Are typos still relevant as an indicator of phishing?
I was recently asked by a customer whether it still makes sense to cover “typos” as a potential indicator that an e-mail message may be malicious in the context of security awareness courses.
One might not expect typos to be relevant anymore, given the prevalence of automated language proofing solutions and the availability of modern LLMs, which threat actors may avail themselves of, coupled with advanced capabilities of modern security solutions used to automatically identify and filter out spam and malicious messages… Nevertheless, the truth is that although the aforementioned indicator may not be as useful as it once was, it may still point a recipient in the right direction.
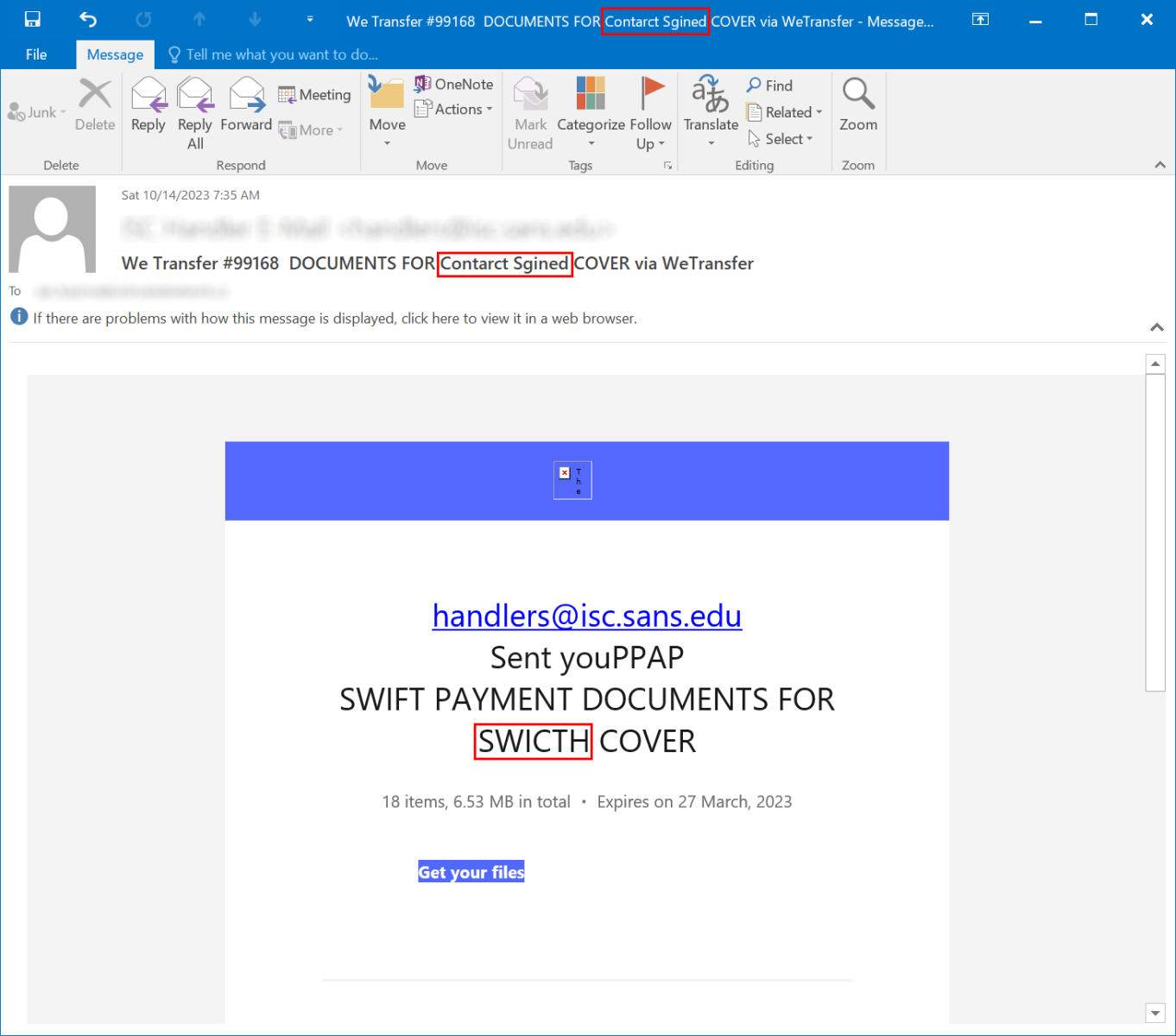
One good example of why this is so was provided by a phishing campaign we saw last week, when several messages, which were trying to masquerade as e-mails from the WeTransfer service, were delivered to our ISC inbox.
As you may see, there were two typos in the subject of the message alone, followed by another one in the body. Whether these were intentional (which would not be unheard of) or not, they show quite well that we are still not at a point when typos would become completely irrelevant when it comes to identification of potential phishing messages.
While one would – of course – hope that messages such as these would be correctly identified as malicious by any e-mail security solution worthy of the name, it remains true that some organizations (especially in the SMB space and in less developed countries) as well as many smaller “freemail” providers don’t necessarily use any such solutions,
One last thing which should be noted is that the “Get your files” link pointed to a URL located in the IPFS system, which – given how prevalent its use in phishing has become[1] – may be another good candidate for a short mention in the context of any security awareness course…
[1] https://www.trendmicro.com/vinfo/us/security/news/cybercrime-and-digital-threats/ipfs-a-new-data-frontier-or-a-new-cybercriminal-hideout
-----------
Jan Kopriva
@jk0pr
Nettles Consulting


Comments
Rien
Oct 16th 2023
2 years ago
Ian B
Oct 17th 2023
2 years ago