Performing network forensics with Dshell. Part 2: Decoder development process
Last Updated: 2016-06-01 21:40:24 UTC
by Manuel Humberto Santander Pelaez (Version: 1)
We saw in part 1 how useful dshell can be. Let's talk about the decoder development process. You can develop the following decoder types:
- PacketDecoder: This type of decoder is able to look for specific packet information in a live capture or PCAP file and then show it to the user in a customized way.
- SessionDecoder: This type of decoder is able to get information from a complete protocol session, from the initial connection to the end of the session.
Dshell has the following classes that can be used to develop the decoders:
- dfile: Dshell class to handle file functions, wheter files are on memory or disk.
- dnsdecoder: Dshell intermediate class used to support DNS-based decoders
- dshell: Base class used to initialize the decoder to work in the framework. You can choose to use IPDecoder, IP6Decoder, UDPDecoder, UDP6Decoder, TCPDecoder, TCP6Decoder,Data, Packet, Connection or Blob.
- httpdecoder: Dshell intermediate class used to support HTTP-based decoders
- util: Dshell class providing useful functions like decode_base64 to decode base64 strings, printableText to print just ASCII-printable chars to the screen, printableUnicode to print unicode text without the control characters, hexPlusAscii to return hex dump in a two-column presentation for binary input, URLDataToParameterDict that parses URL format string, strtok to tokenize a string as used in C and xorStringDecode used to decode xor from string char.
- smbdecoder: This decoder extend dshell.TCPDecoder to handle SMB Message Requests/Responses.
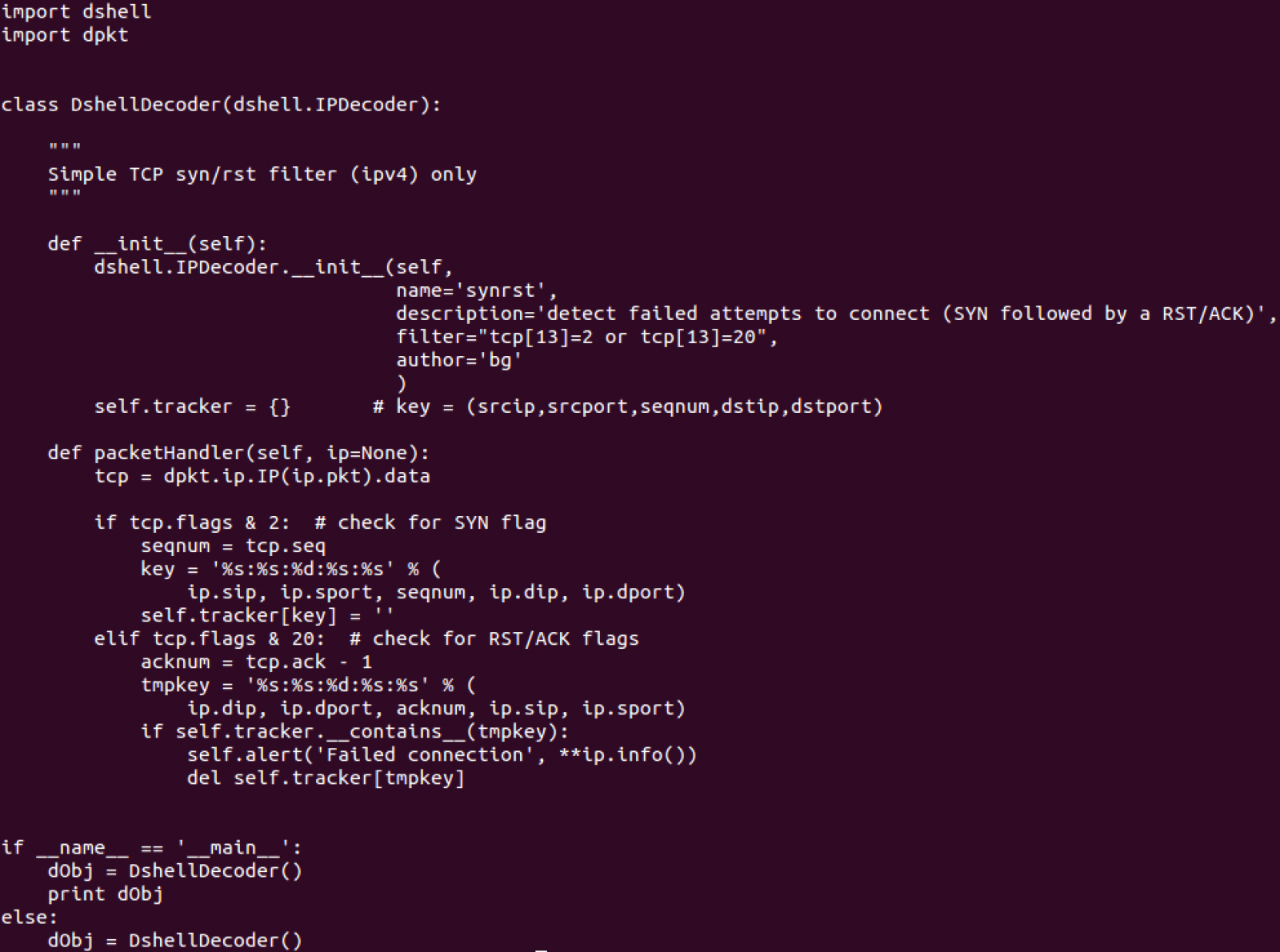
Let's see an example of a simple decoder, which uses dpkt library as well:
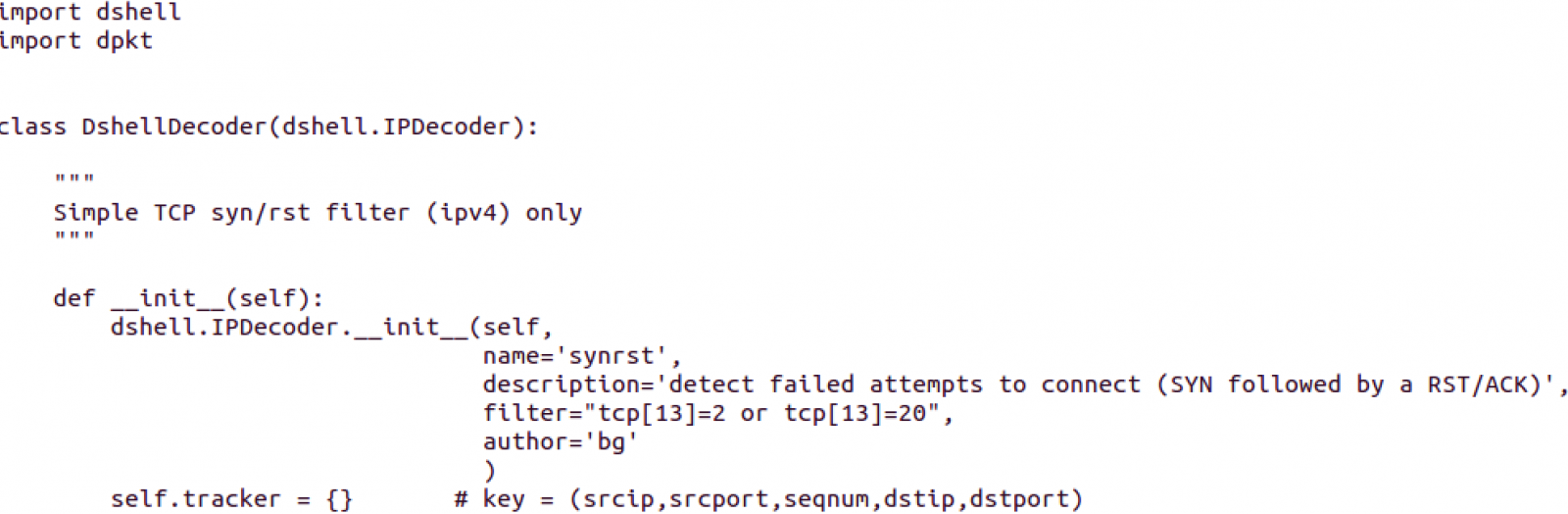
This looks like a packet decoder, using the base definition of IPDecoder contained in the Dshell class.
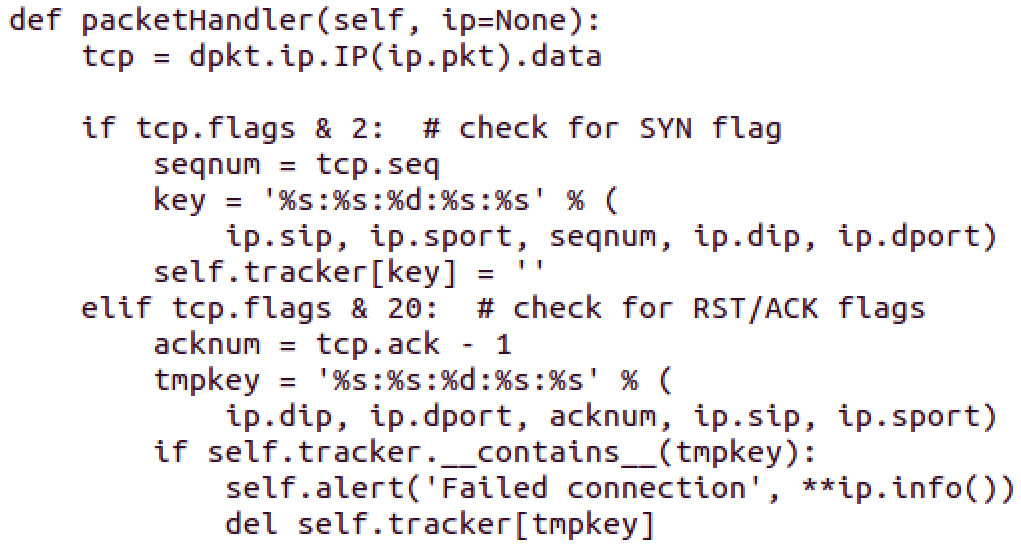
This function is part of all Packet Decoders. In this case, the dpkt library is used to dissect the IP packet to get just the TCP Header into the tcp variable. After that:
- If SYN flag is set, the source port, destination port, source IP, destination IP and sequence number are printed
- If not, if RST/ACK flags are set, the source port, destination port, source IP, destination IP and sequence number are printed
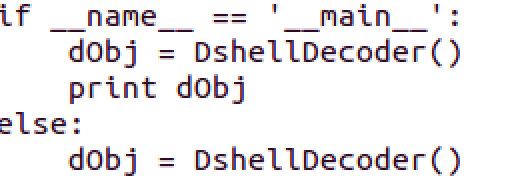
Dshell is instantiated. The whole code looks like this:
You can find this and other examples inside the decoders directory of Dshell.
Manuel Humberto Santander Peláez
SANS Internet Storm Center - Handler
Twitter: @manuelsantander
Web:http://manuel.santander.name
e-mail: msantand at isc dot sans dot org

Comments