The Importance of Out-of-Band Networks
Out-of-band (or "OoB") networks are usually dedicated to management tasks. Many security appliances and servers have dedicated management interfaces that are used to set up, control, and monitor the device. A best practice is to connect those management interfaces to a dedicated network that is not directly connected to the network used to carry applications/users' data. If a physically separated network is always best, a dedicated VLAN could do the job in most cases (if properly configured). What we typically find on OoB networks are:
- Network devices (switches, routers, access-points)
- IPMI (ILO, DRAC, etc)
- Appliances management interfaces
- Management interfaces of servers
They also carry sensitive protocols like SNMP, backup traffic to not interfere with the "production" traffic. OoB networks are, based on their criticality, pretty well hardened with very limited access through bastion hosts. Sometimes, they are so well protected that remote access is not allowed and could lead to critical situations like the recent Facebook downtime due to a BGP issue[1].
But OoB networks can also be used for other purposes: during a security incident. It's recommended to not allow Incident Handlers to use the corporate network to exchange information.
A few days ago, an interesting tweet has been posted by @vxunderground[2]. Apparently, the Ragnar Locker ransomware group was able to access a Slack channel used by the organization in charge of the investigations.
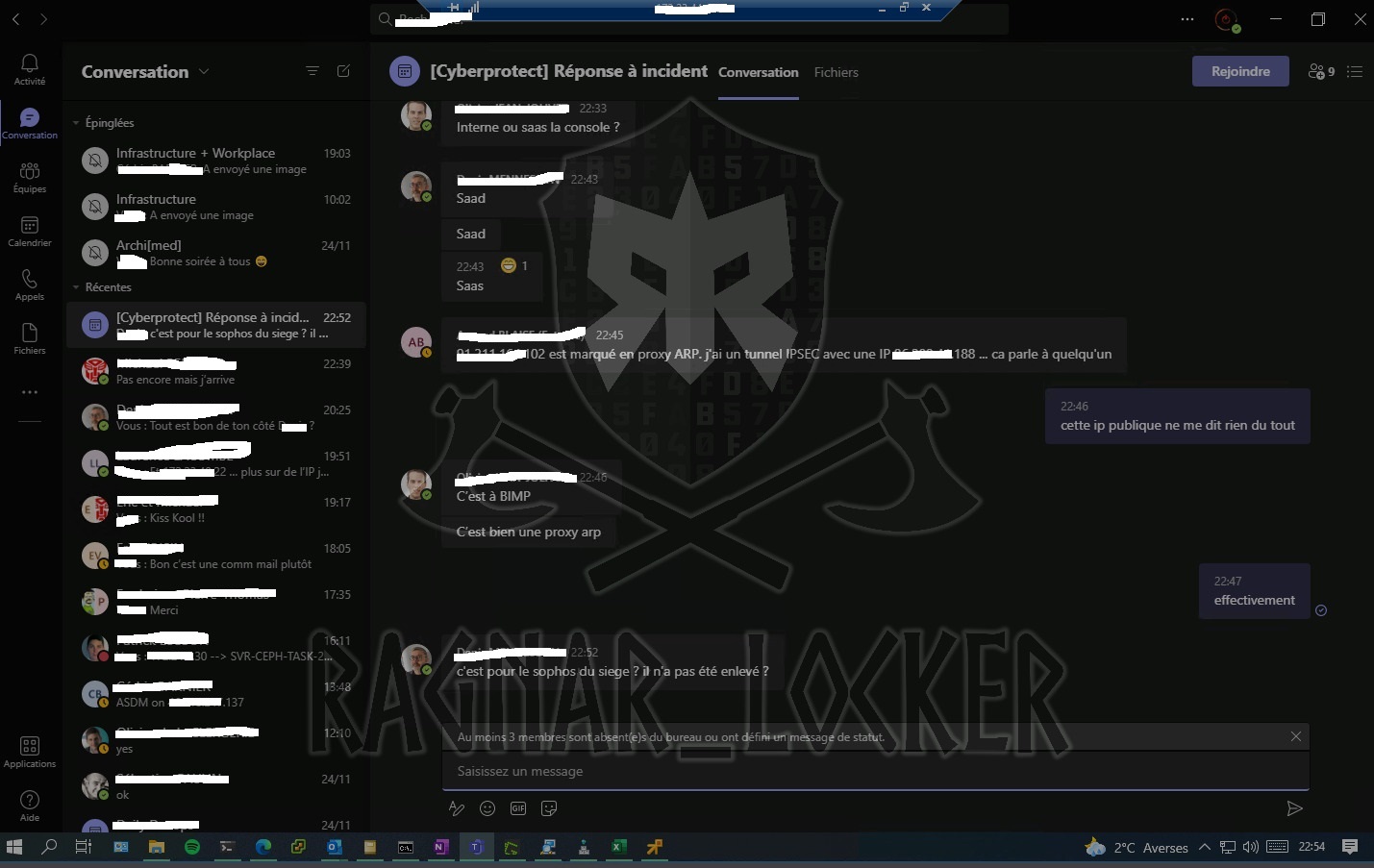
(Image source: vxunderground's Twitter account)
As you can see on top of the screenshot, there is the classic Remote Desktop Client banner. Probably, an Incident Handler was connected to the Teams channel from a workstation on the compromised network and the attacker was still present... Teams is an "external service" and traffic to Teams is encrypted but if the client or the browser can be accessed, it's too late!
[1] https://blog.cloudflare.com/october-2021-facebook-outage/
[2] https://twitter.com/vxunderground/status/1466523987031302145?s=20
Xavier Mertens (@xme)
Senior ISC Handler - Freelance Cyber Security Consultant
PGP Key


Comments