[GUEST DIARY] Tearing apart website fraud to see how it works.
[This is a Guest Diary by Joshua Nikolson, an ISC Intern and part of the SANS.edu Bachelor's degree in Applied Cybersecurity (BACS) program.]
Introduction
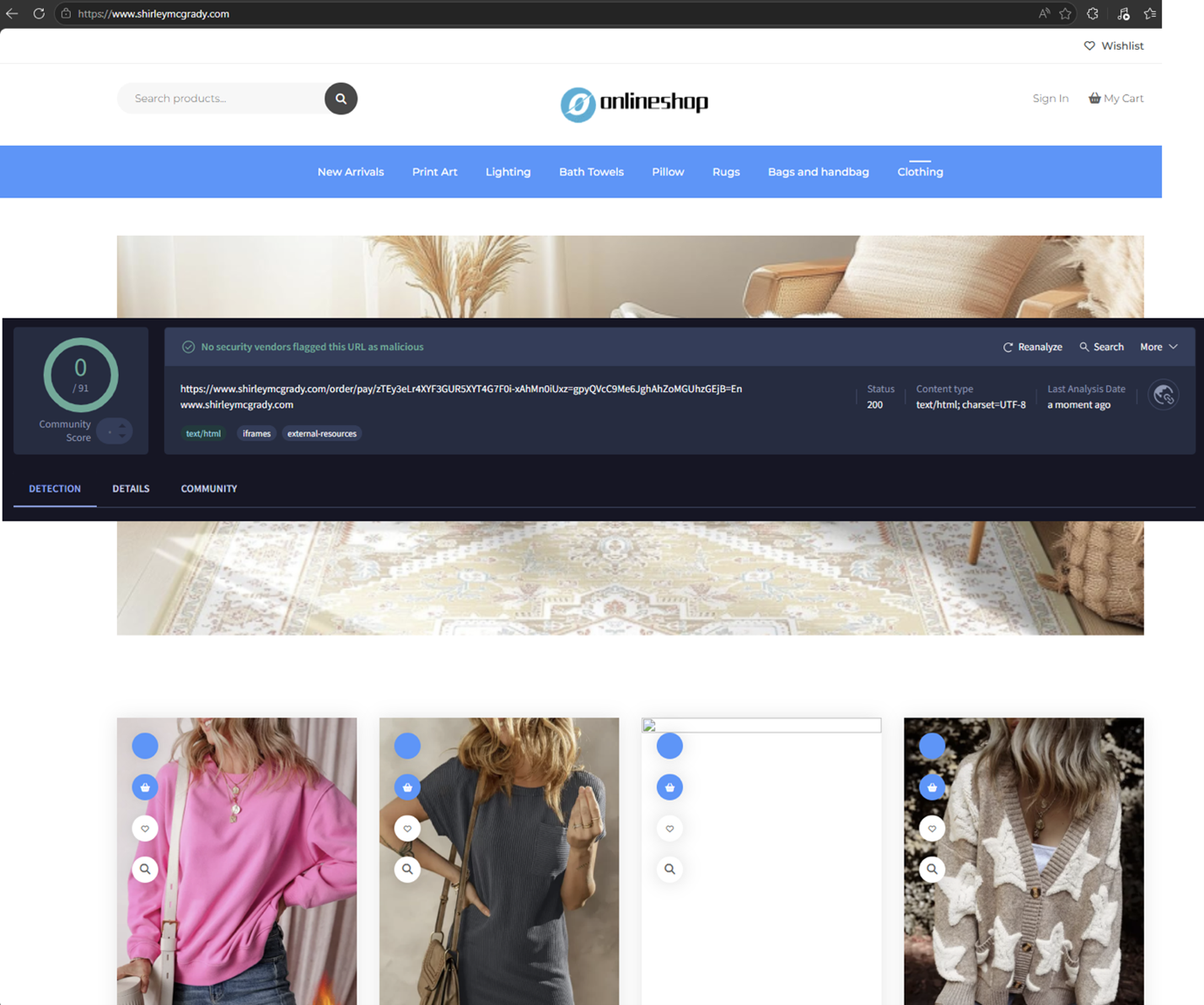
One day at work, a friend messaged me, “How do you check a website to see if it’s legit?” This friend recently received a phishing text message from a “bank”, and I figured he wanted to be careful and double-check. I told him to put the URL into VirusTotal but said that just because it may say it’s clean, that doesn’t mean it’s not malicious.
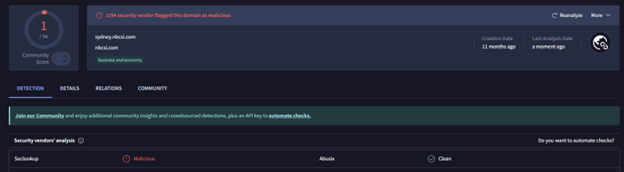
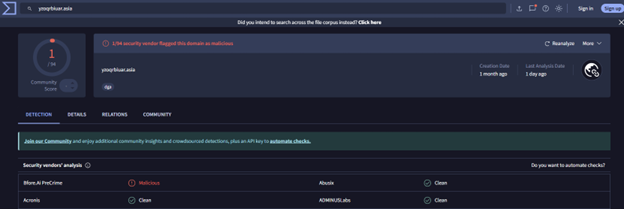
He sent me a screenshot of the VirusTotal page for the URL, with no detections and everything showing green. I took a moment to look at it a little more closely. The domain name was unusual, and right off the bat I could see it had been created in the last few months. As of now, it has one detection from a vendor. All domains mentioned in this blogpost will be listed in the Indicators of Compromise section at the end.
Going to the site, I could immediately tell that something was off about it. It was a secondhand marketplace that seemed to sell just about everything under the sun, with tons of listings in each category and items priced too good to be true. While the site had that “AI vibecoded feeling”, I wanted to give my friend something more concrete other than “don’t trust this site”.
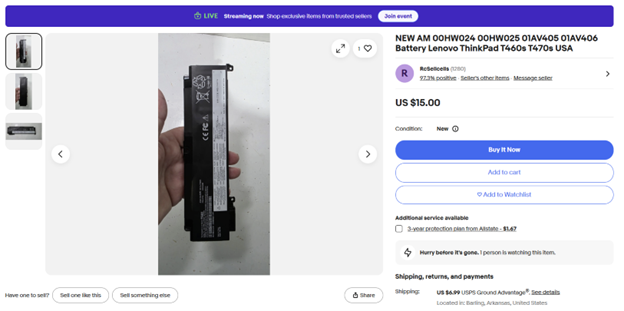
I decided to reverse image search one of the product images, a Lenovo ThinkPad battery replacement, and after some digging, I found an eBay listing with all the same product images and item descriptions. I did this for a few more of the site’s listings and came to the same result. I let my friend know, and he said, “Yeah, it looked too good to be true”.
Finding a Marketplace
I found this interesting and wanted to see if I could find something similar again. Today, it is trivial to use AI to mass-deploy these scams, and I wanted to see what would happen if I tried to buy something.
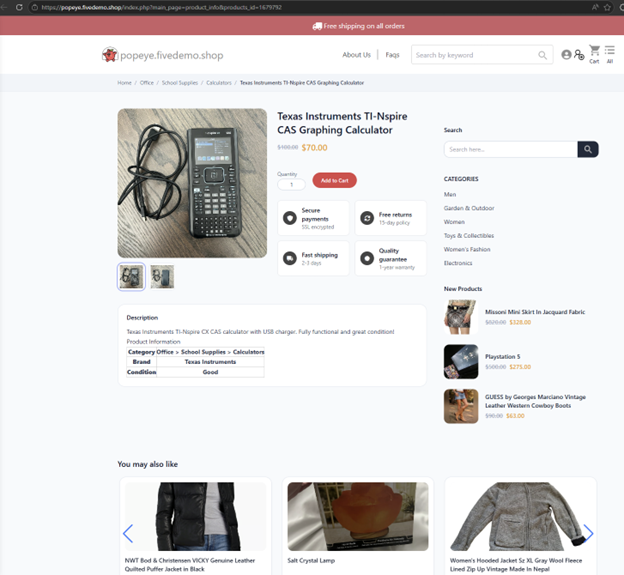
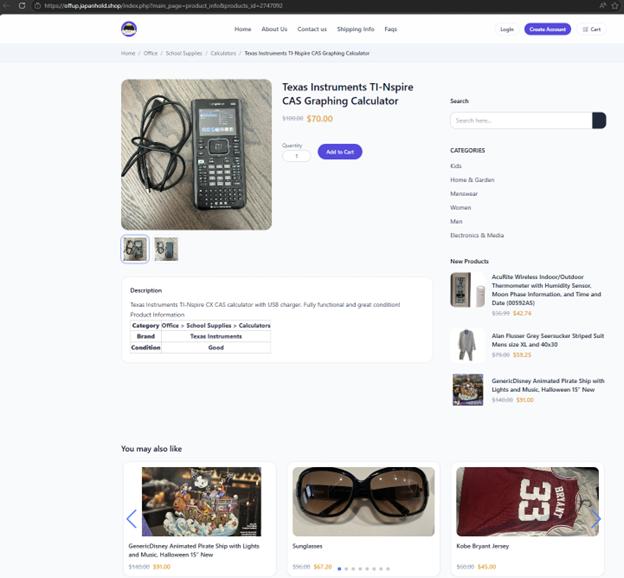
Let’s look up what my friend was originally looking for: a Texas Instruments TI-nSpire CAS calculator. Simply searching on Google and going to the second page, something pops out to me. Why is a driving school selling a calculator?
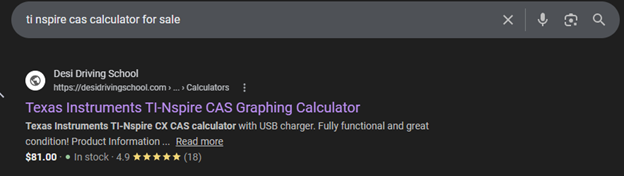
The search result link, hxxps://desidrivingschool[.]com/listing/164903741/ redirects to a marketplace where it is for sale:
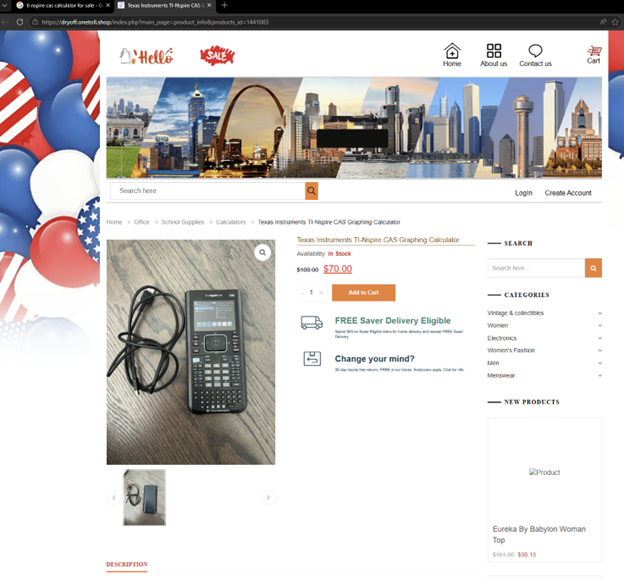
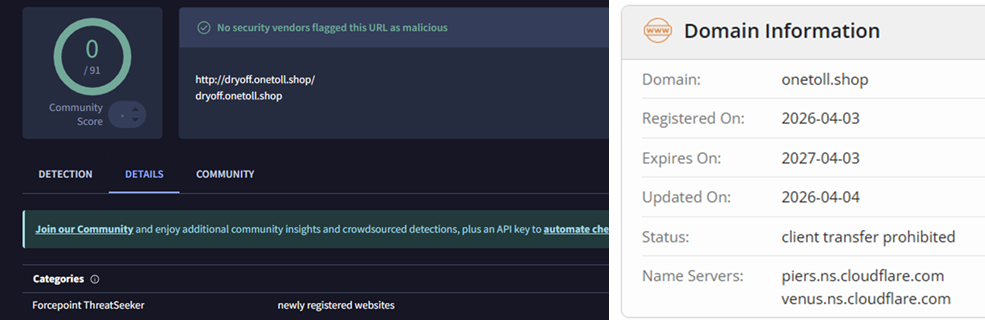
This domain looks suspicious on its own, and to add insult to injury, it was registered ~12 days ago on April 3rd, 2026:
What's happening here?
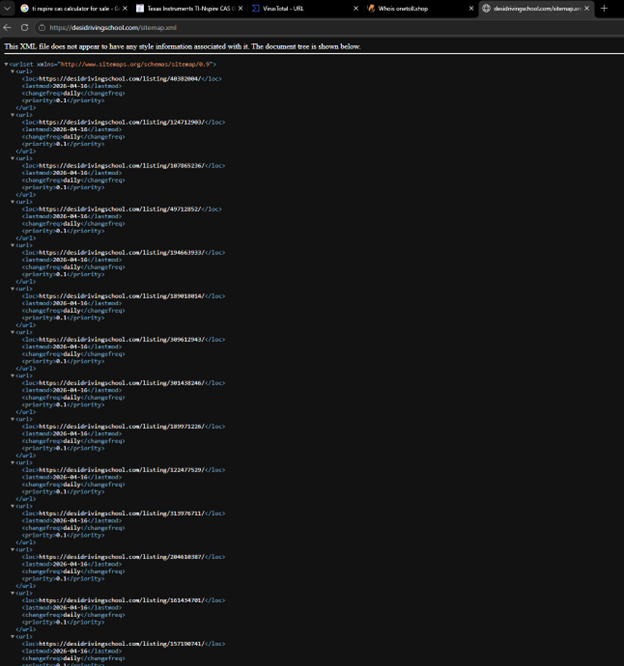
You may be asking why this Desi Driving School is showing up in the search results for this calculator? Good question. If you append “/sitemap.xml” to the URL, you can see tons of these listings that are meant to infiltrate the search results. This is a prime example of SEO poisoning, in which potential victims are lured through their shopping searches to these fake marketplaces.
Threat actors have previously used compromised WordPress sites as command-and-control infrastructure or to stage payloads, but this is being used as a distinct attack vector. Unfortunately, this website was likely compromised, whether through something like a malicious WordPress plugin or stolen credentials, and is now being used to drive traffic to this malicious marketplace:
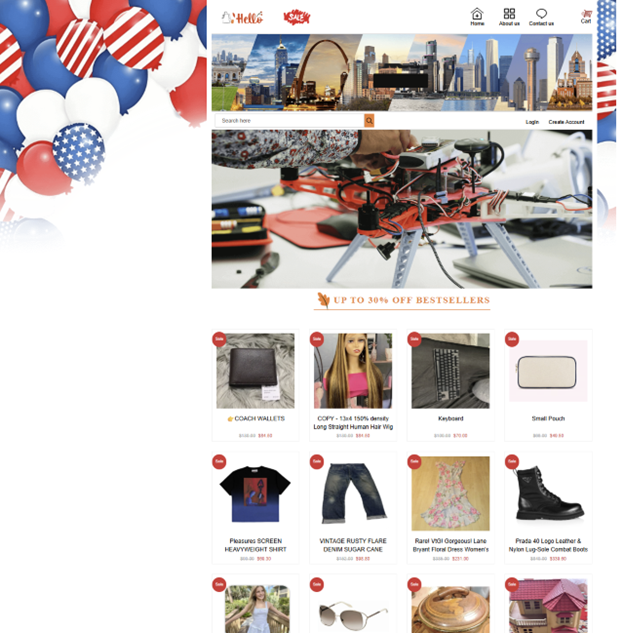
You can see the range of products that this site offers. They must have a good distribution network.
While reverse-image searching for images of the calculator, I found another similar posting on a different fake marketplace. Same images, same description and title, same exact setup with a redirect…

And another… with what looks like loads of other compromised sites being used.
You can endlessly find these sites by searching any description of a product listed with quotes in Google to find the real item that is being sold and copied from, such as this blazer:
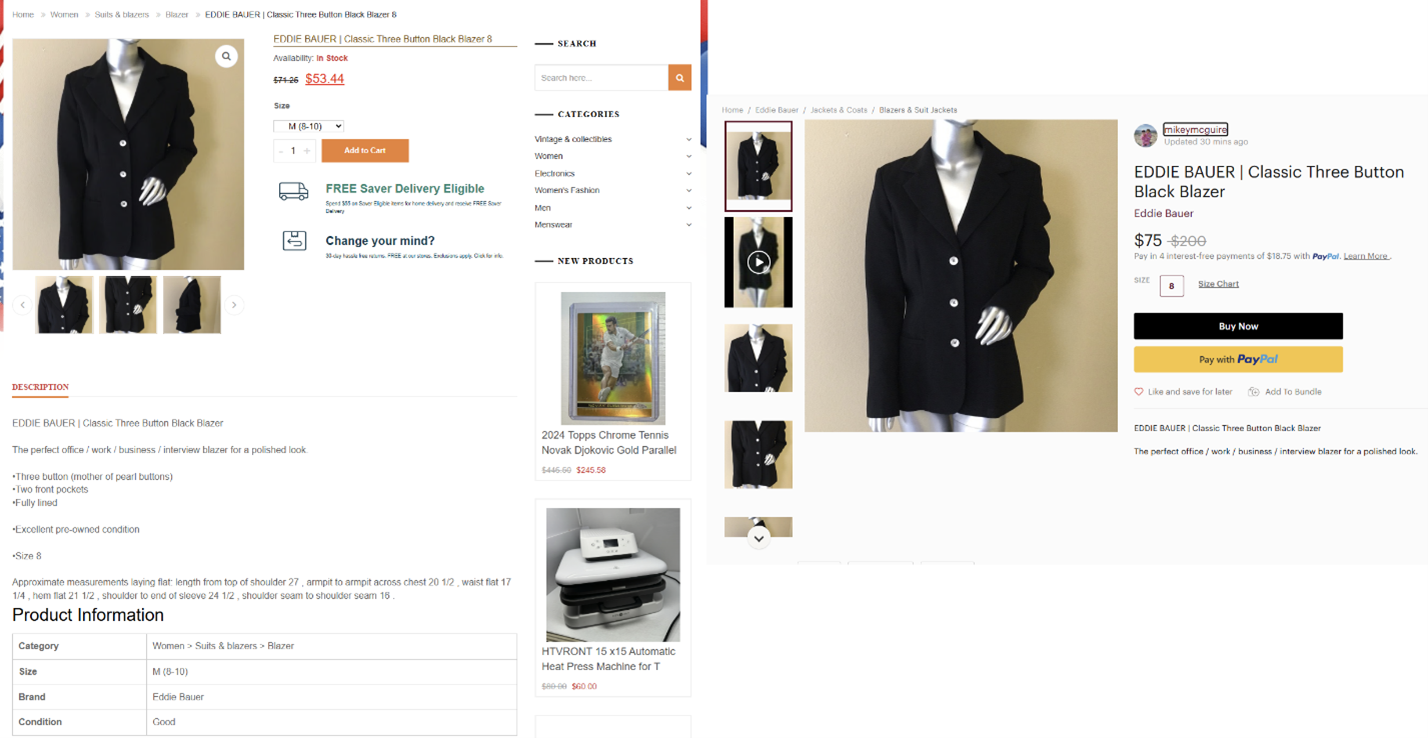
If the price was higher than the actual listing, you might think the scheme is just scraping listings, posting them at a higher price, then purchasing the cheaper item and shipping it. However, I do not think that is the case. Let’s try to buy this Eddie Bauer blazer with a fake identity and a fake debit card from Privacy.com and see what happens.
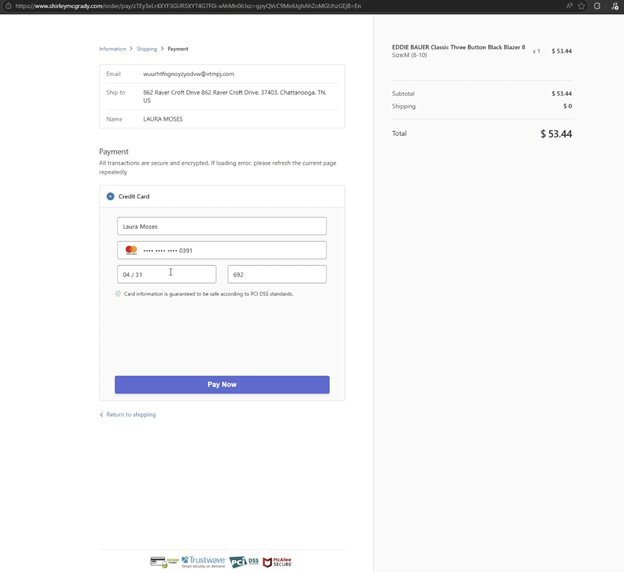
Right away, I can tell this checkout page is a replica of the Shopify checkout page and looks almost identical.
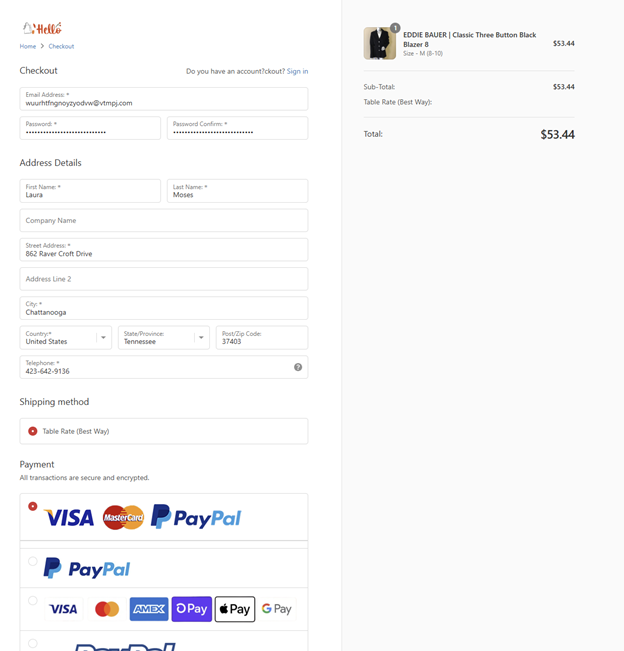
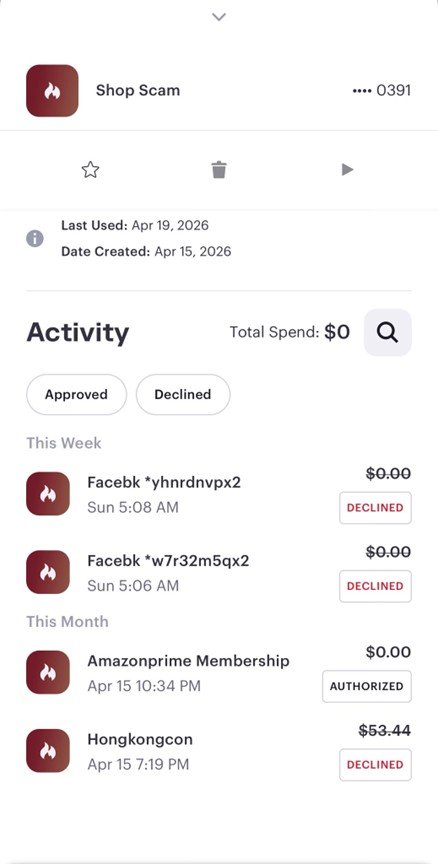
Choosing Mastercard, we’ll check out and pay now. Let’s prepare my fake card. Creating a temporary debit card with a $5 spending limit is extremely easy with Privacy.com, and I have my Mastercard ready.
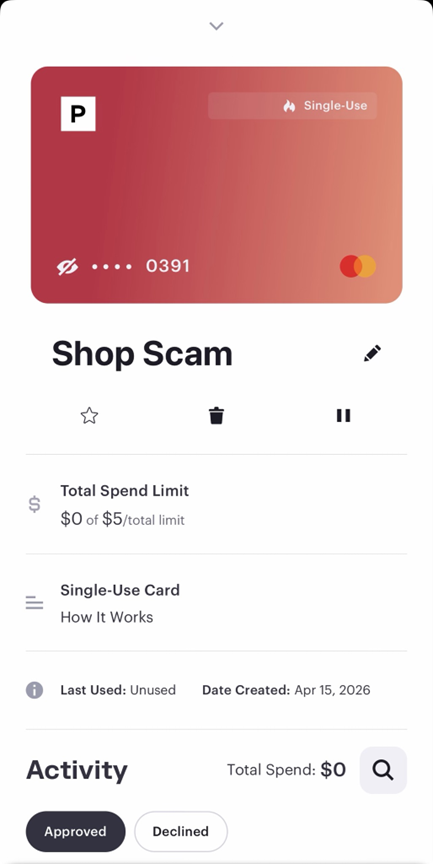
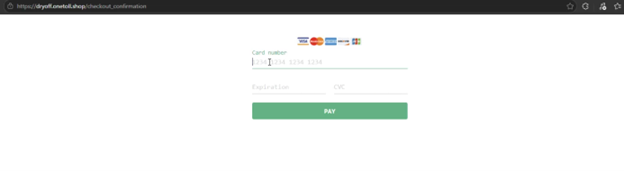
First, I am instructed to enter my card here:
Then I get redirected to this page and must enter my information again:
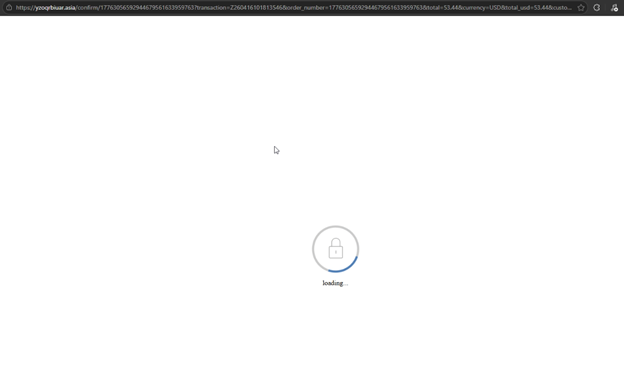
After hitting pay now, a loading screen with a different URL is shown that reminds me of the PayPal loading screen:
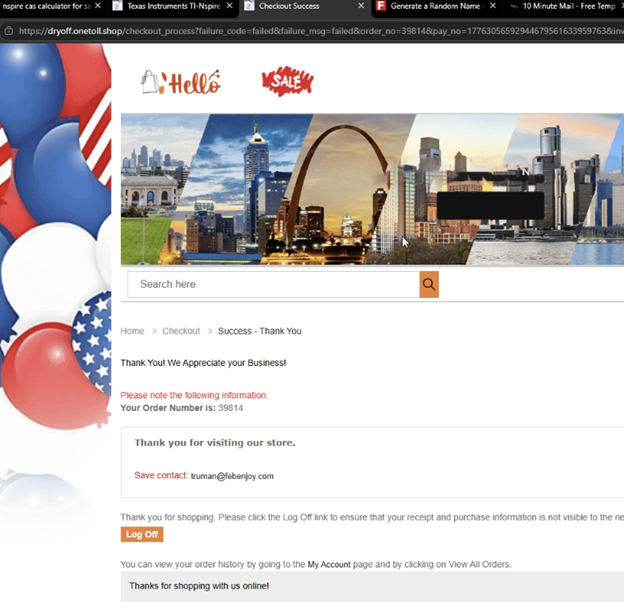
And then I am redirected to a thank-you page for my order, despite the card being declined, which they know because it shows failure_code=failed in the URL.
Only one declined charge was seen on my card. However, in other testing instances, I have seen an additional charge at a different price than the “advertised product”.
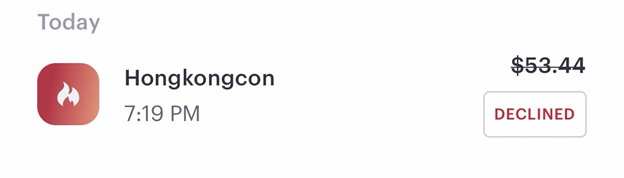
The above screenshot is from the order we just made, and this next screenshot is from a different test where two charges were attempted right away on order:
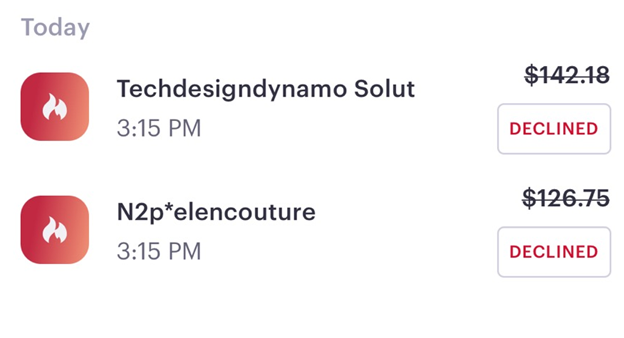
It seems that shirleymcgrady is another similar site, but probably used as the main checkout for the other smaller sites.
The loading page domain from the payment was also created recently, 1 month ago, with one detection on VirusTotal.
Aftermath
A few days after I tried to check out, multiple other charges were attempted on the card:
The clear objective of the scam here is to have the victim make a payment for an item that will never be shipped, resulting in their personal and payment information being stolen. I can only imagine how many people were duped by these marketplaces, considering their popularity, and it must be paying off for the attackers.
With the evolving expertise of AI tools and technology in general, attackers can create these campaigns in a matter of seconds. This takes advantage of the average person’s trust by having a high-ranking site in the search results, images that look real (because they are real, and stolen), and a site that seems trustworthy enough for someone to enter their card details.
I would love to take this a step further and use a card with more funds to purchase a lower-cost item to see how different, if at all, the result would be. It is also fun to hunt down these different marketplaces and see how many you can find. Annoyingly, some of them use registrars that make it harder, not easier, to report abuse, but if anyone reading this would like to investigate this further, I would love to offer my help and see what we can do about it.
Indicators of Compromise
Marketplace Domains:
sydney.nbcsi[.]com
dryoff.onetoll[.]shop
popeye.fivedemo[.]shop
offup.japanhold[.]shop
Redirector Domains:
desidrivingschool[.]com
curencares[.]in
abralipedema.com[.]br
Payment Page Domains:
shirleymcgrady[.]com
yzoqrbiuar[.]asia
Proxying the Unproxyable? Sending EXE traffic to a Proxy
.. if “unproxyable” is a word that is ..
I had a recent engagement where I had to look at the network traffic generated by a Windows executable. Unfortunately, it was all TLS, and all TLS1.3 to boot. So from a PCAP all I got was a whole lot of “yup, that’s encrypted”, and since it was TLSv1.3 all I really had to work with was the IP addresses, not even server names in the server hello packets to help out. And the IP addresses involved were those “500 DNS names AWS” shotgun addresses, so no help there.
What I really needed was something to take specific traffic, say traffic from an executable, and redirect that to a proxy. If that proxy is then burp suite, then Bob’s yer Uncle, now I can look at the traffic!! If you’d rather use fiddler or some other proxy, go for it, anything will work.
A few minutes of Googling, and I found Proxifier (https://www.proxifier.com/)
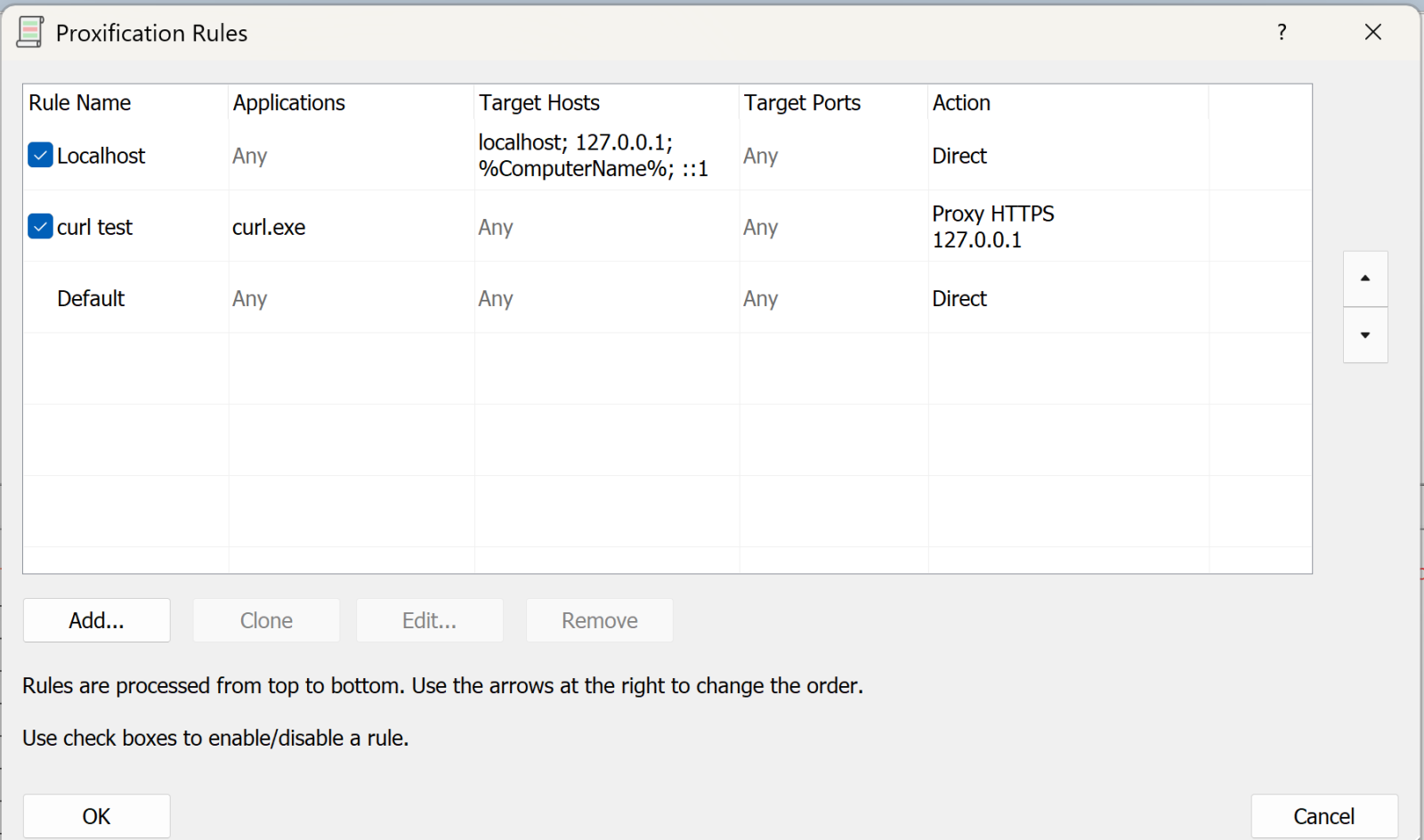
Proxifier allows you set up rules, for instance “send traffic from abc.exe to proxy A”, “send traffic from def.exe to proxy B”, or “send everything else direct”, or any combination. Proxies can be direct or Socks5.
In my case, I was looking at a client executable, and was able to follow all the API calls and data transferred, it was EXACTLY what I needed that day.
I can’t show you the client output - watching the API’s roll by was as cool as it gets though, and the proxy intercept in burp lets you “play” with individual calls if that’s what you need. But I can certainly show you how this works, let’s use curl as our example exe.
Let's start in proxifier. First you need to set up your proxy(s). In this case I'm using Burp Suite Pro running locally, so the proxy is:
.png)
Next, we’ll set up the rules:
The first rule says “anything to my own machine, send direct”. Given how much loopback cruft happens on a typical Windows box, this rule is gold (unless that’s what you are looking for that is).
The second rule is “anything from curl.exe, send to the proxy we just defined” (or whatever your executable is).
You can have multiple of these rules doing different things.
The final rule is “everything else, send direct”
Now, let’s run a test with curl:
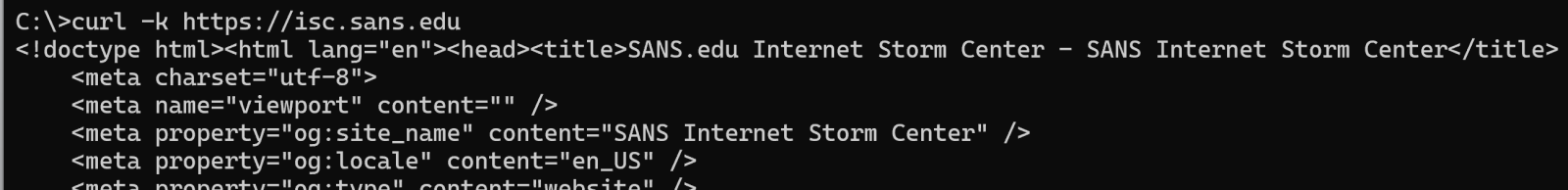
(and so on)
On proxifier, you see the transaction happen in real time:
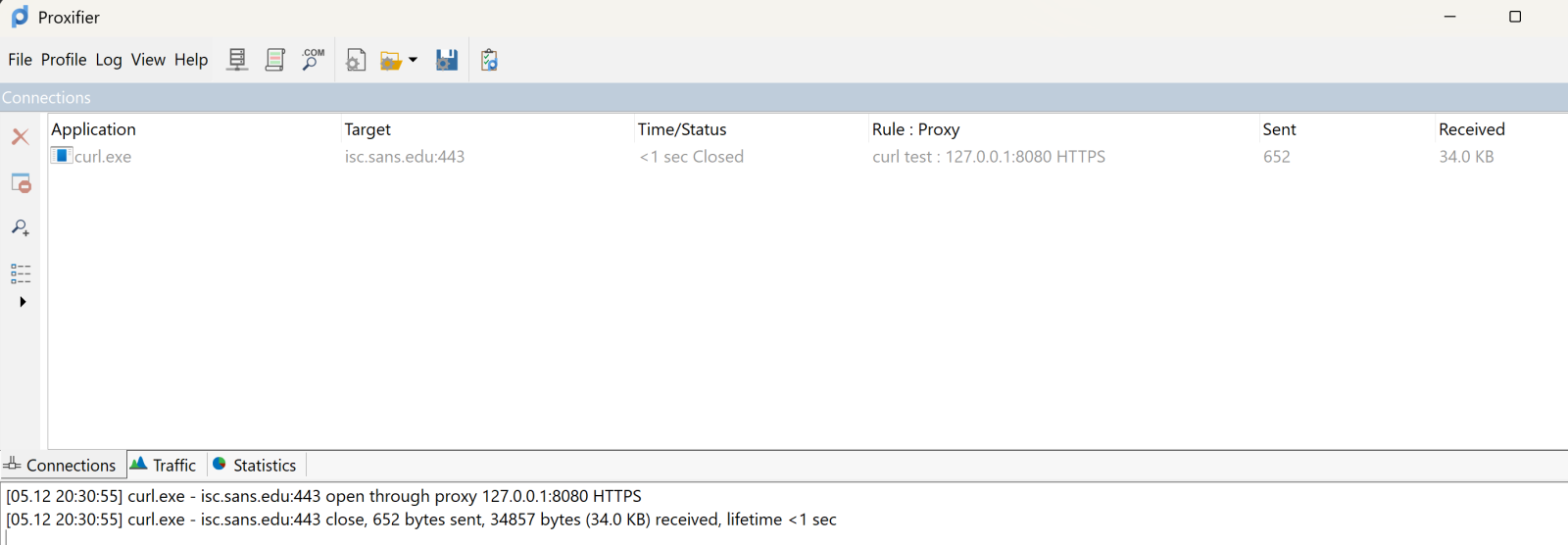
The top pane shows the executable, target and so on. It’s somewhat ephemeral, it’ll show the live view, then will go grey after the transaction complets, then after a few second disappears. The bottom pane scrolls in a more “log like” manner.
Over in Burp, you see all the business that most sites have as their lead page:
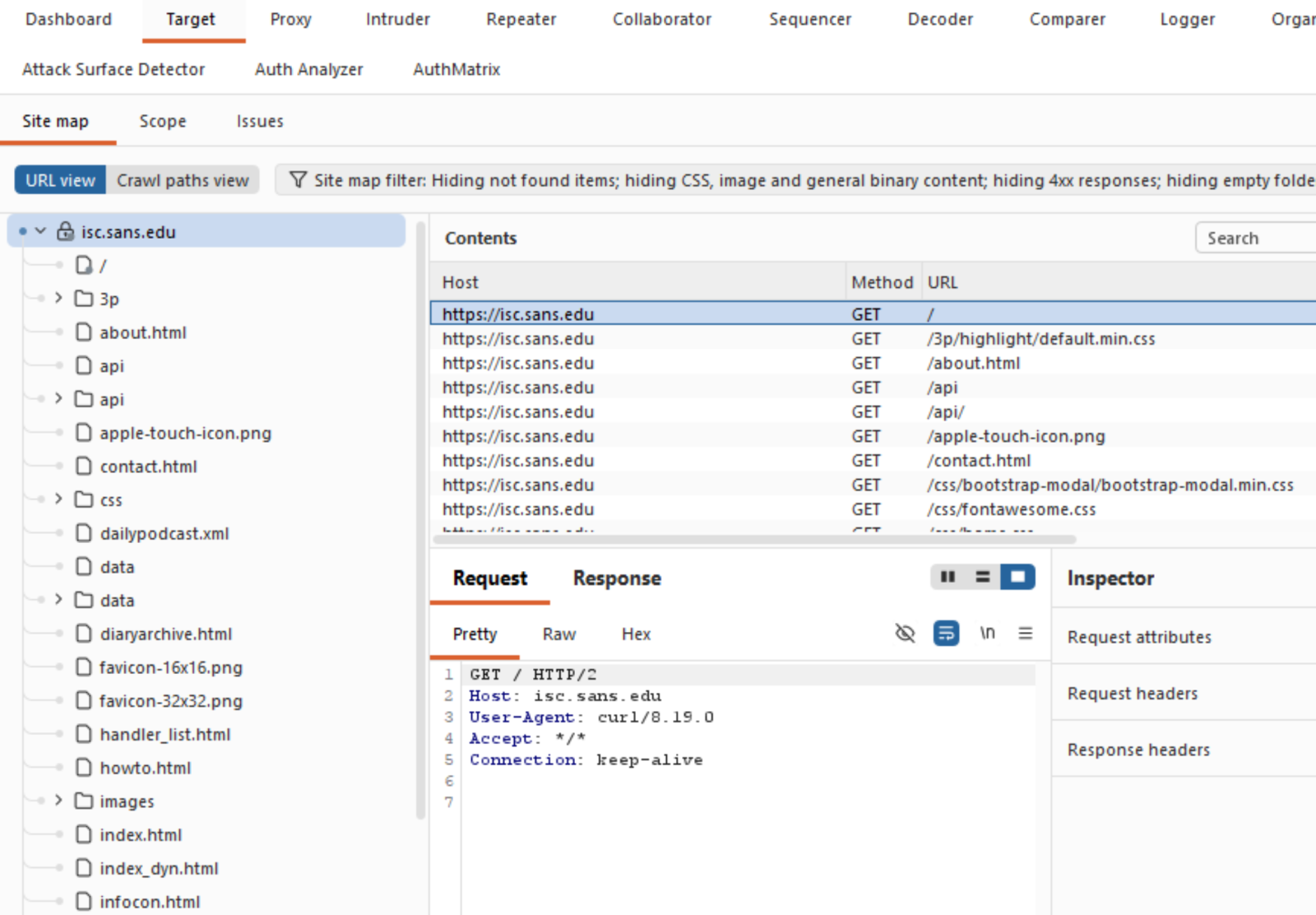
Which is exactly what you need, and can't get these days from a packet capture!
What else does Proxifier do? It also spits out a configurable log file, you can configure what’s in the logs and where to send it:
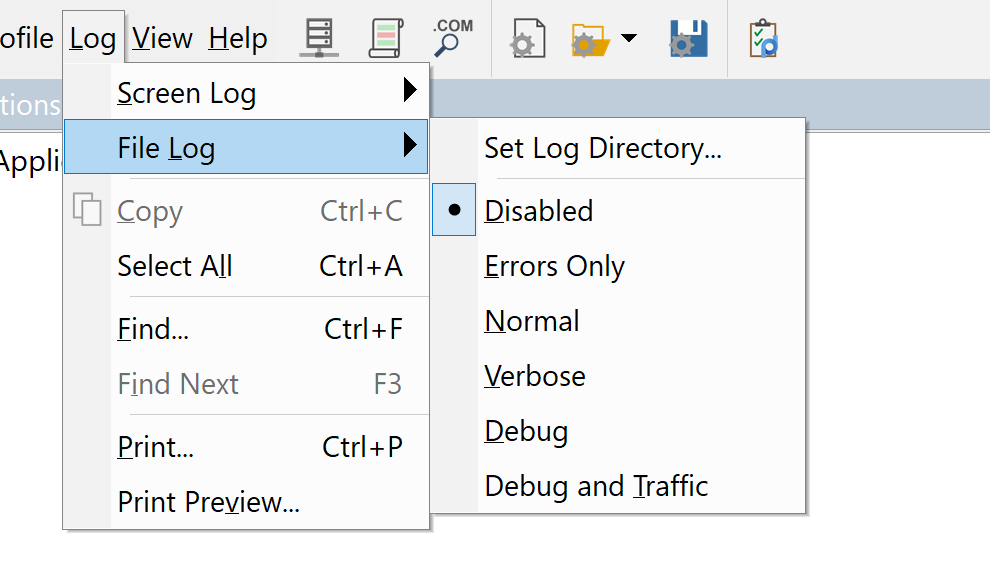
You can set similar sensitivity on the live on-screen log.
All in all, this tool was a life-saver for me, I’ve used it for a few years now and keep coming up with things that it can bail me out of!
Got a cool use for a tool like this? Give it a try and share your experiences in our comment form below (please keep any NDA’s in mind).
Do you have a similar or better tool for this, again, by all means share in our comment form!
===============
Rob VandenBrink
[email protected]


Comments