Checking out the new Petya variant
This is a follow-up from our previous diary about today's ransomware attacks using the new Petya variant. So far, we've noted:
- Several hundred more tweets about today's attack can be found on Twitter using #petya.
- The new Petya variant appears to be using the MS17-010 Eternal Blue exploit to propagate.
- Others claim the new variant uses WMIC to propagate
- Still no official word on the initial infection vector in today's attacks.
- People everywhere are saying today's activity is similar to last month's WannaCry ransomware attacks.
Samples of the new Petya variant are DLL files. So far, we've confirmed the following two SHA256 file hashes are the new variant:
- 027cc450ef5f8c5f653329641ec1fed91f694e0d229928963b30f6b0d7d3a745
- 64b0b58a2c030c77fdb2b537b2fcc4af432bc55ffb36599a31d418c7c69e94b1
Examining the new Petya variant
Petya is a ransomware family that works by modifying the infected Windows system's Master Boot Record (MBR). Using rundll32.exe with #1 as the DLL entry point, I was able to infect hosts in my lab with the above two DLL samples. The reboot didn't occur right away. However, when it did, my infected host did a CHKDSK after rebooting.
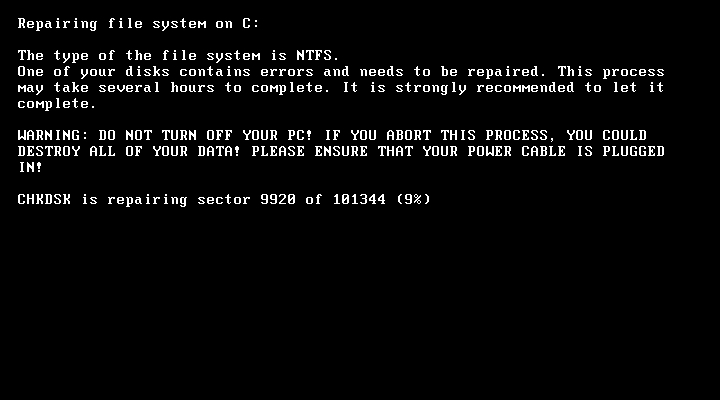
Shown above: An infected host immediately after rebooting.
After CHKDSK finished, the infected Windows host's modified MBR prevented Windows from loading. Instead, the infected host displayed a ransom message.
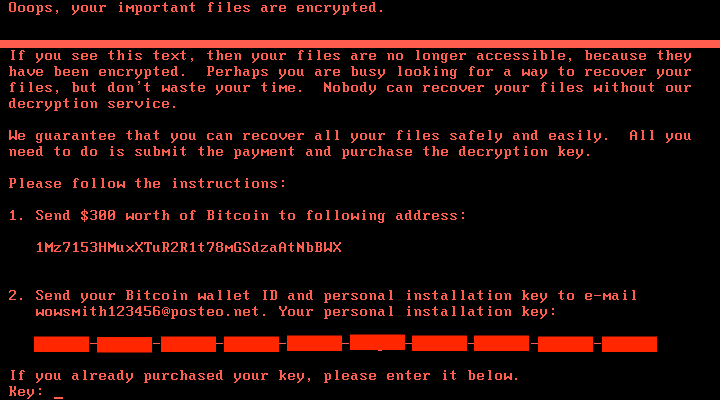
Shown above: The ransom note from a compromised system.
Samples of the new Petya variant appear to have WMI command-line (WMIC) functionality. Others have confirmed this variant spreads over Windows SMB and is reportedly using the EternalBlue exploit tool, which exploits CVE-2017-0144 and was originally released by the Shadow Brokers group in April 2017. My infected Windows hosts immediately generated TCP traffic on port 445 and did ARP requests for local network hosts.
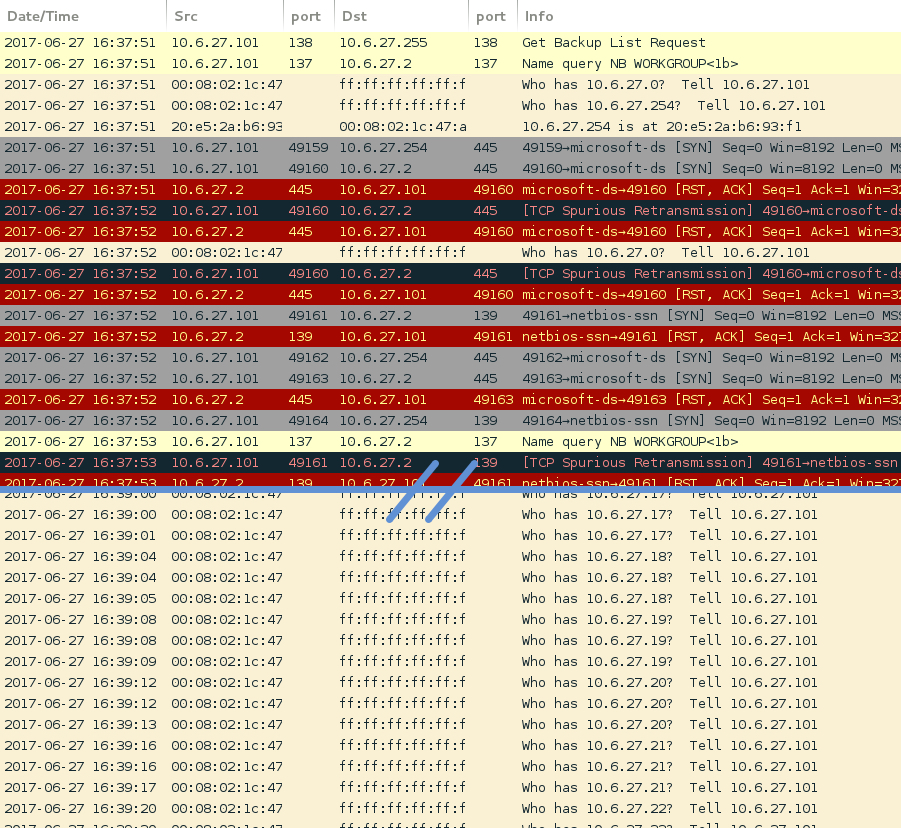
Shown above: Some of the traffic noted in my lab environment.
Keep in mind this is a new variant of Petya ransomware. I'm still seeing samples of the regular Petya ransomware submitted to places like VirusTotal and other locations. From what we can tell, those previous versions of Petya are not related to today's attacks.
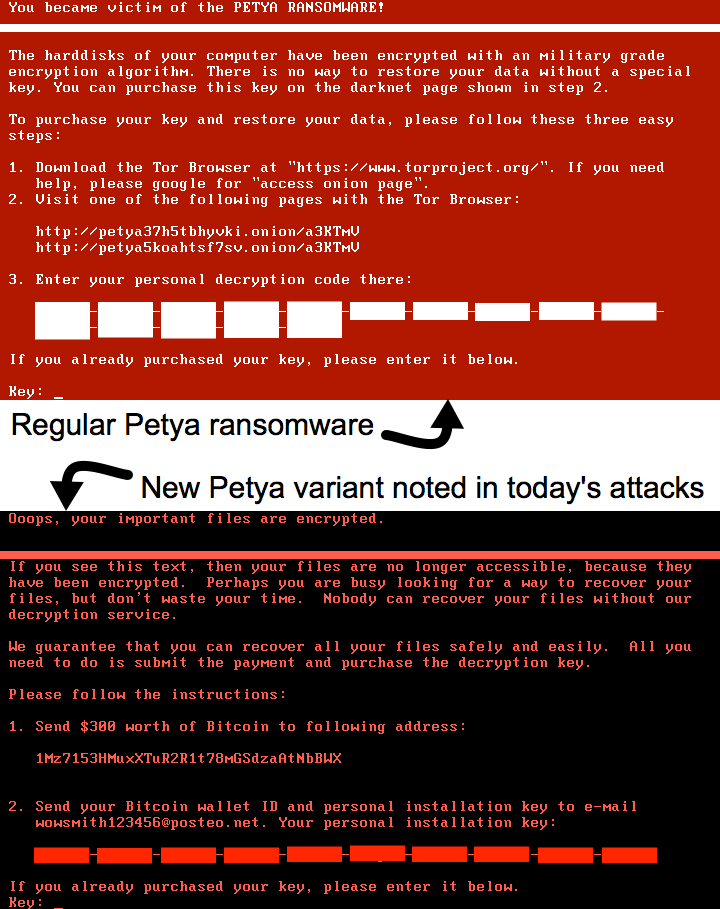
Shown above: Difference in ransomware notes between the old and new Petya variants.
New Petya variant ransom message
Ooops, your important files are encrypted.
If you see this text, then your files are no longer accessible, because they have been encrypted. Perhaps you are busy looking for a way to recover your files, but don't waste your time. Nobody can recover your files without our decryption service.
We guarantee that you can recover all your files safely and easily. All you need to do is submit the payment and purchase the decryption key.
Please follow the instructions:
1. Send $300 worth of Bitcoin to the following address:
1Mz7153HMuxXTuR2R1t78mGSdzaAtNbBWX
2. Send your Bitcoin walled ID and personal installation key to e-mail [email protected]. Your personal installation key:
012345-6789ab-cdefgh-ijklmn-opqrst-uvwxyz-ABCDEF-GHIJKL-MNOPQR-STUVWX
If you already purchased your key, please enter it below.
Key:
More reports about the new Petya variant
- Bleeping Computer: WannaCry Déjà Vu: Petya Ransomware Outbreak Wreaking Havoc Across the Globe
- The Hacker News: Petya Ransomware Spreading Rapidly Worldwide, Just Like WannaCry
- Reuters: Petya ransomware virus is back amid cyber attack: Swiss agency
- Palo Alto Networks Blog: Threat Brief: Petya ransomware


Comments
https://gist.github.com/vulnersCom/65fe44d27d29d7a5de4c176baba45759
Anonymous
Jun 27th 2017
8 years ago
Anonymous
Jun 27th 2017
8 years ago
Anonymous
Jun 27th 2017
8 years ago
https://www.bleepingcomputer.com/news/security/vaccine-not-killswitch-found-for-petya-notpetya-ransomware-outbreak/
Anonymous
Jun 28th 2017
8 years ago
https://nakedsecurity.sophos.com/2017/06/28/deconstructing-petya-how-it-spreads-and-how-to-fight-back/
Anonymous
Jun 28th 2017
8 years ago
Anonymous
Jun 28th 2017
8 years ago