Microsoft September Patch Tuesday Summary
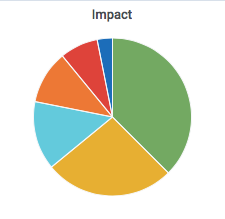
Microsoft released patches for 61 vulnerabilities. In addition, we got two advisories. One for the usual update for Flash, and one for a Windows DoS vulnerability.
The DoS advisory covers "FragmentSmack", an issue first released mid-August. For Unix systems, the recommendation was to reduce the buffer space used for fragments. Microsoft is going a step further: It suggests to drop all out of order fragements. This step appears to be a bit "drastic" in that it can lead to valid data being dropped and something to consider if you tune your IDS accordingly.
This update also patches the "ALPC" privilege escalation flaw, which has already been exploited by malware.
3 additional already disclosed vulnerabilities are patched (see table below for details)
See the Patch Tuesday Dashboard for more details.
| Description | |||||||
|---|---|---|---|---|---|---|---|
| CVE | Disclosed | Exploited | Exploitability (old versions) | current version | Severity | CVSS Base (AVG) | CVSS Temporal (AVG) |
| .NET Framework Remote Code Execution Vulnerability | |||||||
| CVE-2018-8421 | No | No | Less Likely | Less Likely | Critical | ||
| Azure IoT SDK Spoofing Vulnerability | |||||||
| CVE-2018-8479 | No | No | - | - | Important | ||
| Chakra Scripting Engine Memory Corruption Vulnerability | |||||||
| CVE-2018-8367 | No | No | - | - | Critical | 4.2 | 3.8 |
| CVE-2018-8465 | No | No | - | - | Critical | 4.2 | 3.8 |
| CVE-2018-8466 | No | No | - | - | Critical | 4.2 | 3.8 |
| CVE-2018-8467 | No | No | - | - | Critical | 4.2 | 3.8 |
| Device Guard Security Feature Bypass Vulnerability | |||||||
| CVE-2018-8449 | No | No | More Likely | More Likely | Important | 5.3 | 4.8 |
| DirectX Graphics Kernel Elevation of Privilege Vulnerability | |||||||
| CVE-2018-8462 | No | No | More Likely | More Likely | Important | 7.0 | 6.3 |
| Internet Explorer Memory Corruption Vulnerability | |||||||
| CVE-2018-8461 | No | No | More Likely | More Likely | Critical | 7.5 | 6.7 |
| CVE-2018-8447 | No | No | More Likely | More Likely | Critical | 6.4 | 5.8 |
| Internet Explorer Security Feature Bypass Vulnerability | |||||||
| CVE-2018-8470 | No | No | - | - | Important | 2.4 | 2.2 |
| Lync for Mac 2011 Security Feature Bypass Vulnerability | |||||||
| CVE-2018-8474 | No | No | - | - | Moderate | ||
| MS XML Remote Code Execution Vulnerability | |||||||
| CVE-2018-8420 | No | No | More Likely | More Likely | Critical | 6.4 | 5.8 |
| Microsoft Edge Elevation of Privilege Vulnerability | |||||||
| CVE-2018-8463 | No | No | - | - | Important | 4.3 | 3.9 |
| CVE-2018-8469 | No | No | - | - | Important | 4.3 | 3.9 |
| Microsoft Edge Information Disclosure Vulnerability | |||||||
| CVE-2018-8366 | No | No | - | - | Important | 4.3 | 3.9 |
| Microsoft Edge PDF Remote Code Execution Vulnerability | |||||||
| CVE-2018-8464 | No | No | - | - | Critical | 4.2 | 3.8 |
| Microsoft Edge Spoofing Vulnerability | |||||||
| CVE-2018-8425 | No | No | - | - | Important | 5.3 | 5.3 |
| Microsoft Excel Information Disclosure Vulnerability | |||||||
| CVE-2018-8429 | No | No | Less Likely | Less Likely | Important | ||
| Microsoft Excel Remote Code Execution Vulnerability | |||||||
| CVE-2018-8331 | No | No | - | - | Important | ||
| Microsoft Graphics Component Information Disclosure Vulnerability | |||||||
| CVE-2018-8433 | No | No | Less Likely | Less Likely | Important | 4.7 | 4.2 |
| Microsoft JET Database Engine Remote Code Execution Vulnerability | |||||||
| CVE-2018-8392 | No | No | Less Likely | Less Likely | Important | 7.8 | 7.0 |
| CVE-2018-8393 | No | No | Less Likely | Less Likely | Important | 7.8 | 7.0 |
| Microsoft Office SharePoint XSS Vulnerability | |||||||
| CVE-2018-8426 | No | No | Less Likely | Less Likely | Important | ||
| Microsoft Scripting Engine Information Disclosure Vulnerability | |||||||
| CVE-2018-8315 | No | No | - | - | Important | 4.2 | 3.8 |
| Microsoft SharePoint Elevation of Privilege Vulnerability | |||||||
| CVE-2018-8428 | No | No | Less Likely | Less Likely | Important | ||
| CVE-2018-8431 | No | No | Less Likely | Less Likely | Important | ||
| OData Denial of Service Vulnerability | |||||||
| CVE-2018-8269 | No | No | Less Likely | Less Likely | Important | ||
| Scripting Engine Information Disclosure Vulnerability | |||||||
| CVE-2018-8452 | No | No | - | - | Important | 4.3 | 3.9 |
| Scripting Engine Memory Corruption Vulnerability | |||||||
| CVE-2018-8354 | No | No | - | - | Important | 4.2 | 3.8 |
| CVE-2018-8391 | No | No | - | - | Critical | 4.2 | 3.8 |
| CVE-2018-8456 | No | No | - | - | Critical | 4.2 | 3.8 |
| CVE-2018-8457 | Yes | No | More Likely | More Likely | Critical | 6.4 | 5.8 |
| CVE-2018-8459 | No | No | - | - | Critical | 4.2 | 3.8 |
| September 2018 Adobe Flash Security Update | |||||||
| ADV180023 | No | No | - | - | Critical | ||
| System.IO.Pipelines Denial of Service | |||||||
| CVE-2018-8409 | Yes | No | Less Likely | Less Likely | Important | ||
| Win32k Graphics Remote Code Execution Vulnerability | |||||||
| CVE-2018-8332 | No | No | Less Likely | Less Likely | Critical | 8.8 | 8.8 |
| Windows ALPC Elevation of Privilege Vulnerability | |||||||
| CVE-2018-8440 | Yes | Yes | More Likely | More Likely | Important | 7.0 | 6.3 |
| Windows Denial of Service Vulnerability | |||||||
| ADV180022 | No | No | Less Likely | Less Likely | Important | ||
| Windows Elevation of Privilege Vulnerability | |||||||
| CVE-2018-8468 | No | No | More Likely | More Likely | Important | 4.3 | 3.9 |
| Windows GDI Information Disclosure Vulnerability | |||||||
| CVE-2018-8424 | No | No | Less Likely | Less Likely | Important | 4.7 | 4.2 |
| Windows Hyper-V Denial of Service Vulnerability | |||||||
| CVE-2018-8436 | No | No | - | - | Important | 5.4 | 4.9 |
| CVE-2018-8437 | No | No | - | - | Important | 5.4 | 4.9 |
| CVE-2018-8438 | No | No | Less Likely | Less Likely | Important | 5.8 | 5.2 |
| Windows Hyper-V Information Disclosure Vulnerability | |||||||
| CVE-2018-8434 | No | No | Less Likely | Less Likely | Important | 5.4 | 4.9 |
| Windows Hyper-V Remote Code Execution Vulnerability | |||||||
| CVE-2018-0965 | No | No | Less Likely | Less Likely | Critical | 7.6 | 6.8 |
| CVE-2018-8439 | No | No | Less Likely | Less Likely | Critical | 7.6 | 6.8 |
| Windows Hyper-V Security Feature Bypass Vulnerability | |||||||
| CVE-2018-8435 | No | No | Less Likely | Less Likely | Important | 4.2 | 3.8 |
| Windows Information Disclosure Vulnerability | |||||||
| CVE-2018-8271 | No | No | Less Likely | Less Likely | Important | 2.5 | 2.5 |
| Windows Kernel Elevation of Privilege Vulnerability | |||||||
| CVE-2018-8455 | No | No | Less Likely | Less Likely | Important | 7.0 | 6.3 |
| Windows Kernel Information Disclosure Vulnerability | |||||||
| CVE-2018-8336 | No | No | - | - | Important | 2.5 | 2.5 |
| CVE-2018-8419 | No | No | Less Likely | Less Likely | Important | 4.7 | 4.2 |
| CVE-2018-8442 | No | No | More Likely | More Likely | Important | 4.7 | 4.2 |
| CVE-2018-8443 | No | No | Less Likely | Less Likely | Important | 4.7 | 4.2 |
| CVE-2018-8445 | No | No | - | - | Important | 4.7 | 4.2 |
| CVE-2018-8446 | No | No | Less Likely | Less Likely | Important | 4.7 | 4.2 |
| Windows Registry Elevation of Privilege Vulnerability | |||||||
| CVE-2018-8410 | No | No | More Likely | More Likely | Important | 7.0 | 6.3 |
| Windows Remote Code Execution Vulnerability | |||||||
| CVE-2018-8475 | Yes | No | More Likely | More Likely | Critical | 8.8 | 7.9 |
| Windows SMB Denial of Service Vulnerability | |||||||
| CVE-2018-8335 | No | No | Less Likely | Less Likely | Important | 4.8 | 4.8 |
| Windows SMB Information Disclosure Vulnerability | |||||||
| CVE-2018-8444 | No | No | - | - | Important | 7.0 | 6.3 |
| Windows Subsystem for Linux Elevation of Privilege Vulnerability | |||||||
| CVE-2018-8441 | No | No | - | - | Important | 7.0 | 6.3 |
| Windows Subsystem for Linux Security Feature Bypass Vulnerability | |||||||
| CVE-2018-8337 | No | No | - | - | Important | 5.3 | 4.8 |
| Word PDF Remote Code Execution Vulnerability | |||||||
| CVE-2018-8430 | No | No | More Likely | More Likely | Important | ||
---
Johannes B. Ullrich, Ph.D. , Dean of Research, SANS Technology Institute
Twitter|


Comments