is used to track all the plugin results and associated data.
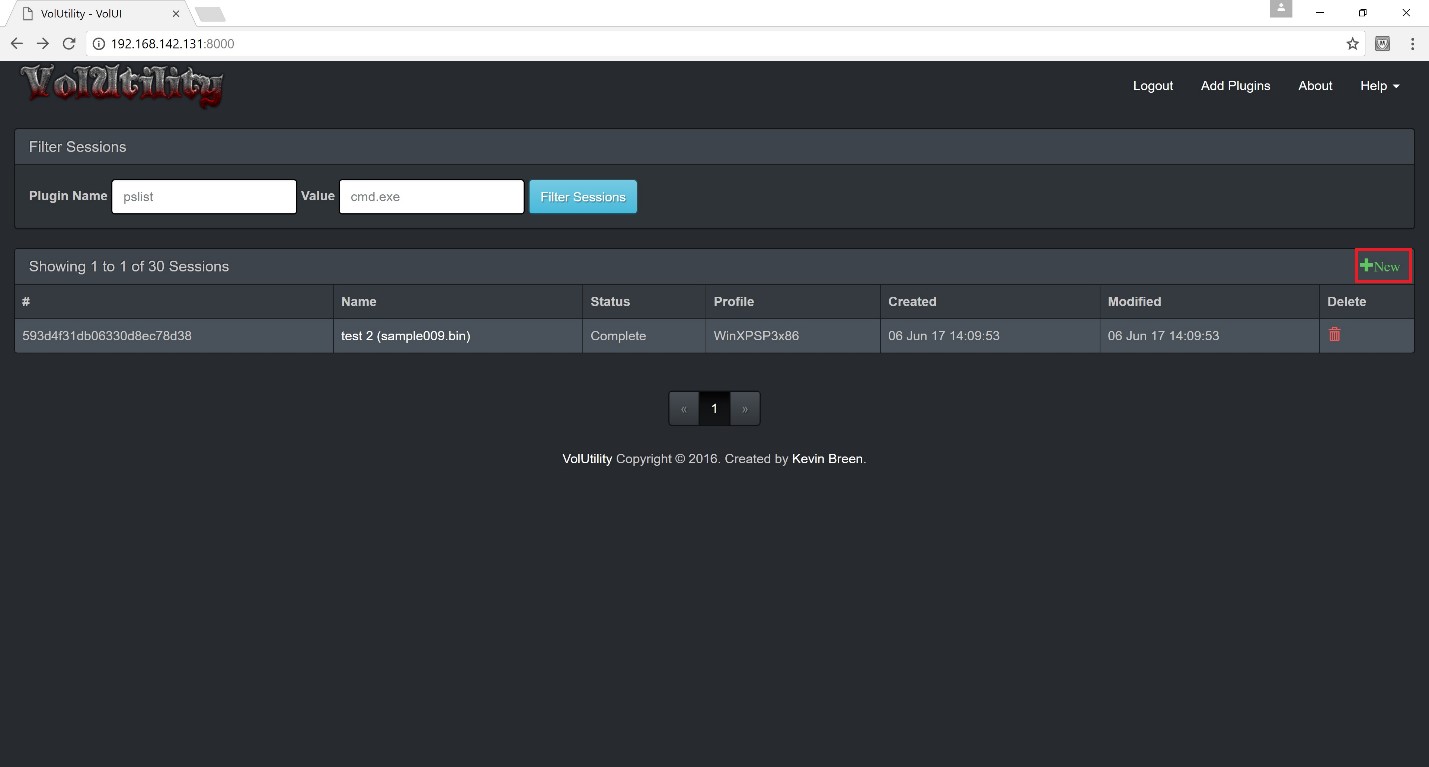
To create a new session, navigate to the home page and click the New + Button
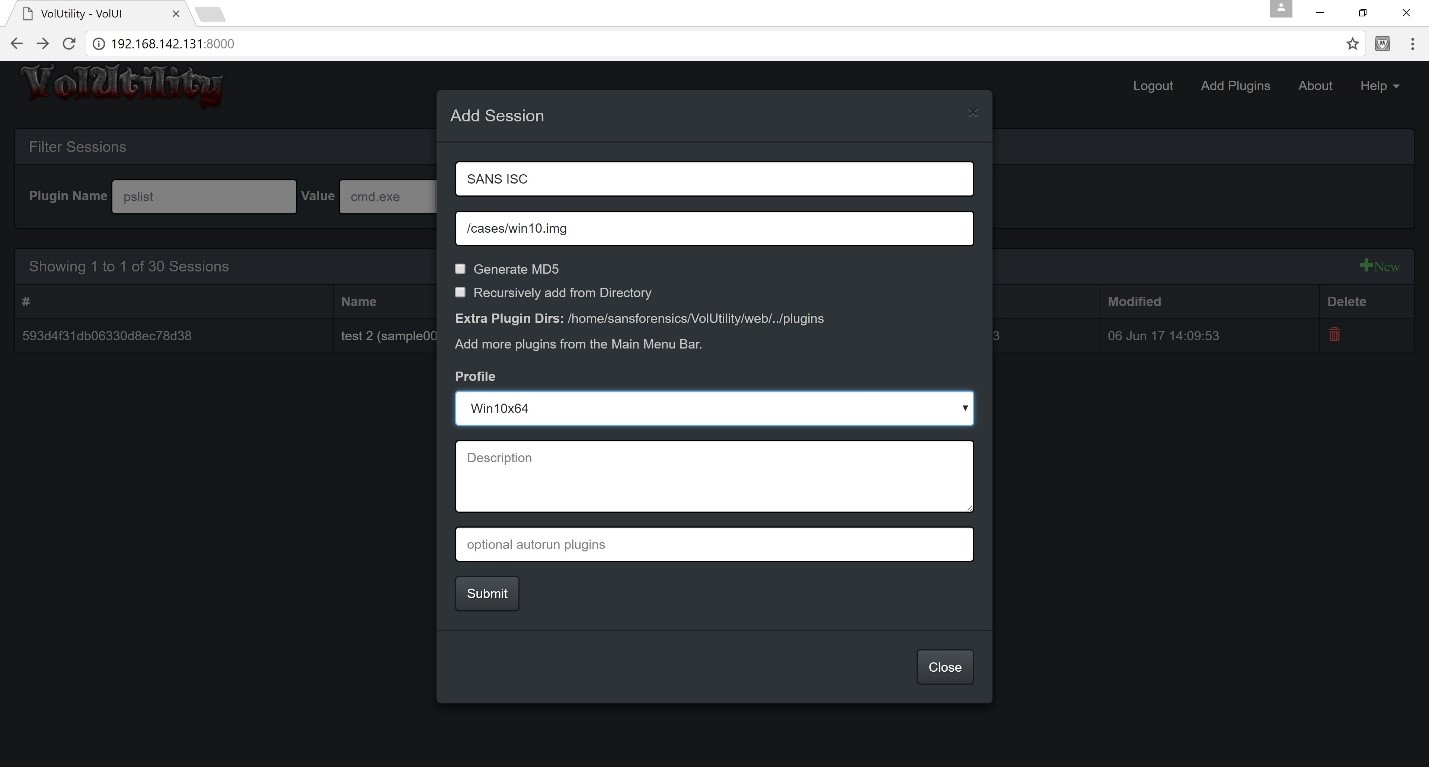
Enter a name for the session and the location of the memory image ,for the profile you can either specify it or you can choose autodetect, then click on submit button :
You have to wait for few minutest till it finishes from processing the image, once it finished the status will change to “Complete”
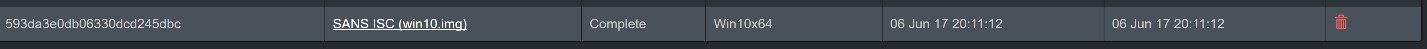
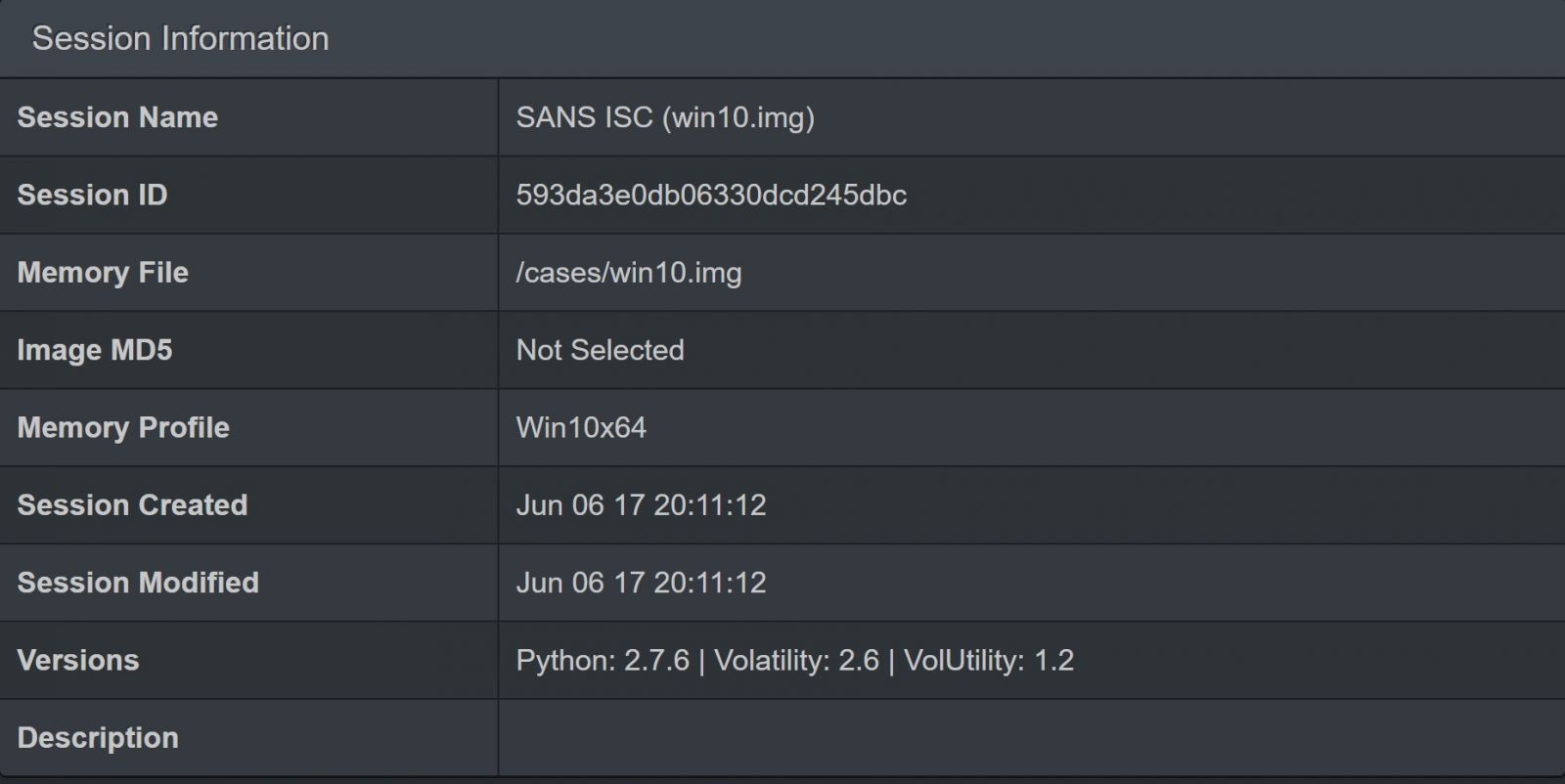
To examine the image click on the session name , in this the dairy it’s “SANS ISC” . Once you click on the session it will take you to a new page.
On the upper left corner there will be some information about the session:
Now let’s try some of the plugins :
To run a plug in you type the plugin name in the Filter Plugins text box and you can run it by clicking on the Play button .
And here is some sample outputs
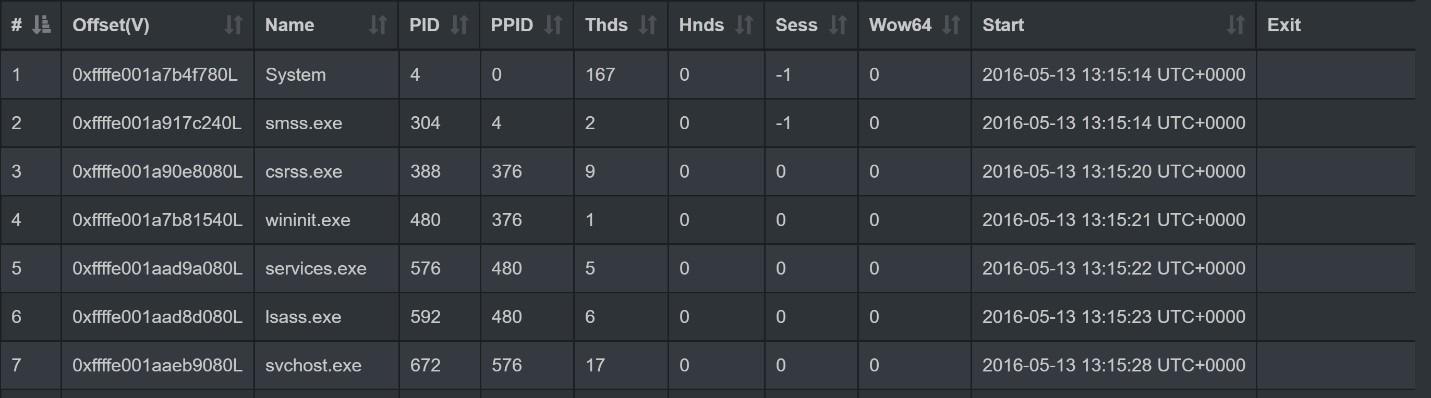
pslist
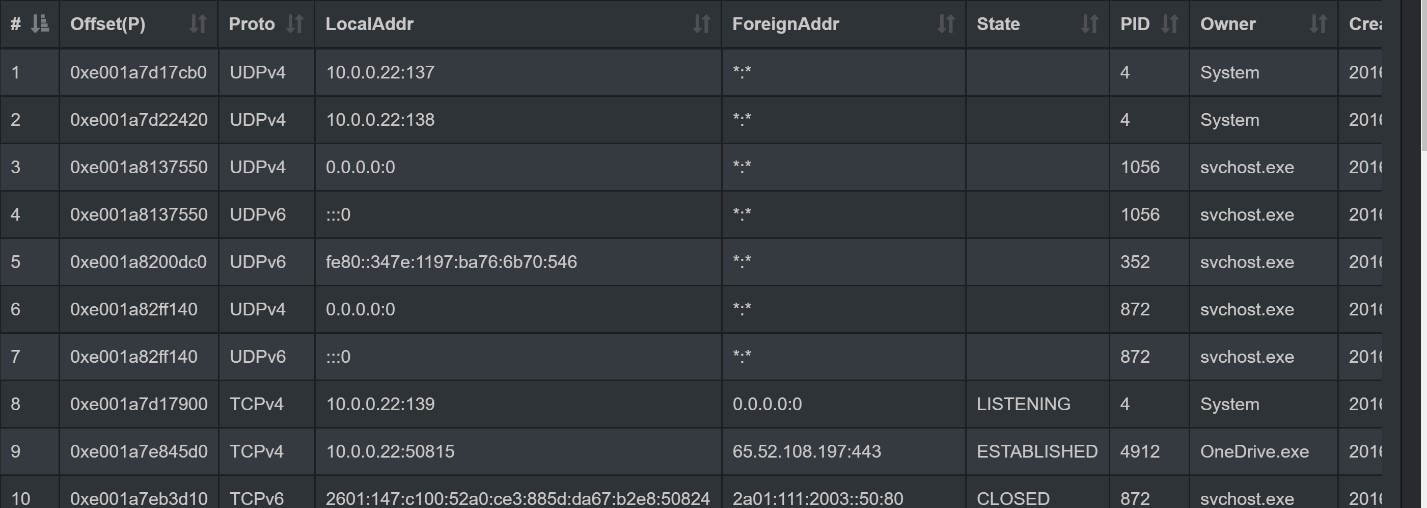
netscan
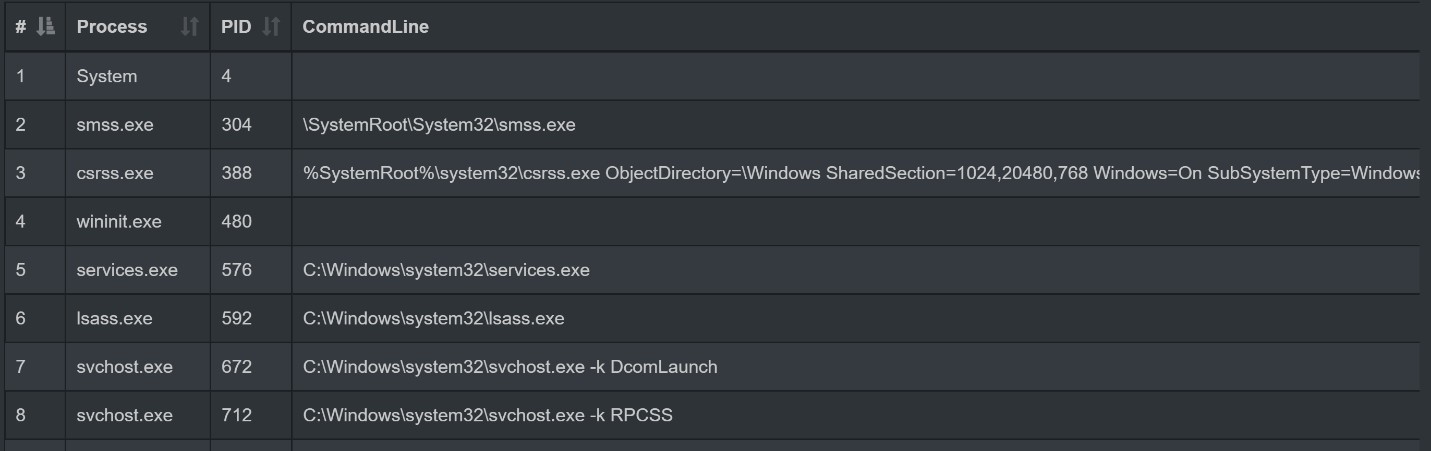
cmdline
One advantage of using VolUtility over using the command line is the possibility of exporting results to csv file, to do so click on down arrow next to the result
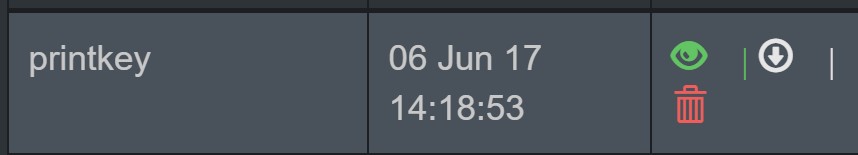
And you can of course filter your result using tools such as MS Excel.
_______________________________________________________
[1] https://github.com/kevthehermit/VolUtility/wiki
[2] http://holisticinfosec.blogspot.com/2016/04/toolsmith-115-volatility-acuity-with.html
[3] https://digital-forensics.sans.org/community/downloads


Comments