Phish or scam? - Part 1
Reader Carlos Almeida submitted an email with a .docx attachment.
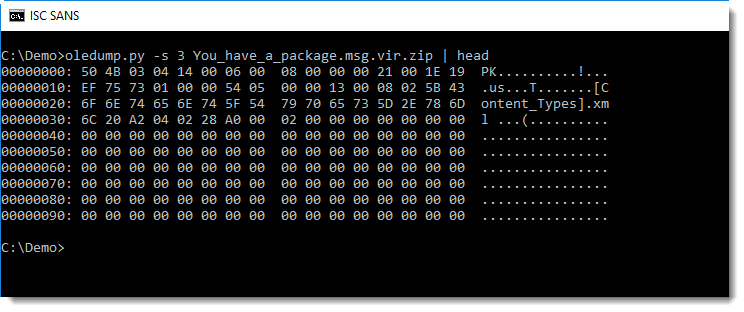
As MSG files are Compound File Binary Format files, we can use oledump to start analyzing this email.
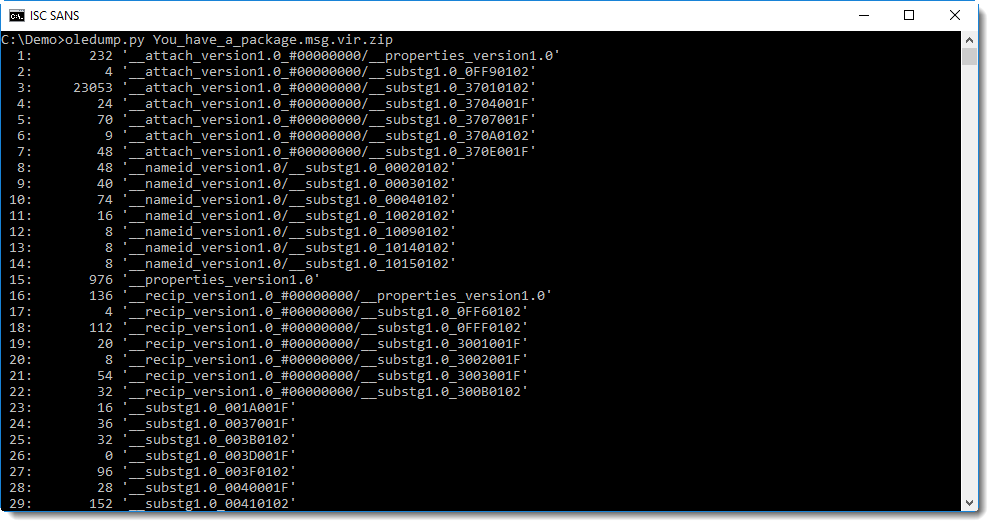
The hexadecimal codes in the stream names are an indication of the purpose and type of the stream data. I developed a new oledump plugin to identify streams in MSG files:
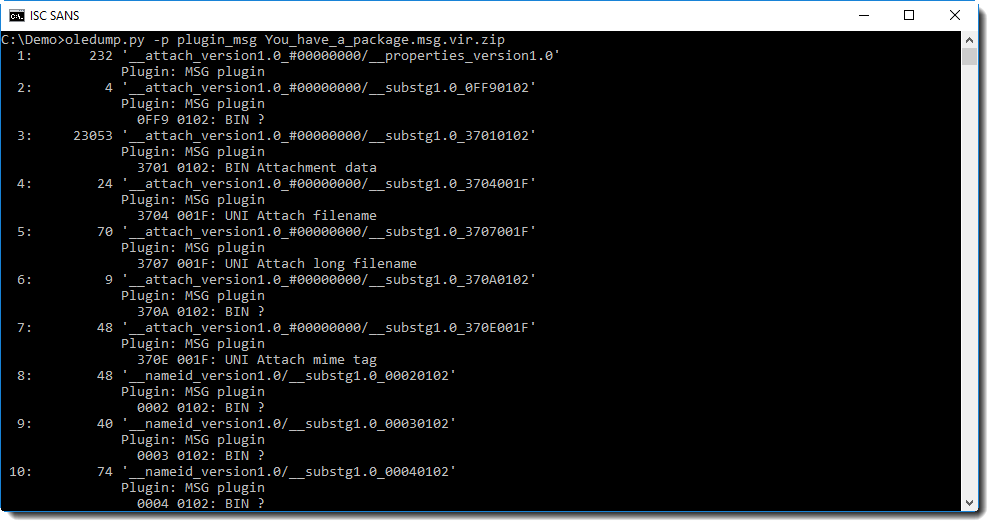
A condensed overview can be obtained using option -q (quiet):
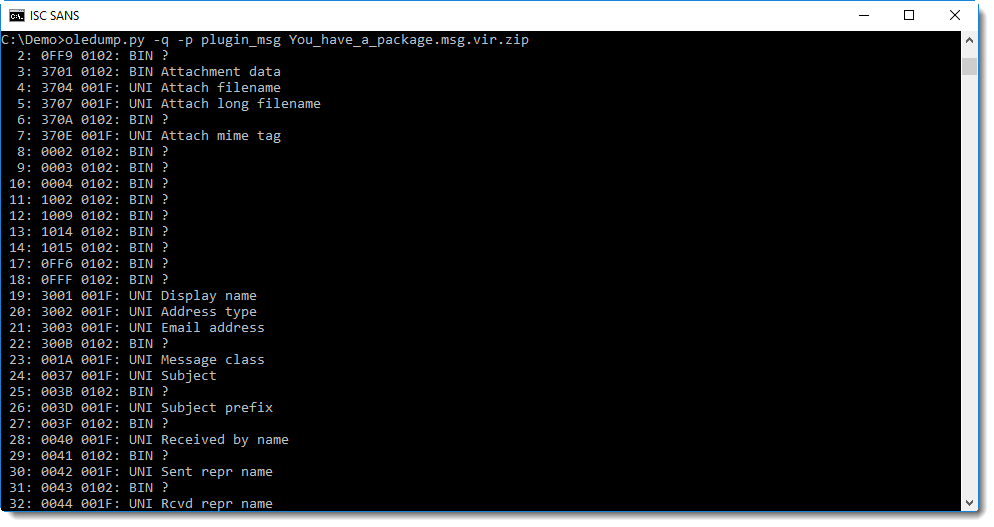
The first column after the hexadecimal data tells us what the data type is: BINary, UNIcode or ASCii.
And the last column informs us about the purpose of the data stream.
Let's take a look at some, like:
- the subject:
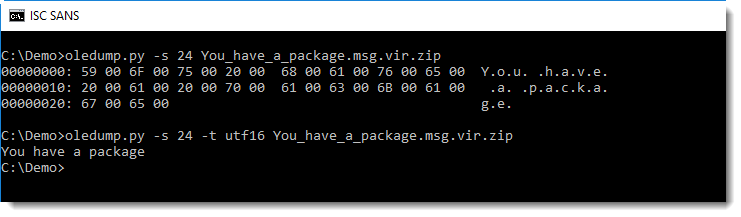
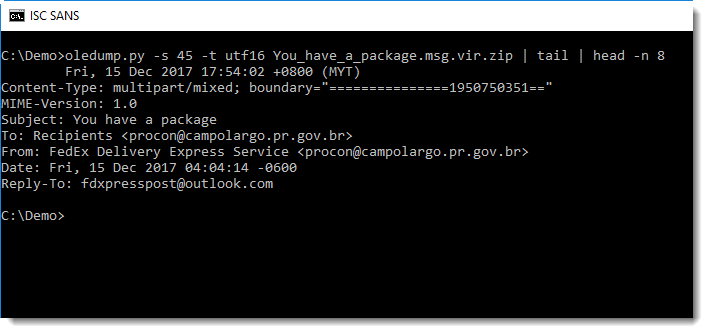
Since the data type is UNICODE, we use oledump's option -t to decode the content as UTF16.
- the headers:
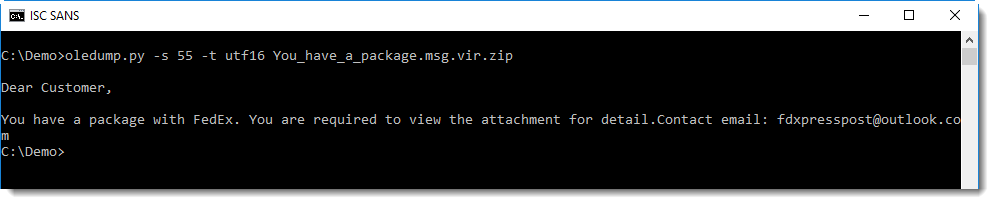
- the message body:
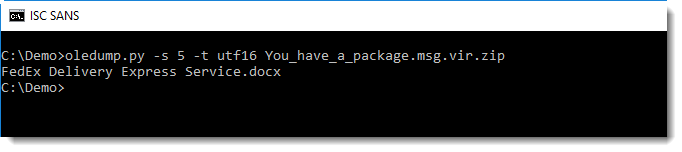
The attachment looks to be a .docx file:
We can analyze this attachment with zipdump:
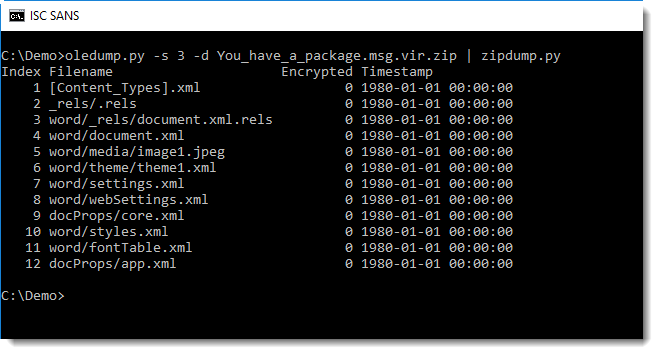
This looks indeed like a Word document without macros.
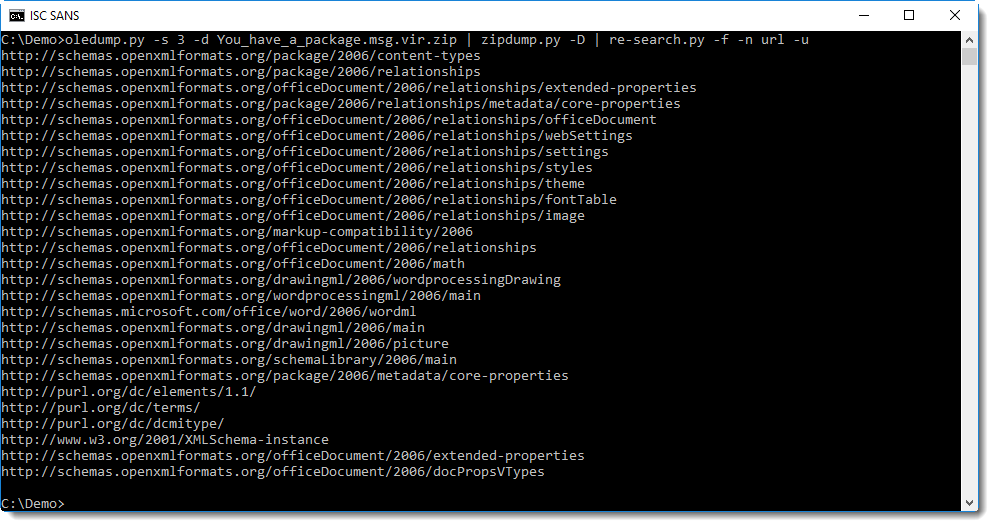
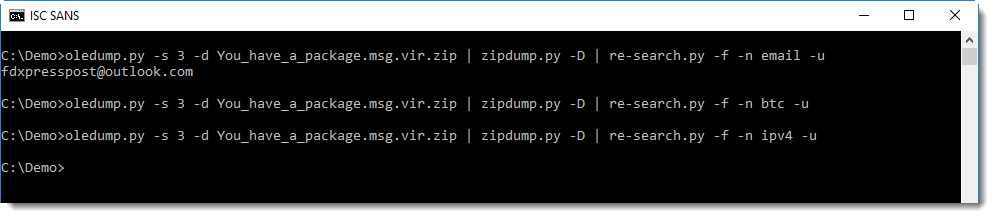
With re-search, we can search through the XML files for URLS, email addresses, BTC addresses and IPv4 addresses.
We don't find any suspicious URLs:
Just a suspicious email address:
Now it would be useful to read the content of the Word document, without actually having to open it in Word. That's what we'll do in the next part of this diary entry.
Stay tuned.
Didier Stevens
Microsoft MVP Consumer Security
blog.DidierStevens.com DidierStevensLabs.com


Comments