Truncating Payloads and Anonymizing PCAP files
Sometimes, you may need to provide PCAP files to third-party organizations like a vendor support team to investigate a problem with your network. I was looking for a small tool to anonymize network traffic but also to restrict data to packet headers (and drop the payload). Google pointed me to a tool called ‘TCPurify’.
It’s an old tool (last updated in 2008) but it still makes the job! The original website is offline but it is possible to find it using the Internet Archive[1]. They are two main features that are interesting with TCPurify:
- It truncates almost all packets immediately after the last recognized header (IP or Ethernet), removing all data payload before storing the packet.
- It has the capability of randomizing some or all IP addresses (based on the network portion of the address) to mask exactly where packets are where or to while still retaining some general idea.
The latest source code is available also through the Intenet Archive. I did not find any package ready for latest Linux distributions so, let's install it the old-way: compilation! The installation is straightforward on a standard UNIX system. The only requirement is the libpcap and C header files:
# apt-get install libpcap-dev # wget https://web.archive.org/web/20130701155216/http://irg.cs.ohiou.edu/~eblanton/tcpurify/tcpurify-0.11.2.tar.gz # tar xvf tcpurify-0.11.2.tar.gz # cd tcpurify-0.11.2 # ./configure # make install
Now, you have a single executable available in /usr/local/bin. There are different ways to use TCPurify: it can listen to packets from an interface:
# tcpurify -i eth1 -o /tmp/capture.pcap
Or from another PCAP file:
# tcpurify -r /tmp/source.pcap -o /tmp/destination.pcap
What about the anonymization of the packets? There are different modes offered: “none” (does nothing, default), “nullify” (replace all IP addresses with 0.0.0.0) or ‘table’. This one is the most interesting. It allows defining which subnets will be anonymized using filters. Those filters are save in a map file to be able to reconstruct the original PCAL if required later.
Filters are defined like this:
subnet/netmask/xformmask
Example:
192.168.0.0/0xffff0000/0xffff
This will randomize IP addresses from 192.168.0.0/16 except the network & broadcast addresses (example: '192.168.1.2' will be anonymized to '192.168.123.43')
The ‘table’ mode requires an extra argument, 'mapfile' which will point to the filename that will contain the mappings.
Here is an example of usage:
# tcpurify -i eth1 -o /tmp/test.pcap table 192.168.0.0/0xffff0000/0xffff mapfile=/tmp/test.map ^C
The tool looks a very light tcpdump clone and does not allow to fine-tune the capture session. The most important missing option is the non-support for BPF filters. This means that you can’t restrict the traffic when reading from an interface. But you could collect traffic via a regular tcpdump and then anonymize it:
# tcpdump -i eth1 -w /tmp/test.pcap port 80 # tcpurify -r /tmp/test.cap -o /tmp/test_anonymized.pcap table 192.168.0.0/0xffff0000/0xffff mapfile=/tmp/test.map
The tool is not perfect and does not follow modern standards. For example, it does not allow reading PCAP data from stdin and writing to stdout but it can be helpful in many cases. It deserve to be added to your toolbox.
[1] https://web.archive.org/web/20140203210616/irg.cs.ohiou.edu/~eblanton/tcpurify/
Xavier Mertens (@xme)
Senior ISC Handler - Freelance Cyber Security Consultant
PGP Key
More malspam pushing password-protected Word docs for AZORult and Hermes Ransomware
Introduction
This is a follow-up to a previous diary from last month on malicious spam (malspam) distributing password-protected Word docs with malicious macros designed to infect vulnerable Windows computers with ransomware.
Details
Today, I found five examples of malspam with password-protected Word docs using 1234 as the password. The Word doc had a malicious macro that retrieved AZORult malware. The AZORult malware conducted callback traffic, then the infected host retrieved Hermes ransomware.
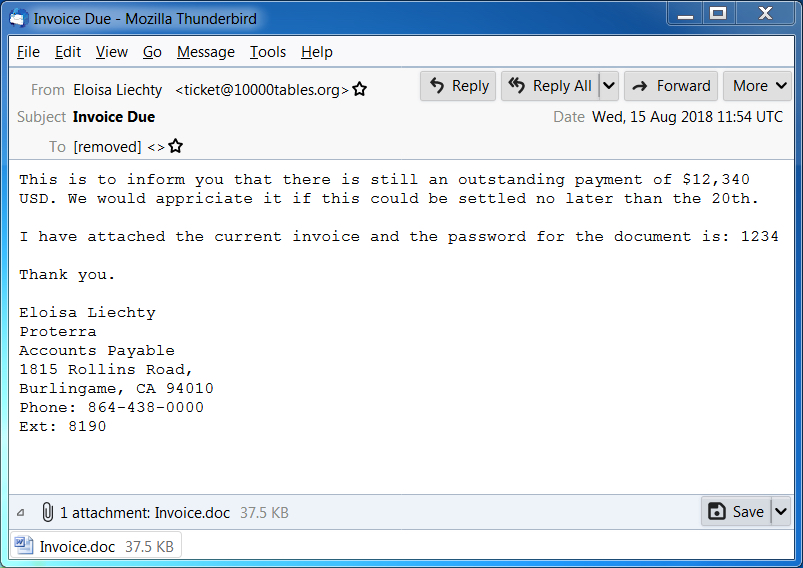
Shown above: Screen shot of a malspam example from today (1 of 2).
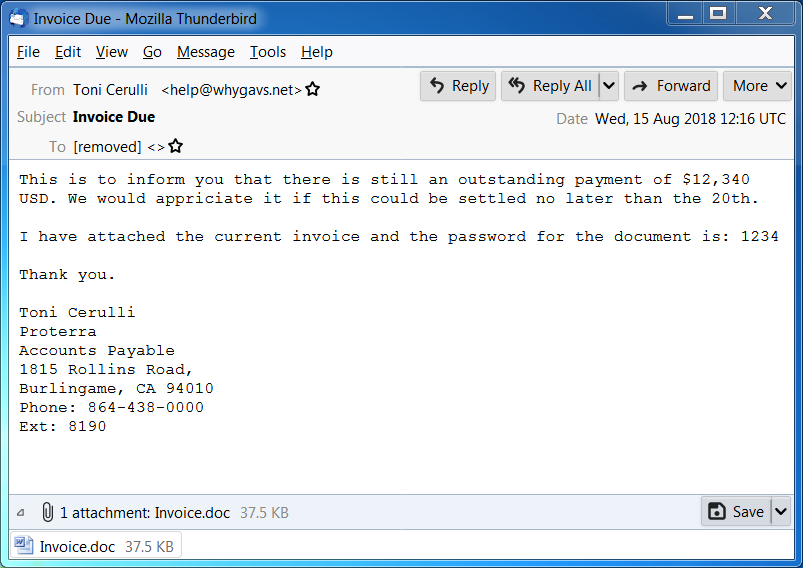
Shown above: Screen shot of a malspam example from today (2 of 2).

Shown above: Opening the password-protected Word doc on a Windows host.
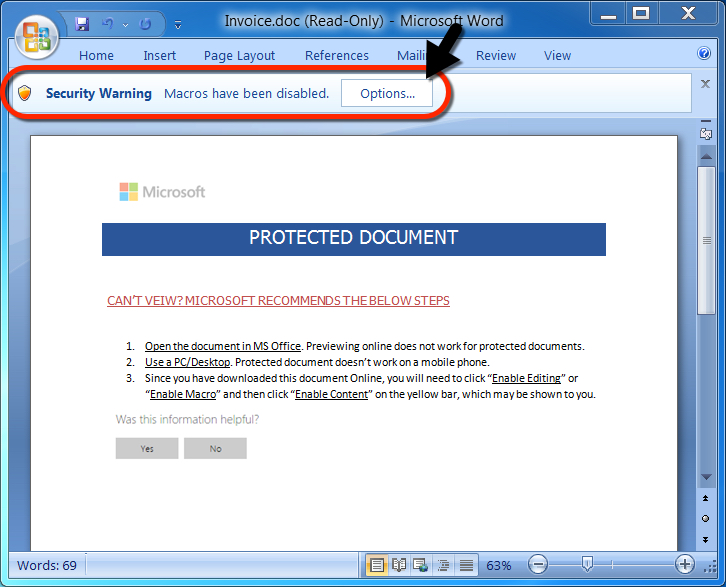
Shown above: After entering the password, a victim must enable macros.

Shown above: Traffic from an infection filtered in Wireshark.
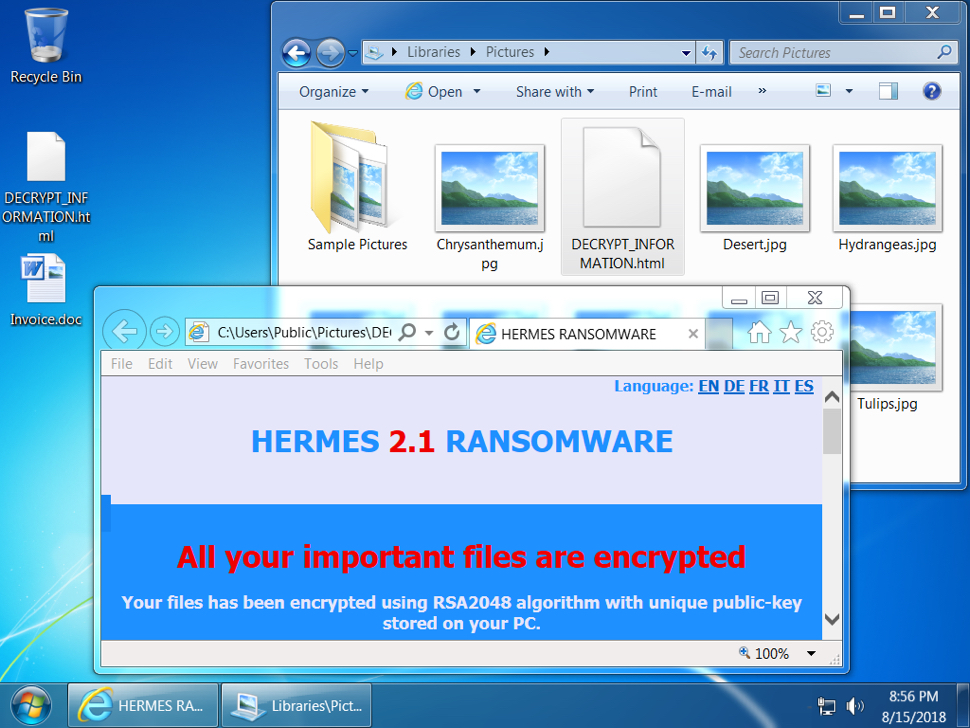
Shown above: Desktop of an infected Windows host.
Indicators
Malspam information from 5 email samples:
- Date: Wednesday 2018-08-15
- Received: from 180connection.org ([46.161.42.24])
- Received: from 10000tables.org ([46.161.42.9])
- Received: from 160h.com ([46.161.42.21])
- Received: from 135798.com ([46.161.42.18])
- Received: from whygavs.net ([46.161.42.20])
- From: Karan Fabiano =?UTF-8?B?wqA=?= <[email protected]>
- From: Eloisa Liechty =?UTF-8?B?wqA=?= <[email protected]>
- From: "Edgar Blanding =?UTF-8?B?wqA=?=" <[email protected]>
- From: "Jackqueline Wroblewski =?UTF-8?B?wqA=?=" <[email protected]>
- From: "Toni Cerulli =?UTF-8?B?wqA=?=" <[email protected]>
- Subject: Invoice Due
- Attachment name: Invoice.doc
Network traffic:
- 209.141.59.124 port 80 - 209.141.59.124 - GET /azo.exe
- 149.129.216.194 port 80 - briancobert.com - POST /index.php (AZORult traffic)
- 149.129.216.194 port 80 - briancobert.com - POST /index.php (AZORult traffic)
- 209.141.59.124 port 80 - 209.141.59.124 - GET /hrms.exe
Associated malware:
- SHA256 hash: 05e3783379157ed6bdc936f306d14b23927b6f682273d37f490349990532c305
- File size: 38,440 bytes
- File description: Password-protected Word doc from malspam with macro for malware
- SHA256 hash: a7b8e4988e9da83ac55b4613bff4bccca62e208c2fed0c850ca024163b27dc09
- File size: 348,160 bytes
- File location: hxxp://209.141.59.124/azo.exe
- File location: C:\Users\[username]\AppData\Local\Temp\qwerty2.exe
- File description: First-stage malware, AZORult
- SHA256 hash: 2698c141c7fb2660fd009ce9c083022a531c28c8ae8258555027a2f7852de13d
- File size: 348,160 bytes
- File location: hxxp://209.141.59.124/hrms.exe
- File location: C:\Users\[username]\AppData\Local\Temp\hrms.exe
- File description: Second-stage malware, Hermes ransomware
Contact info from the decryption instructions:
- primary email: [email protected]
- reserve email: [email protected]
Final words
As usual, properly-administered and up-to-date Windows hosts are not likely to get infected. System administrators and the technically inclined can also implement best practices like Software Restriction Policies (SRP) or AppLocker to prevent these types of infections.
Pcap and malware associated with today's diary can be found here.
---
Brad Duncan
brad [at] malware-traffic-analysis.net


Comments