Adobe Flash 0-Day Used Against South Korean Targets
the Koren CERT announced that it is aware of a so far unpatched Adobe Flash vulnerability that is being exploited in targeted attacks [1]. All versions of Adobe Flash Player including 28.0.0.137 are vulnerable. 28.0.0.137 was released in January as part of Adobe's normal patch Tuesday. Adobe has not yet released an advisory, and the only confirmation so far is a twitter post from a Korean security researcher [2]. [See update below about Adobe's advisory]
According to KrCERT's advisory, the exploit can be included in a Microsoft Office document or a web page. As a workaround, KrCERT recommends disabling or uninstalling the Flash Player. Firefox appears to be not vulnerable to the web-based exploit.
Update: Adobe just released a security advisory [3]. The vulnerability, CVE-2018-4878, will be fixed with next weeks update.
[1] https://www.krcert.or.kr/data/secNoticeView.do?bulletin_writing_sequence=26998
[2] https://twitter.com/issuemakerslab/status/959006385550778369
[3] https://helpx.adobe.com/security/products/flash-player/apsa18-01.html
---
Johannes B. Ullrich, Ph.D. , Dean of Research, SANS Technology Institute
STI|Twitter|
Adaptive Phishing Kit
Phishing kits are everywhere! If your server is compromised today, they are chances that it will be used to mine cryptocurrency, to deliver malware payloads or to host a phishing kit. Phishing remains a common attack scenario to collect valid credentials and impersonate the user account or, in larger attacks, it is one of the first steps to compromise the final target. Phishing kits are usually mimicking well-known big Internet players (eBay, Paypal, Amazon, Google, Apple, Microsoft…[add your preferred one here]). I found an interesting phishing kit which adapts itself to the victim. Well, more precisely, it adapts to the victim email address.
The mail received is a warning about a mailbox that reached its storage quota:
From: EMAIL ADMIN Subject: NOTIFICATION - Storage Full To: [email protected] Dear [email protected], Your email has used up the storage limit of 99.9 gigabytes as defined by your Administrator. You will be blocked from sending and receiving messages if not re- validated within 48hrs. Kindly click on your email below for quick re-validation and additional storage will be updated automatically [email protected] Regards, E-mail Support 2018.
This is a classic approach: to make the victim fear that he/she will lose access to a service. The email address in the mail body is a link that points to:
http://www.[redacted].com/sec/domainz/domainz/domainz/%40%26%25%40%25*%40()!%[email protected]
The URL is not publicly available because the compromised website is quite sensitive. We contacted the owner to request a cleanup.
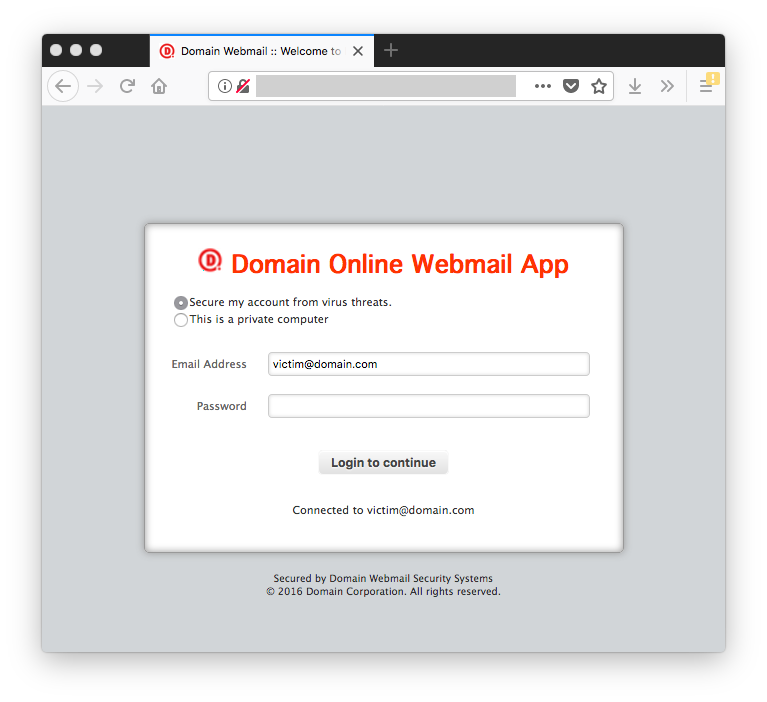
You can see the string “Domain” added to the login page title, as well as a small icon and a favicon. In fact, this is the favicon grabbed from the victim’s email address domain:
Let’s try with another email address from the ISC:
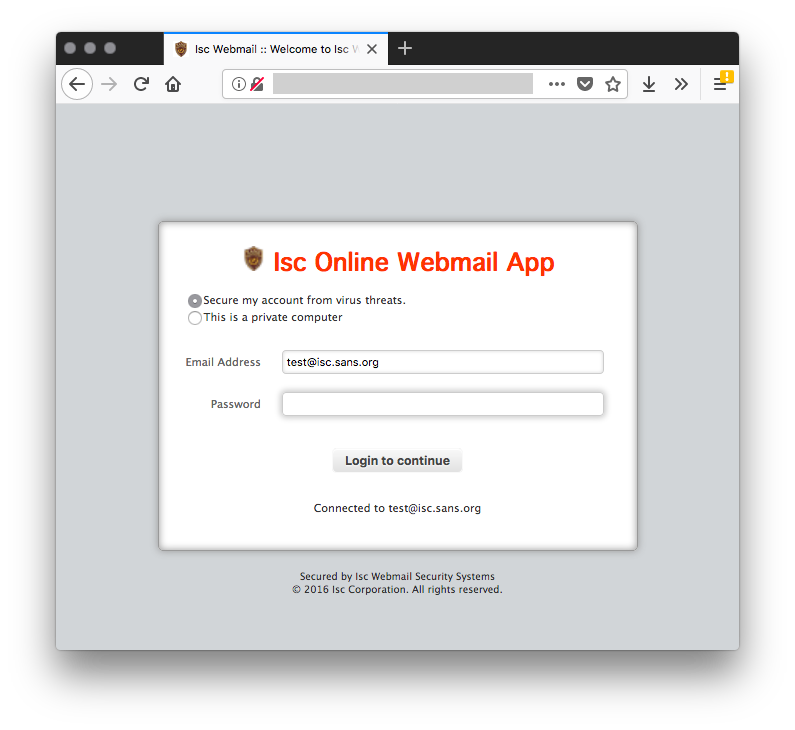
Based on my tests, the phishing kit extracts the first word of the email address (before the first ‘dot’) and capitalize the word:
@isc.sans.edu returns "Isc"
@gmail.com returns "Gmail"
function getDomainFromEmail($email)
{
// Get the data after the @ sign
$domain = substr(strrchr($email, "@"), 1);
return $domain;
}
It grabs the favicon from the email address domain and re-uses it on the fake webpage. This is a simple but cool way to make the webpage more attractive.
The attack has 3 steps:
- Collect email / password
- Collect the phone number
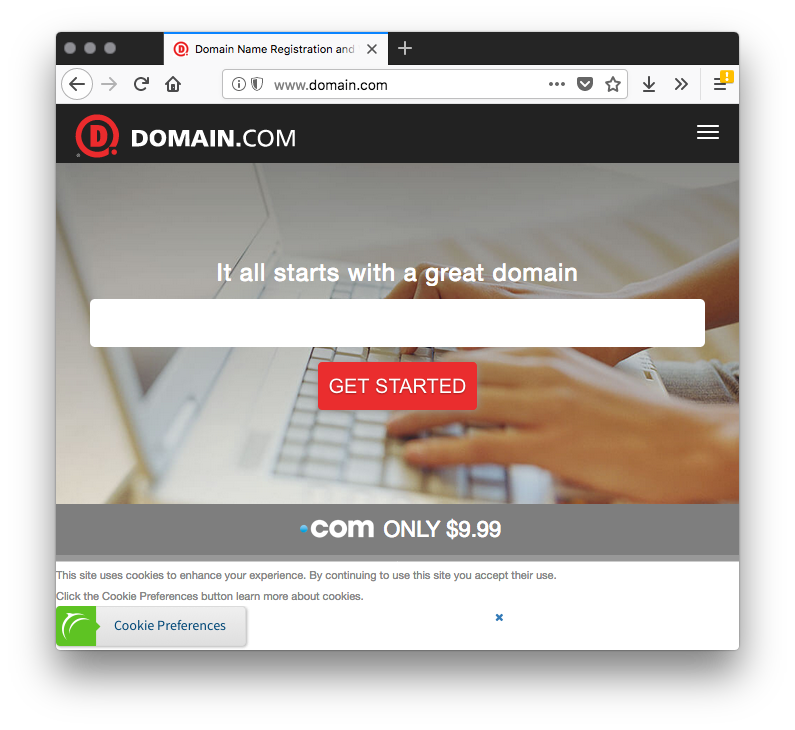
- Redirect to the original website (based on the email address)
This is not a brand new kit. I found some references back to 2016. Based on the files, I also found other compromised websites. But it remains very simple and the fact to display the domain & logo (the favicon) to the victim might increase chances of success (from the attacker’s perspective). Stay safe!
Xavier Mertens (@xme)
ISC Handler - Freelance Security Consultant
PGP Key


Comments