web3 phishing via self-customizing landing pages
You may not quite understand what "web3" is all about (I do not claim to do so), but it appears phishers may already use it. At least a particular web3 platform, "Skynet," aka "siasky.net," is already being abused. [FWIW: the page was reported to [email protected]]
The platform is pretty much a free file hosting platform. You upload an HTML file, which will display at a particular "slasky.net" URL. Like all similar file hosting platforms, it is ready to be abused by phishing scams.
Aside from being hosted on this newish platform, the JavaScript used to implement the phishing page is interesting. Not only does it customize the login dialog with the company logo, but it also replaces the entire page with a screenshot of the domain homepage.
Here is what the phishing page looks like if I append my "[email protected]" email address to the URL
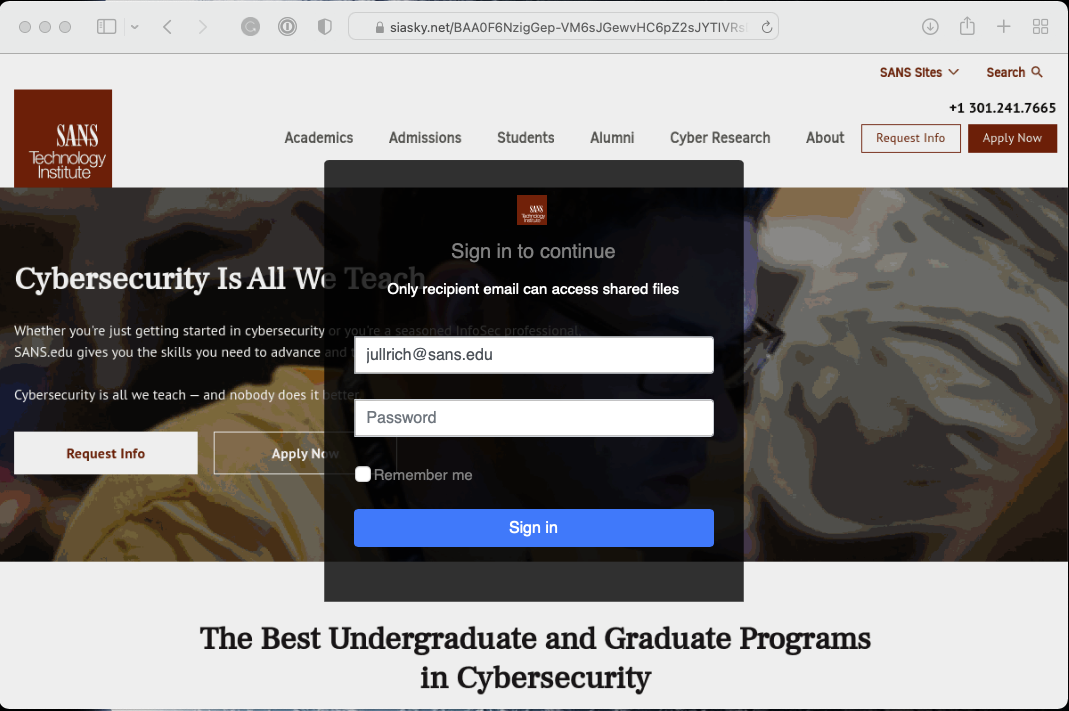
The JavaScript delivered by the site first attempts to disable some fo the context menu actions to prevent simple "view-source attacks". The, it uses the website screen shot generator at thum.io. Thum.io offers free accounts, but the JavaScript did include an API key (reported to thum.io) so this phishing site may have used a paid account. The logo is retrieved from logo.clearbit.com using the simple free service without any authentication tokens.
var ind=my_email.indexOf("@");
var my_slice=my_email.substr((ind+1));
var mainPage = 'https://'+my_slice;
var sv = my_slice;
var image = "url('https://image.thum.io/get/auth/53562-77e4da5126dd25414aacf01ccad53fff/width/1200/https://"+sv;"')"
$("#logoimg").attr("src", "https://logo.clearbit.com/"+mainPage);
document.body.style.backgroundImage = image;
Any data collected by the login form is then posted to https://cryptoglobalinvestment.net/obinna/New.php . The domain "cryptoglobalinvestment.net" redirects to blockchain.com. I doubt that the domain is related to blockchain.com. cryptoglobalinvestment.net is interestingly not using anonymized registration data. The email used to register it "[email protected]" is also used for a few other domain names that are currently not reachable. For example 1stalliancecredit.com.
For the first two attempts, the site will return a password error. On the third attempt, it will redirect the user to email.[user domain] in an attempt to direct the user to a likely webmail server.
Phishing URL: https [:] //siasky [.] net/BAA0F6NzigGep-VM6sJGewvHC6pZ2sJYTIVRsDYA4_QUVA#[email protected]
---
Johannes B. Ullrich, Ph.D. , Dean of Research, SANS.edu
Twitter|


Comments
Your article mentions sLasky dot net as the site being used but siasky dot net (which seems to be the correct site) in the abuse email address.
Also, good morning!
Dave
Anonymous
Feb 7th 2022
4 years ago
With the companies belief on decentralization / Web3.0, do you think that there's any good in reporting phishing abused on these platforms?
Anonymous
Feb 7th 2022
4 years ago
siasky.net does have an abuse reporting contact. I reported it, but so far the page is still up (about 5 hrs or so later). Not sure if it is right to call it web3, maybe it is more web2.5 ;-).
Anonymous
Feb 7th 2022
4 years ago