IPv4 Address Representations
A reader asked for help with this maldoc. Not with the analysis itself, but how to understand where the URL is pointing to.
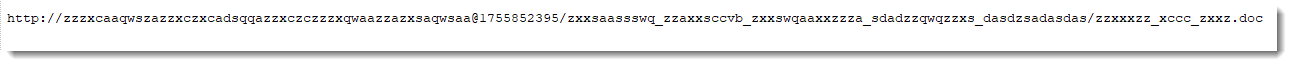
This is the URL they extracted:
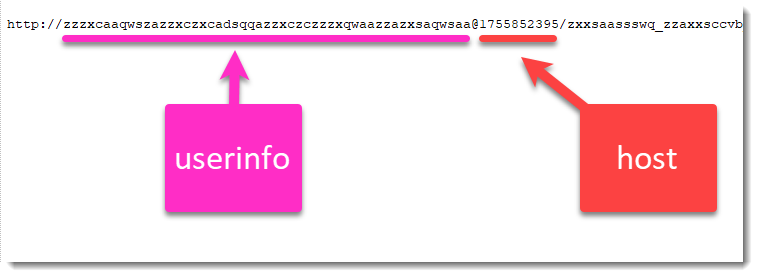
It contains userinfo and a host:
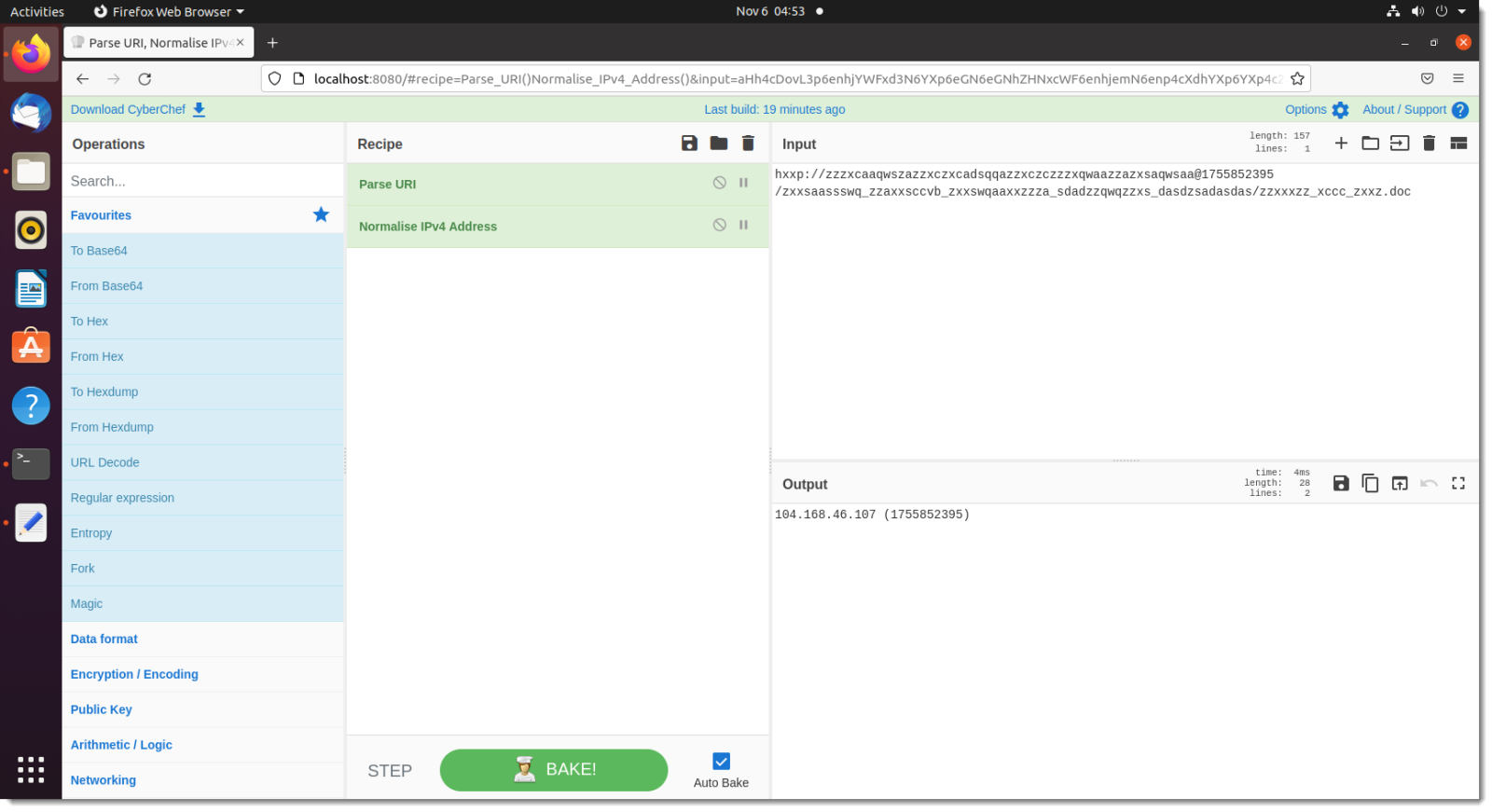
This URL analysis can also be done with CyberChef, using the Parse URI operation:
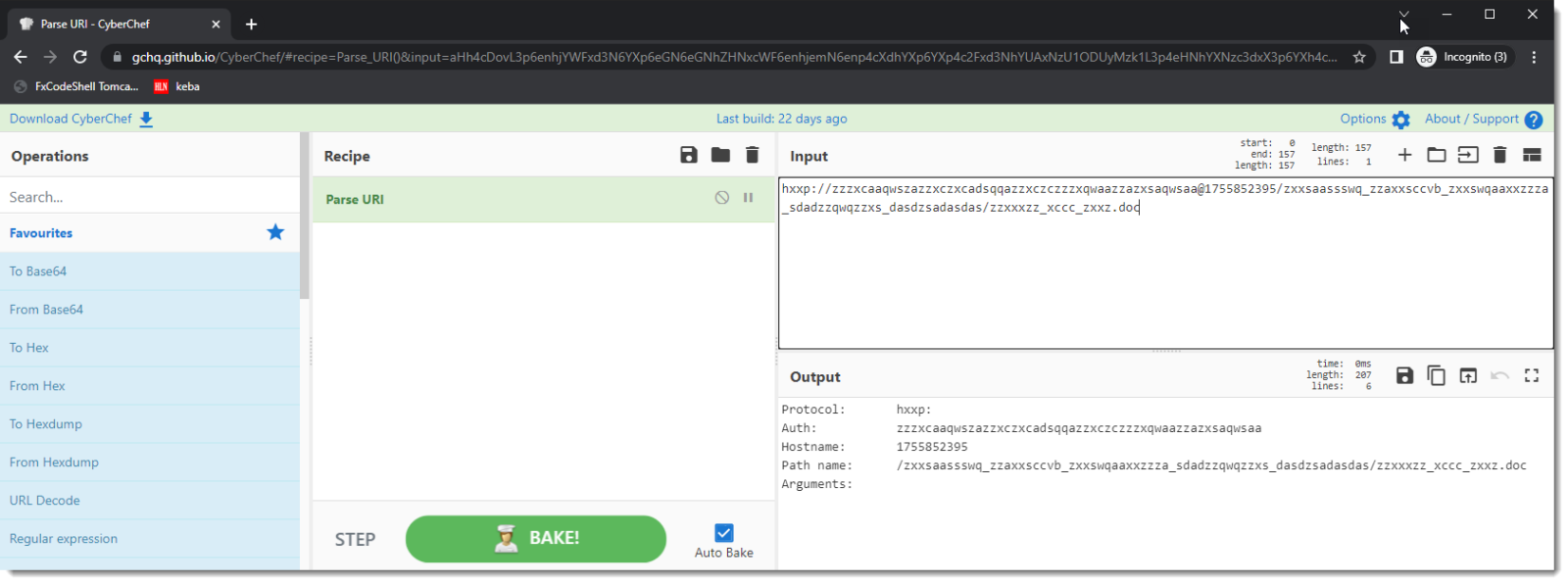
So the host is just a number. An integer.
That integer is an IPv4 address. According to Wikipedia:
IPv4 addresses may be represented in any notation expressing a 32-bit integer value.
There is no CyberChef operation to convert this value, but it can be done with a short Python script, that you can run online in one of the many online Python interpreters:
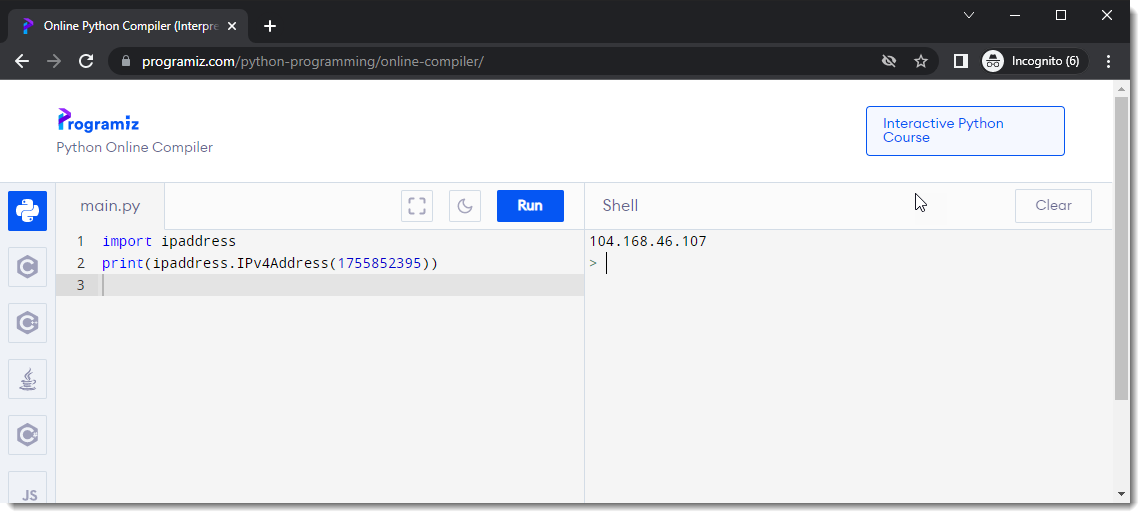
import ipaddress
print(ipaddress.IPv4Address(fill in your IPv4 address))
Maybe someone can code a new CyberChef operation that parses the many IPv4 address representations. This blog post on IPv4 address representations is a good starting point.
(I started to adapt some existing CyberChef operations and code new ones).
Update: I started writing a new "Normalise IPv4 Address" operation:
Didier Stevens
Senior handler
Microsoft MVP
blog.DidierStevens.com


Comments