Using RITA for Threat Analysis
I installed and tested this open source framework called Real Intelligence Threat Analytics (RITA) that was recently updated against my BRO logs. It supports some interesting features such as: [2]
Beaconing Detection
DNS Tunneling Detection
Blocklist Checking
URL Length Analysis
Scanning Detection
"This open source project, born from Black Hills Information Security, is now developed, funded and supported by Active CounterMeasures". A full description of RITA's capabilities and the code is available here.
I used the automated script (install.sh) with CentOS 7 which I download from here. The installation is straight forward and it verified my setup to make sure everything is installed on my box.
After the installation, I edited the configuration file and changed the default (/etc/rita/config.yaml) and confirmed the following:
- RitaLogPath: /var/lib/rita/logs <- Default RITA logs location
- ImportDirectory: /data/bro/logs/ <- Default BRO logs
- DBRoot: "bro" <- I changed the default RITA to bro (or anything you like)
Next I got a Google Safe Browsing API key [4] and followed the API setup instructions here and added it to the rita config file.
- APIKey: "" <- Added my Google SafeBrowsing key
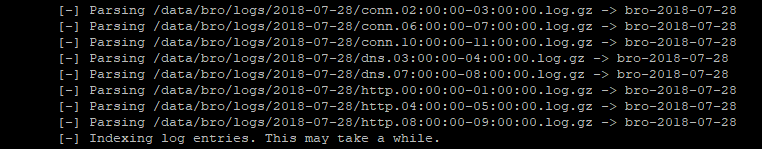
My next step is to import my Bro logs into the database with the command:
- rita import <- From default config file logs
If you want to import a single day, use the following command:
- rita import /data/bro/logs/2018-07-27 bro-2018-07-27
Show what is available now:
- rita show-databases
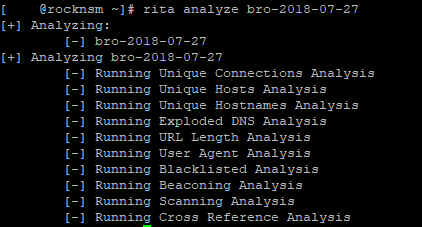
Now we can analyze a day of Bro traffic as follow:
- rita analyze bro-2018-07-27
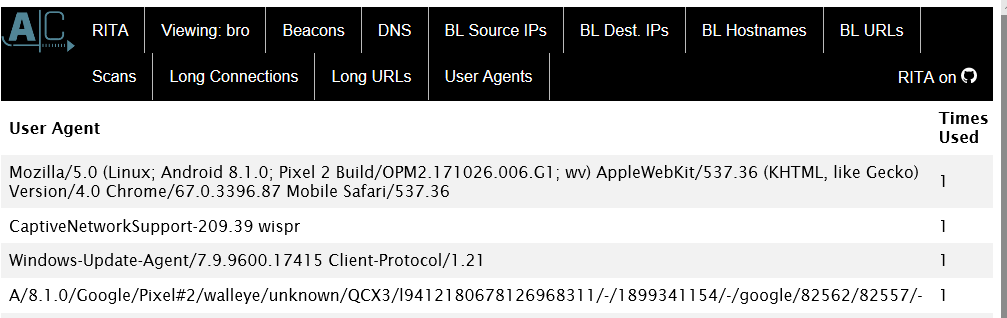
Last step, lets create a web report that can be easily viewed with a browser:
- rita html-report bro-2018-07-27
[guy@rocknsm ~]# rita html-report bro-2018-07-27
[-] Writing: /home/guy/bro-2018-07-271/bro-2018-07-27
[-] Wrote outputs, check /home/guy/bro-2018-07-27 for files
If at some point you want to delete a day of data, use the following command in your home directory:
- rita delete-database bro-2018-07-27
If you are interested to see this tool in action, check out John Strand's YouTube video here.
[1] https://www.activecountermeasures.com
[2] https://github.com/activecm/rita
[3] https://github.com/activecm/rita/releases/tag/v1.0.1
[4] https://console.cloud.google.com
[5] https://www.blackhillsinfosec.com/projects/rita/
-----------
Guy Bruneau IPSS Inc.
Twitter: GuyBruneau
gbruneau at isc dot sans dot edu


Comments
Allowing additional input formats would be great.
A part from that I really liked the article. Thanks for sharing.
Anonymous
Jul 30th 2018
7 years ago
Anonymous
Jul 30th 2018
7 years ago