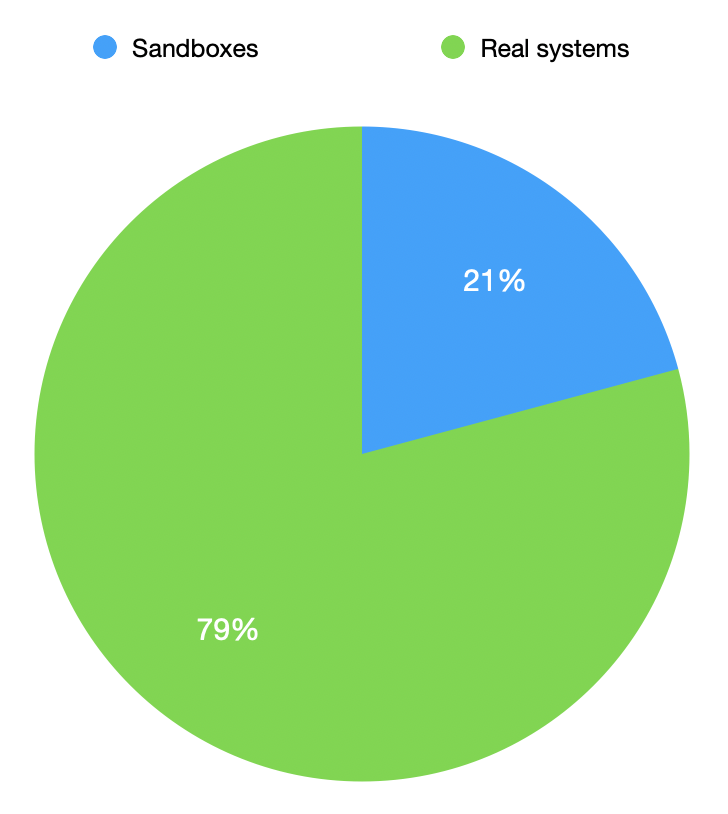
C2 Activity: Sandboxes or Real Victims?
In my last diary[1], I mentioned that I was able to access screenshots exfiltrated by the malware sample. During the first analysis, there were approximately 460 JPEG files available. I continued to keep an eye on the host and the number slightly increased but not so much. My diary conclusion was that the malware looks popular seeing the number of screenshots but wait… Are we sure that all those screenshots are real victims? I executed the malware in my sandbox and probably other automated analysis tools were used to detonate the malware in a sandbox. This question popped up in my mind: How do have an idea about the ratio of automated tools VS. real victims?
I grabbed all the pictures in a local directory and wrote some lines of Python to analyze them. The main question is: how to detect if the screenshot has been taken in a sandbox or a real system? What we can check:
- The size of the screenshot (that matches the desktop)
- The percentage of unified color (usually, sandbox don’t have open windows and a limited set of icons on the desktop).
To « translate » this into Python, I used the classic library to work on image: pillow[2]. extcolors is a small library that works directly on colors[3].
#!/usr/bin/python3
import extcolors
import PIL
import os
folder="screenshots"
for image in os.listdir(folder):
img = PIL.Image.open(folder+"/"+image)
width, height = img.size
colors, pixel_count = extcolors.extract_from_image(img)
if width <= 1024 and height <= 768:
print("Possible sandbox: %s : Size: %dx%d" % (image, width, height))
else:
for c in colors:
hexcolor = '%02x%02x%02x' % c[0]
percentage = (c[1] / pixel_count) * 100
if percentage > 93 and hexcolor < "f00000":
print("Possible sandbox: %s : Color: %s (%6.2f%%)" % (image,hexcolor, percentage))
After some tests, I decided to "flag" a screenshot as coming from a sandbox if the screen resolution is below 1024x768 and if we have >93% of a dark color (to match the classic blue, black or green backgrounds. Let's execute the scripts against the collected pictures:
Possible sandbox: 152114211370.jpg : Color: 000000 ( 94.25%) Possible sandbox: 152117757583.jpg : Color: 000000 ( 98.20%) Possible sandbox: 152127051988.jpg : Color: 000000 ( 95.09%) Possible sandbox: 152178310978.jpg : Size: 1024x768 Possible sandbox: 152129950226.jpg : Size: 800x600 Possible sandbox: 152115117436.jpg : Size: 800x600 Possible sandbox: 152135496106.jpg : Color: c7b199 ( 99.23%) Possible sandbox: 152119090512.jpg : Color: 000000 ( 99.37%) Possible sandbox: 152129464868.jpg : Color: 2974c7 ( 94.60%) Possible sandbox: 152153616774.jpg : Size: 800x600 Possible sandbox: 152137277200.jpg : Size: 800x600 Possible sandbox: 152157989841.jpg : Size: 1024x768 ...
Here are the results:
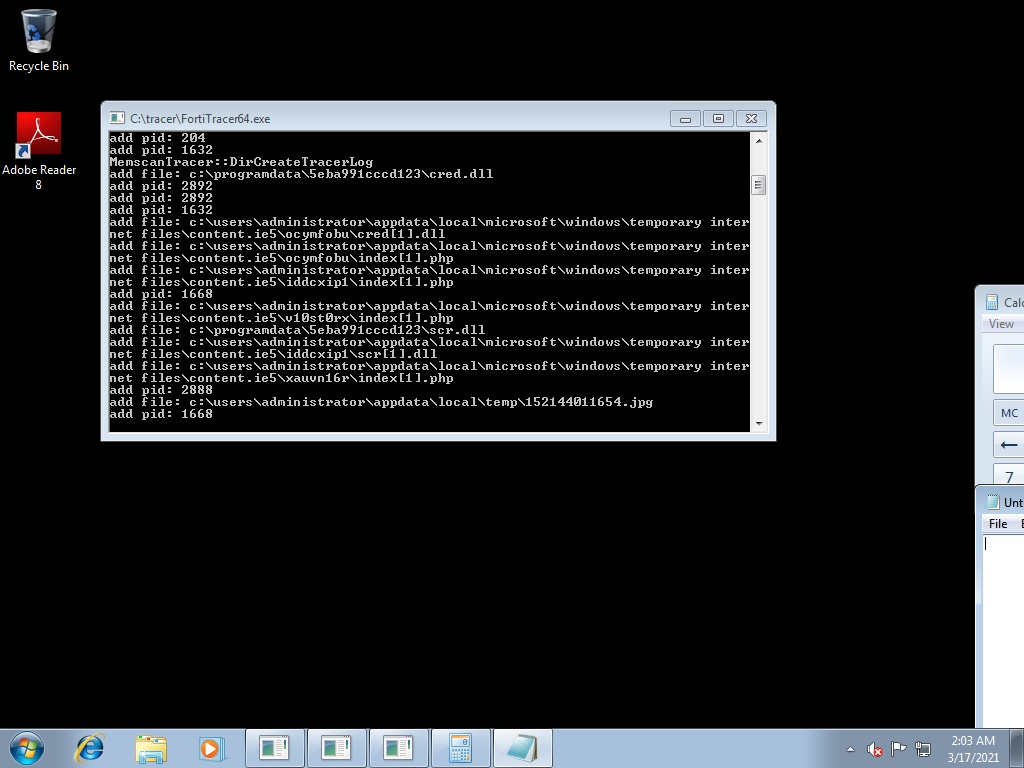
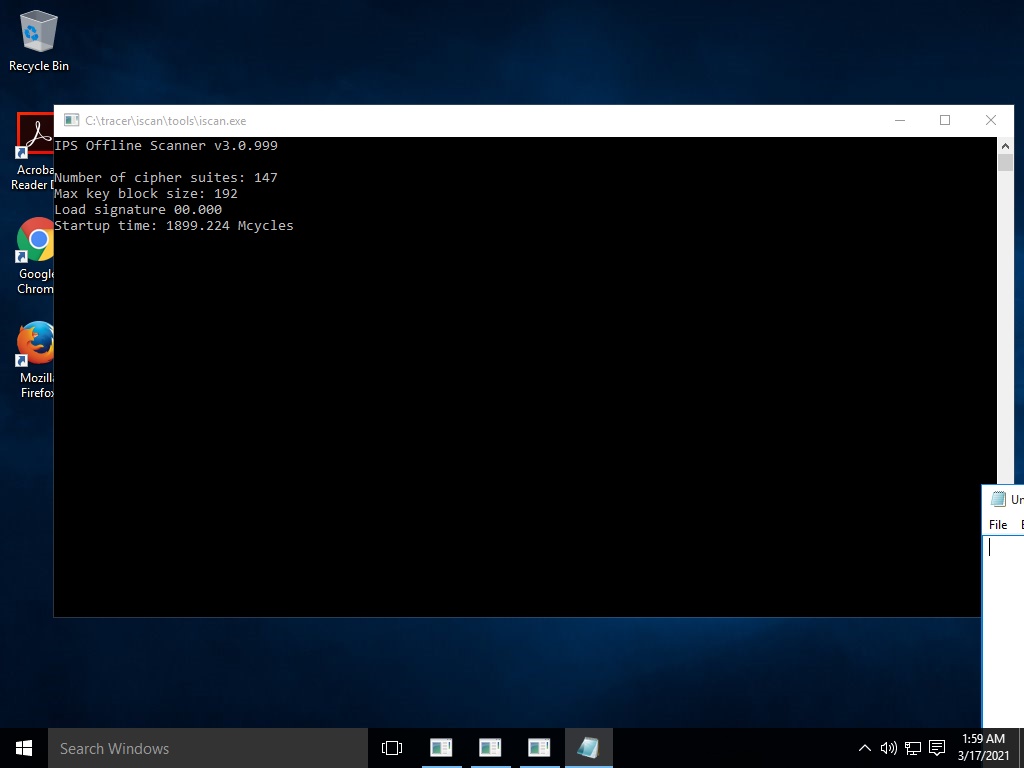
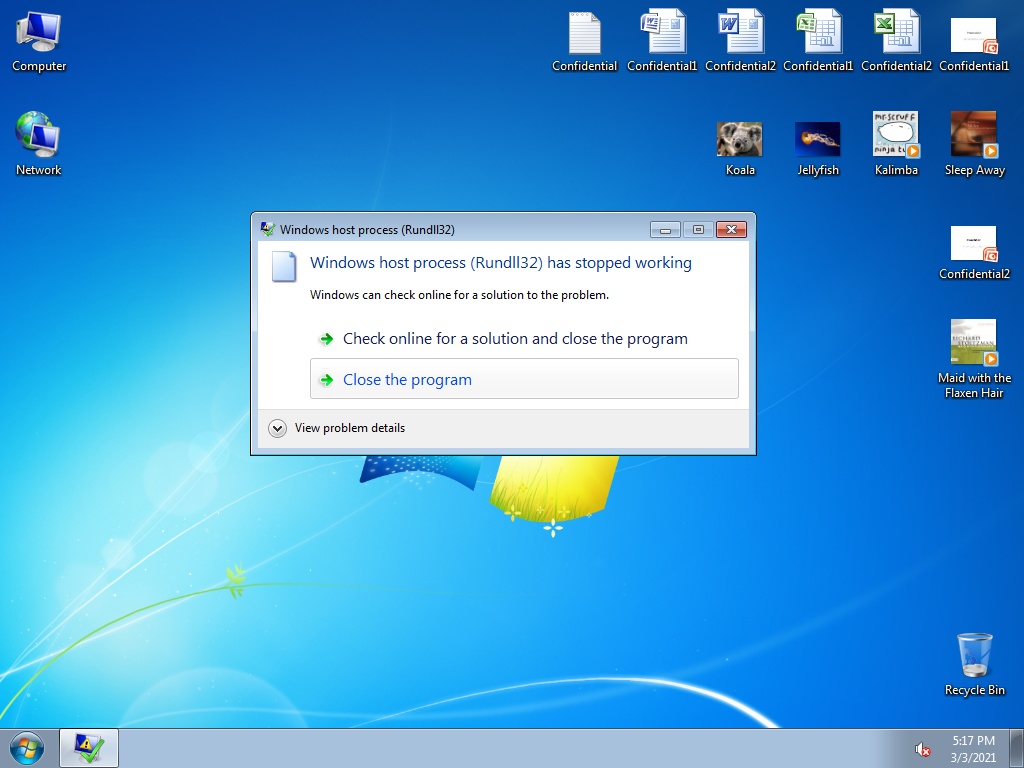
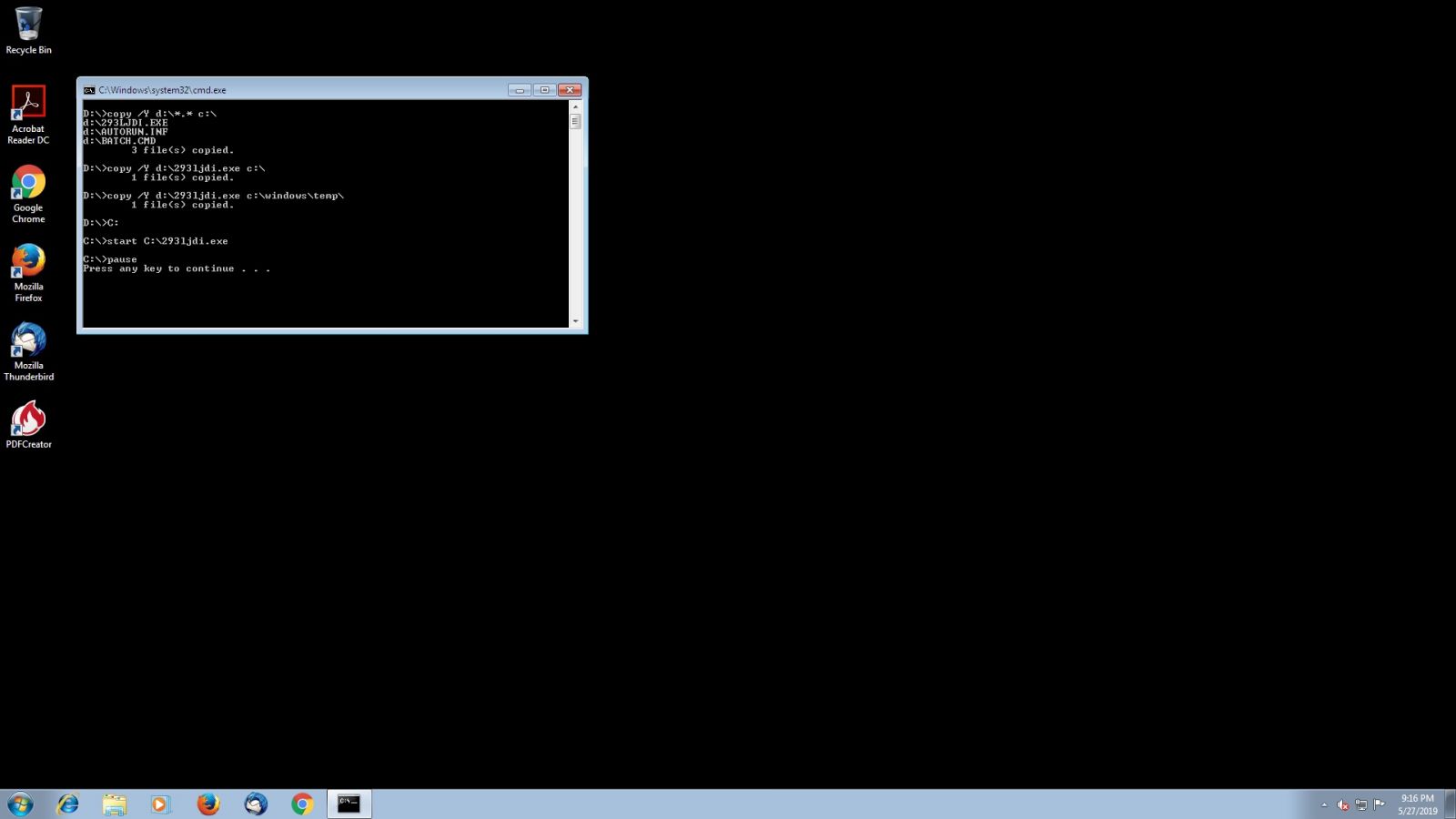
Some detected sandboxes:
[1] https://isc.sans.edu/forums/diary/Quick+Analysis+of+a+Modular+InfoStealer/27264/
[2] https://pillow.readthedocs.io/en/stable/
[3] https://pypi.org/project/extcolors/
Xavier Mertens (@xme)
Senior ISC Handler - Freelance Cyber Security Consultant
PGP Key


Comments