Malicious spam - Subject: RE: Bill
Introduction
Earlier today (Wednesday 2015-11-25), one of our readers notified the ISC of malicious spam (malspam) with a Word document designed to infect a Windows computer with malware. I found examples of the malspam and looked into it. Word documents from this particular campaign will download Pony malware to infect a Windows computer with Vawtrak. This malspam was blocked by our spam filters, but others might see it, so I'm posting the information in a diary.
Thanks for the heads up, Travis!
The emails
The emails spoof your company name (or whatever domain you're using for your email address), and they have a Microsoft Word document as an attachment. The one's I've found have all been plain-text.
From: "accounting@[your company].com"
Reply-To: "accounting@[your company].com"
Date: Wednesday, 2015-11-25 at 09:37 CDT
To: [your email address]
Subject: Re: bill
This bill just came through and it has your name on it.
What is this about?
---
Este email está livre de vírus e malware porque a proteção avast! Antivirus está ativa.
https://www.avast.com/antivirus
Attachment: Bill.doc
The messages all have a notification at the bottom stating "This email is free of viruses and malware protection because the Avast! Antivirus is active." These antivirus messages were all in different languages, based on the host these emails were sent from.
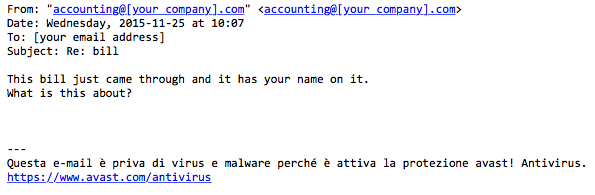
Shown above: Example of the malspam with a different language for the antivirus notification.
We saw this malspam come from senders at the following IP addresses:
- 2015-11-25 15:06 UTC - 85.246.96.111 (l13-96-111.dsl.telepac.pt)
- 2015-11-25 15:36 UTC - 178.253.170.155 (178-253-170-155.vdial.slovanet.sk)
- 2015-11-25 15:59 UTC - 188.250.234.94 (bl24-234-94.dsl.telepac.pt)
- 2015-11-25 16:14 UTC - 88.16.67.20 (20.Red-88-16-67.dynamicIP.rima-tde.net)
- 2015-11-25 16:26 UTC - 82.54.254.143 (host143-254-dynamic.54-82-r.retail.telecomitalia.it)
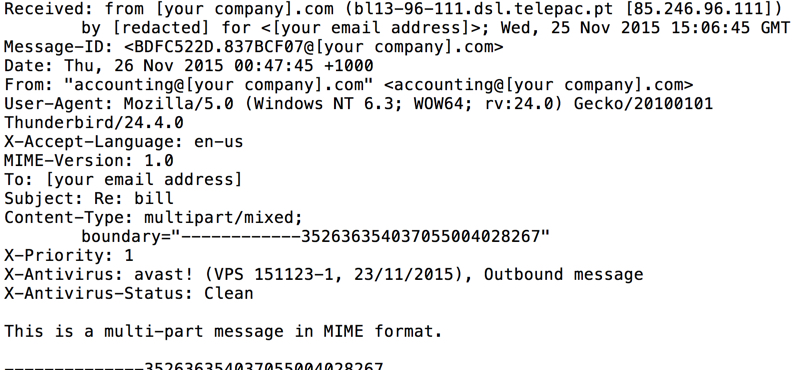
Shown above: An example of the email headers from this malspam.
The attachment
The attachment is a Microsoft Word document with malicious macros. The sample had already been submitted to VirusTotal (link), but it only had a 1 / 55 detection rate when I first checked. I enabled the document's macros in a controlled environment to infect a Windows host.
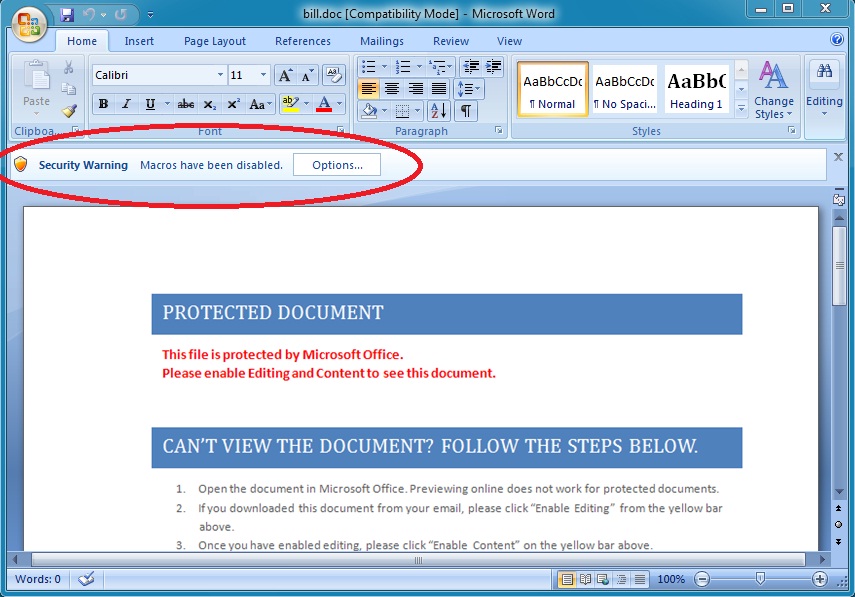
Shown above: The malicious document opened in Word 2007.
The infection traffic
Infecting a host with the malware generated traffic that matched a Pony downloader infecting a Windows computer with Vawtrak.
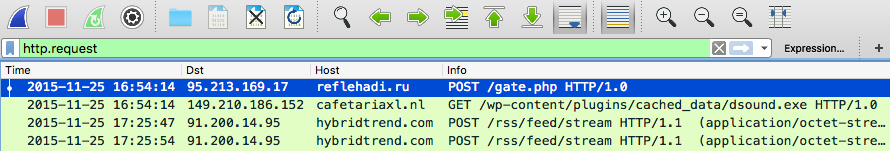
Shown above: A pcap of the infection traffic filtered in Wireshark by HTTP request.
I reviewed the infection traffic using Security Onion with the EmergingThreats Pro signature set. I saw alerts for Fareit/Pony and Vawtrak.
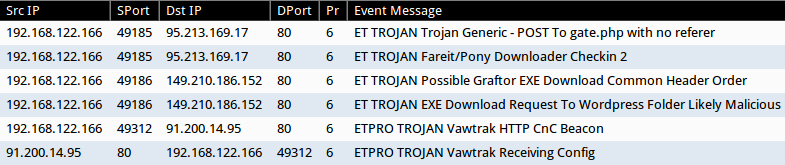
Shown above: Some of the alerts in Sguil on Security Onion.
The following IP addresses and domain names were associated with this Pony/Vawtrak infection:
- 95.213.169.17 - reflahadi.ru
- 149.210.186.152 - cafetariaxl.nl
- 46.161.1.172 - castuning.ru
- 91.200.14.95 - hybridtrend.com
- 81.177.22.179 - 81.177.22.179
Malware and artifacts from the infected host
The Word document caused the following artifacts to appear in the infected user's AppData\Local\Temp directory:
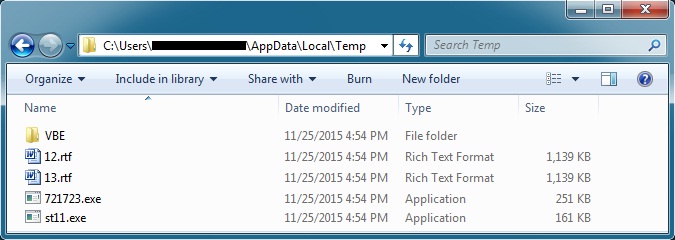
Shown above: Artifacts from the infected user's AppData/Local/Temp directory.
- 12.rtf - MD5 hash: 6dfd5c9274b1ecb1bad095cb8f00100e - VirusTotal link
- 13.rft - MD5 hash: f08febf78a641505c13746fd38ed09c3 - VirusTotal link
- 721723.exe (also HadFeqt.exe) - MD5 hash: a054dfe5575c59f6bd96fc395041eb93 - VirusTotal link
- st11.exe - MD5 hash: bd86e1a8a35b12841ee6694dcc607cd0 - VirusTotal link
Both st11.exe and 721723.exe deleted themselves shortly after appearing in the directory. st11.exe is the Pony downloader. 721723.exe is Vawtrack, which copied itself to another directory and updated the infected host's registry to remain persistent.
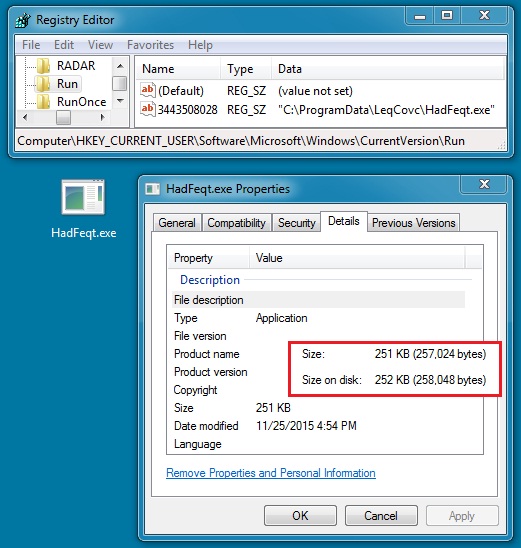
Shown above: The Vawtrak malware from this infection.
Final words
Malspam with a Word document that causes Pony to download more malware is not uncommon. It's just another example of the many types of malspam we see blocked by our spam filters on a daily basis.
Email examples, traffic, and malware from this diary can be found here.
Many thanks to our readers, who continue to notify us of suspicious activity!
---
Brad Duncan
Security Researcher at Rackspace
Blog: www.malware-traffic-analysis.net - Twitter: @malware_traffic


Comments
Anonymous
Nov 25th 2015
1 decade ago
Anonymous
Nov 25th 2015
1 decade ago
I'm new to the ISC, so I'm not sure if it would be of use, but if you guys want a copy of what I have, please let me know where to send it.
Anonymous
Nov 25th 2015
1 decade ago
You can always submit samples through our contact page at: https://isc.sans.edu/contact.html
We prefer .eml files for the spam samples. If you can only submit the malware, please let us know of the sender, subject, and Date/time at a minimum. If possible, you can always send us the email headers with the malware submission.
Thanks,
- Brad
Anonymous
Nov 25th 2015
1 decade ago
Such malware is MOSTLY HARMLESS ... its payload can't run if you setup your Windows properly!
See <http://mechbgon.com/srp/> and <http://home.arcor.de/skanthak/SAFER.html> for instructions!
Anonymous
Nov 26th 2015
1 decade ago
Do you mind if I use the pictures in this post as part of an internal education campaign?
Anonymous
Nov 26th 2015
1 decade ago
Sure thing! Just make sure to credit the source (the isc.sans.edu URL).
- Brad
Anonymous
Nov 27th 2015
1 decade ago
I saw a couple of days ago and IP reputation of originator was an established, well-known blacklisted..
Anonymous
Nov 29th 2015
1 decade ago