Maldoc: VBA Purging Example
An anonymous reader asked if the malicious document Brad discussed in his latest diary entry, was "purged". VBA purging means that the compiled VBA code (PerformanceCache) is missing.
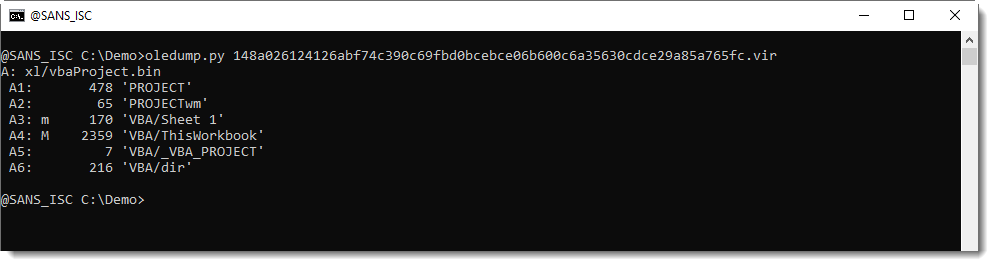
And indeed, if you use my tool oledump.py with option -i, you get more information and you can see that the PerformanceCache data is not present:
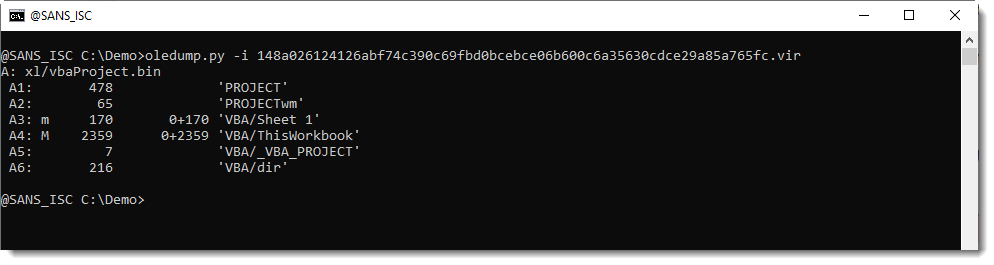
0+2359 means that the size of the PerformanceCache data is 0, and that the size of the CompileSourceCode data is 2359 bytes: this VBA code is indeed purged.
I took a look at the metadata to get an indiction if the document was created with Office and then VBA purged, or if a custom tool was used that does not generate PerformanceCache data. Since it is an OOXML file, I looked for the properties XML files (docProps):
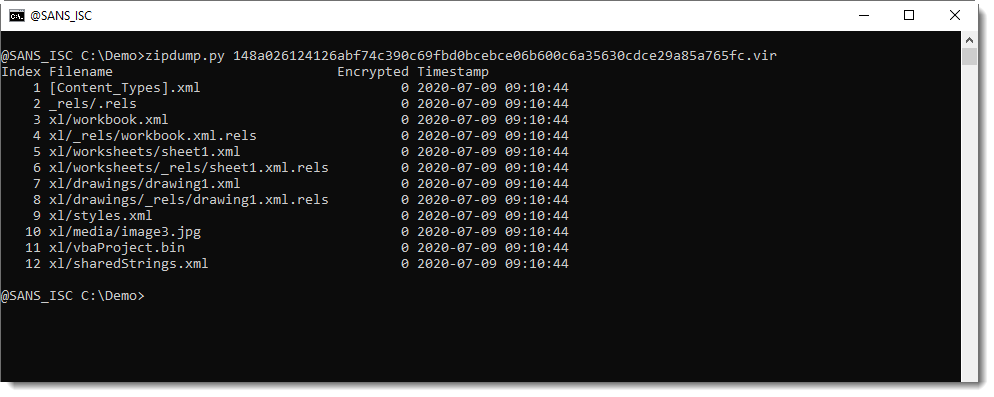
And as you can see, the metadata is missing too.
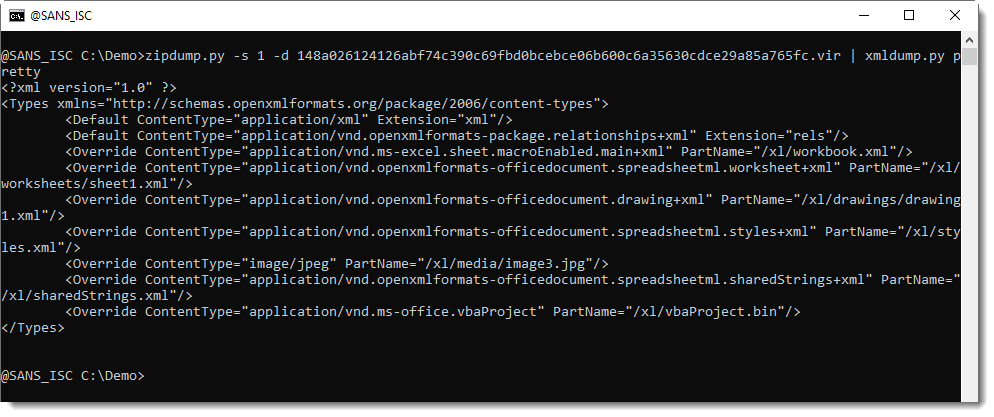
It's not that the docProps files have been deleted, they are also not referenced in the Content_Types file:
I need to take a better look to have more confidence, but now I would be inclined to think that this document was created with a custom tool.
Update: I just noticed that the VBA code is also password protected.
Update 2: I have even more confidence, now I'm thinking this document was created with C# library EPPlus.
Didier Stevens
Senior handler
Microsoft MVP
blog.DidierStevens.com DidierStevensLabs.com


Comments