Scanning for Microsoft Secure Socket Tunneling Protocol
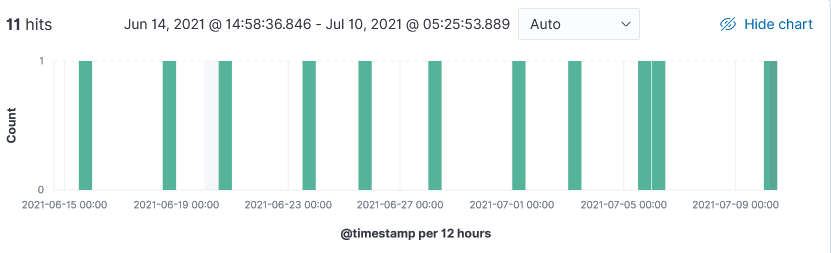
Over the past month I noticed a resurgence of probe by Digitalocean looking for the Microsoft (MS) Secure Socket Tunneling Protocol (SSTP). This MS proprietary VPN protocol is used to establish a secure connection via the Transport Layer Security (TLS) between a client and a VPN gateway. Additional information on this protocol available here.
Sample Log
20210710-062306: 192.168.25.9:443-138.68.249.116:50742 data
SSTP_DUPLEX_POST /sra_{BA195980-CD49-458b-9E23-C84EE0ADCD75}/ HTTP/1.1
SSTPCORRELATIONID: {19730D60-90A0-4623-8C44-688D762AAA16}
Content-Length: 18446744073709551615
Host: XX.XX.28.221
Indicators
138.68.249.116
157.245.176.143
[1] http://msdn.microsoft.com/en-us/library/cc247364.aspx
[2] https://docs.microsoft.com/en-us/openspecs/windows_protocols/ms-sstp/70adc1df-c4fe-4b02-8872-f1d8b9ad806a
[3] https://nmap.org/nsedoc/scripts/sstp-discover.html
[4] https://otx.alienvault.com/indicator/ip/138.68.249.116
[5] https://otx.alienvault.com/indicator/ip/157.245.176.143
-----------
Guy Bruneau IPSS Inc.
My Handler Page
Twitter: GuyBruneau
gbruneau at isc dot sans dot edu


Comments