Scans for FPURL.xml: Reconnaissance or Not?
A reader has been reporting an increase in scans for "FPURL.xml" against their IIS server. The file did not exist in this case, and the server returned a 404 error. Checking our honeypots, we found little to no requests for this URL. But our honeypots are currently not emulating IIS servers. These scans have been hitting IIS servers for a while, according to some other reports I found.
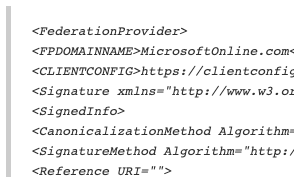
FPURL.xml is used as part of Microsoft's federated identity system. It can be used to implement "Windows Hello for Business." With Windows Hello for business, users can authenticate to Azure AD using two-factor authentication, and you can leverage this authentication for your applications. A client taking advantage of this authentication mechanism will load FPURL.xml to learn the parameters needed to authenticate. Here is a typical FPURL.xml file:
(I abbreviated some of the Base64 encoded strings to make this more readable)
<FederationProvider> <FPDOMAINNAME>MicrosoftOnline.com</FPDOMAINNAME> <CLIENTCONFIG>https://clientconfig.microsoftonline-p.net</CLIENTCONFIG> <Signature xmlns="http://www.w3.org/2000/09/xmldsig#"> <SignedInfo> <CanonicalizationMethod Algorithm="http://www.w3.org/TR/2001/REC-xml-c14n-20010315"/> <SignatureMethod Algorithm="http://www.w3.org/2000/09/xmldsig#rsa-sha1"/> <Reference URI=""> <Transforms> <Transform Algorithm="http://www.w3.org/2000/09/xmldsig#enveloped-signature"/> </Transforms> <DigestMethod Algorithm="http://www.w3.org/2000/09/xmldsig#sha1"/> <DigestValue>7Dl3OtA9+LvTX7P6gpBbsMe70U4=</DigestValue> </Reference> </SignedInfo> <SignatureValue>hCHLON..5mTQ==</SignatureValue> <KeyInfo> <X509Data> <X509Certificate>MIIDBTCCAe2gAw...vMqm9ndL7</X509Certificate> </X509Data> </KeyInfo> </Signature> </FederationProvider>
The file describes a "Federation Provider" that can be used to authenticate. In this case, the Federation Provider is MicrosoftOnline.com, and the file describes algorithms and certificates to use.
This file has some reconnaissance value. An attacker may now, for example, know that they can phish users for MicrosoftOnline credentials to get access to the resource. It could also be used for simple fingerprinting. There is a possibility that some of the requests you see for this file are just caused by clients that check if you are supporting this authentication method.
If anybody has additional input on these scans: Please let me know below or via our contact page.
---
Johannes B. Ullrich, Ph.D. , Dean of Research, SANS Technology Institute
|


Comments