Python Obfuscation for Dummies
Recently, I found several malicious Python scripts that looked the same. They all contained the same strings at the end:
eval(compile(base64.b64decode(eval('<hex_encoded_string>')),'<string>','exec'))
Pretty nifty obfuscation technique because you cannot get any idea of the script's purpose without executing it in a sandbox or checking deeper. Obfuscation is a crucial element for attackers because they help to bypass classic security controls and they slow down the analysis process by Security Analysts. How does it work? Attackers write their code then they use tools to obfuscate the code. Of course, they are tools available in the underground, but there are also tools publicly available.
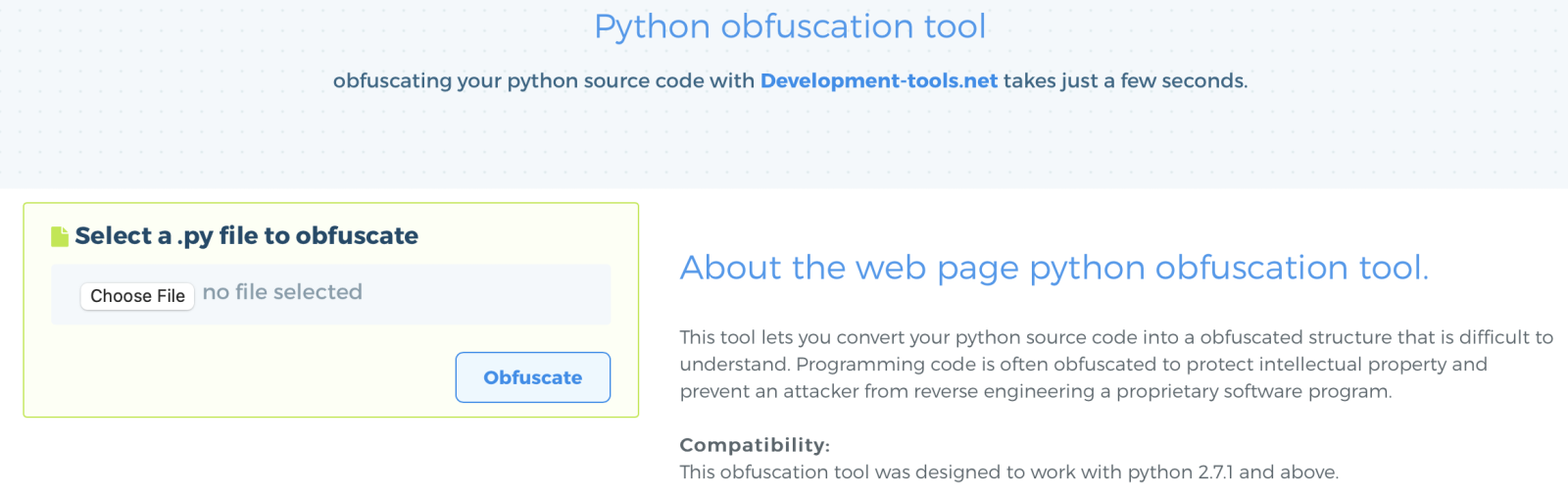
One of them is called development-tools.net[1], which provides a free online Python obfuscation tool:
Here is a simple/fantastic script:
#!/usr/bin/python print "Hello world!"
The obfuscated code is:
import base64, codecs
magic = 'IyEvdXNyL2Jpb'
love = 'v9jrKEbo24XpU'
god = 'JpbnQgIkhlbGx'
destiny = 'iVUqipzkxVFVX'
joy = '\x72\x6f\x74\x31\x33'
trust = eval('\x6d\x61\x67\x69\x63') + eval('\x63\x6f\x64\x65\x63\x73\x2e\x64\x65\x63\x6f\x64\x65\x28\x6c\x6f\x76\x65\x2c\x20\x6a\x6f\x79\x29') + \
eval('\x67\x6f\x64') + eval('\x63\x6f\x64\x65\x63\x73\x2e\x64\x65\x63\x6f\x64\x65\x28\x64\x65\x73\x74\x69\x6e\x79\x2c\x20\x6a\x6f\x79\x29')
eval(compile(base64.b64decode(eval('\x74\x72\x75\x73\x74')),'<string>','exec'))
But is the obfuscation efficient to make the Python script bypass some AV's? I selected a classic script (a password stealer). The script has a current score of 4/60 on VT (SHA256:5f9a62e6c09f085ffb60caefbe155e3ead38848d0f5201517ca0c3cccc09ce78)[2]. The obfuscated script received a score of 5/60.
Another one (a keylogger) with a score of 10/59 (SHA256:77d1cda4ab39e3e0f0a7af4c3d86a42721b9a0d62ccf2f3112988e518c296af5)[3]. The obfuscated version also received a score of 5/60.
As you can see, if the code is really difficult to understand out-of-the-box by an Analyst (goal completed) without proper tools. However, this obfuscation tool does not always improve the detection rate of antivirus tools.
[1] https://development-tools.net/python-obfuscator/
[2] https://www.virustotal.com/gui/file/5f9a62e6c09f085ffb60caefbe155e3ead38848d0f5201517ca0c3cccc09ce78/detection
[3] https://www.virustotal.com/gui/file/77d1cda4ab39e3e0f0a7af4c3d86a42721b9a0d62ccf2f3112988e518c296af5/detection
Xavier Mertens (@xme)
Xameco
Senior ISC Handler - Freelance Cyber Security Consultant
PGP Key


Comments