CyberChef: Analyzing OOXML Files for URLs
In diary entry "Doc & RTF Malicious Document" I start analyzing a malicious Word document with my tools.
That Word document, an Office Open XML file (OOXML, .docx), is a ZIP container with XML files. I show how to extract URLs from this document.
CyberChef can also process ZIP files: I made a CyberChef recipe to extract URLs from OOXML files.
This is how it looks:
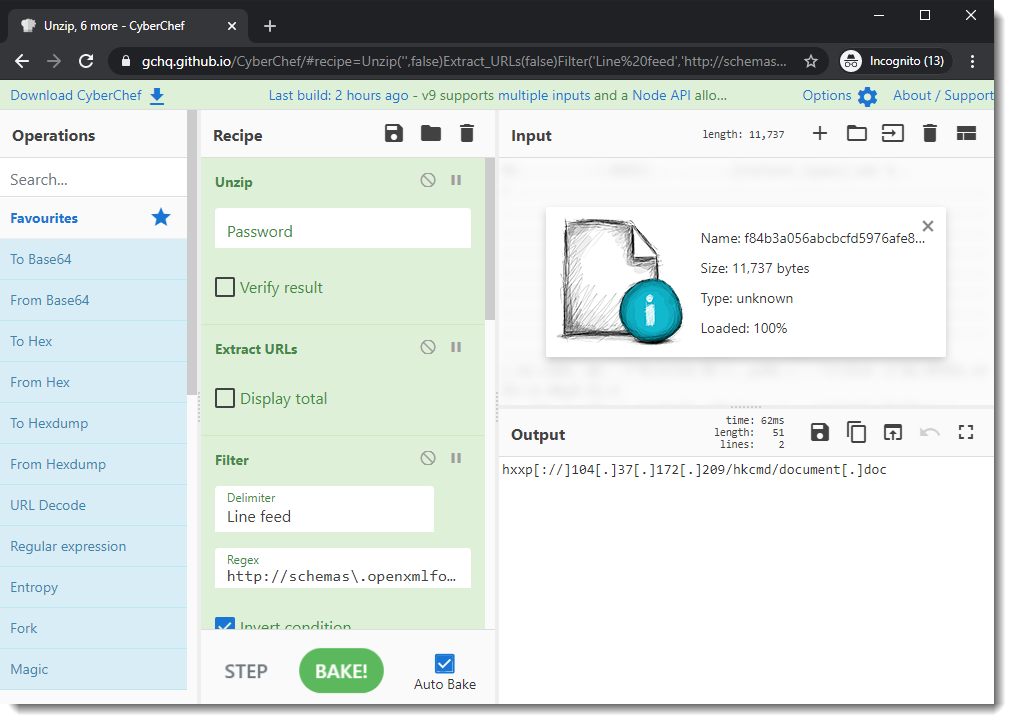
You can use it for any .docx, .docm, .xlsx, ... file (OOXML file) to see if it contains URLs.
And if you want to understand how I use CyberChef to create this recipe, take a look at this video:
Didier Stevens
Senior handler
Microsoft MVP
blog.DidierStevens.com DidierStevensLabs.com
×
![modal content]()
Diary Archives


Comments