IR using the Hive Project.
Request Tracker Incident Response (RTIR) is one of the most popular IR ticketing systems. Its a open source project based on perl and MySQL. While it meets all your typical ticket tracking items, it needs lots of customization to meet your SOC needs. A few months ago I came across a project called TheHive (https://thehive-project.org/) that is a scalable open source platform.
The frontend is written in AngularJS and the backend is Elastic Search. The platform has the ability to create tickets, organize workflow, track indicators, import data about indicators from other sources and export it into MISP. The group of guys that are developing this are doing an amazing job of fixing bugs and adding new features to the system on a monthly basis.
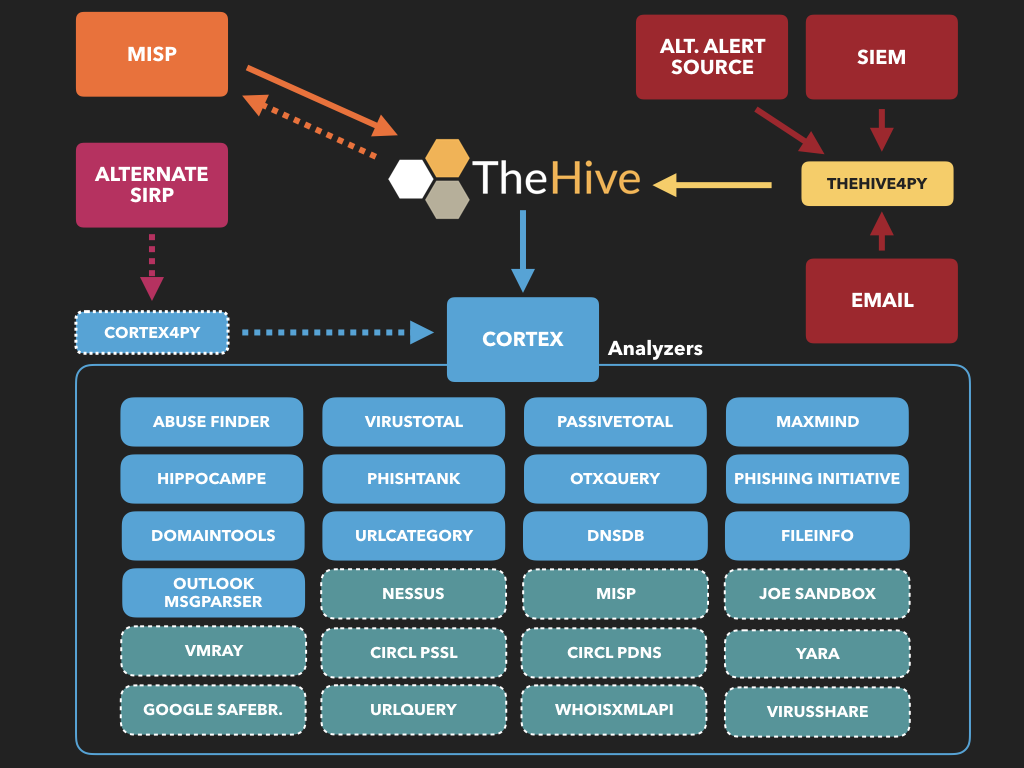
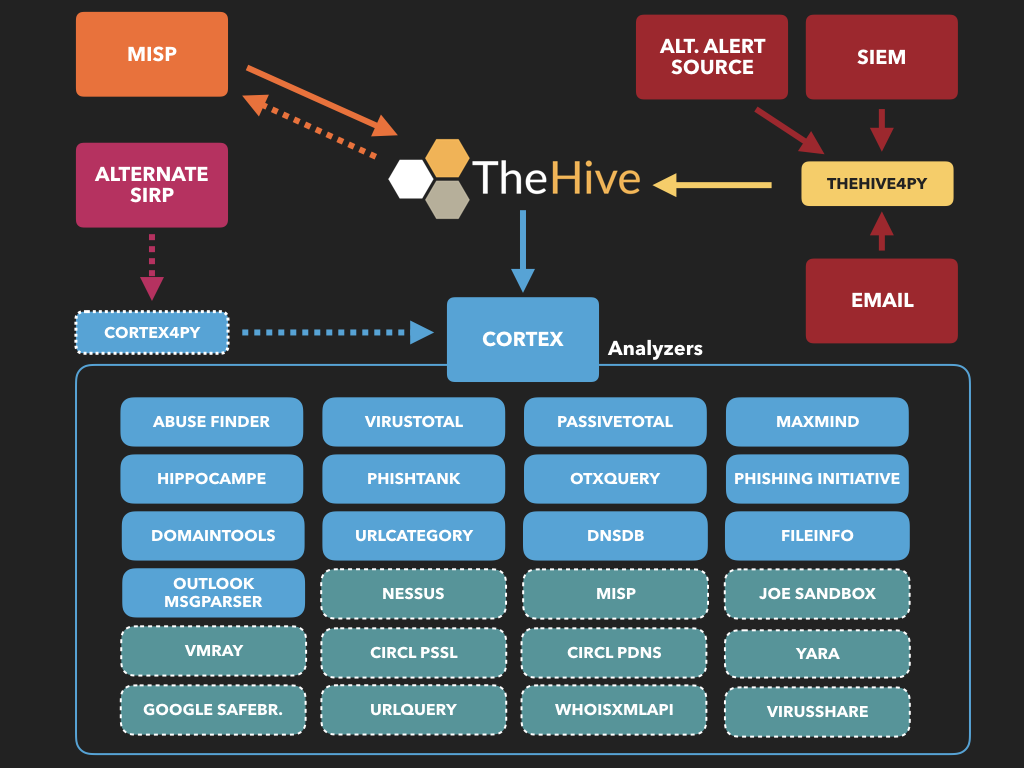
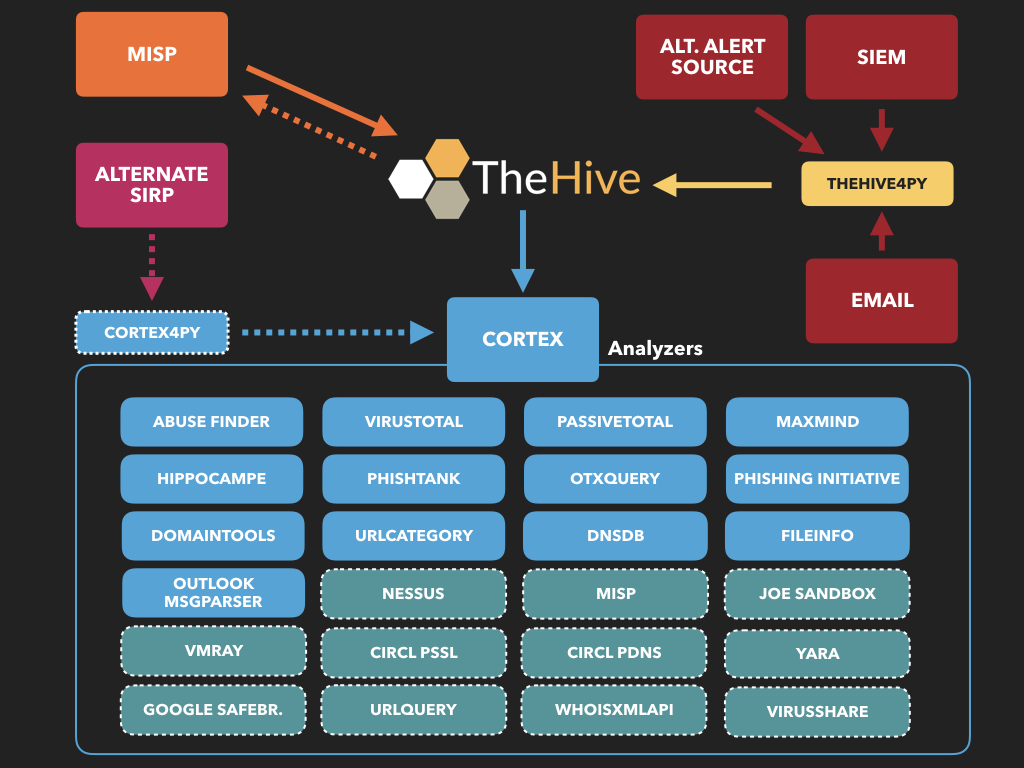
The hive has several other components that should be leveraged to give you the power of the overall system. These components are Cortex and Hippocampe.
They have several ways to get started. They have a set Docker Images, a test VM, and you can download from source and install. I'd start with the VM or Docker just to get a feel for it.
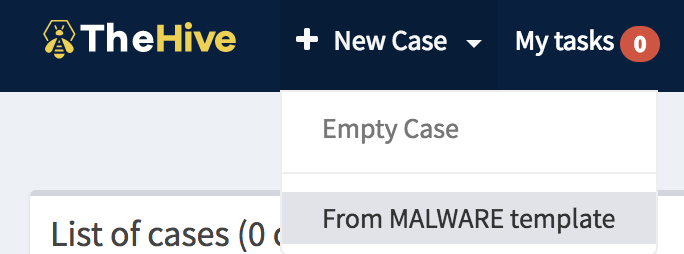
Basic GUI workflow:
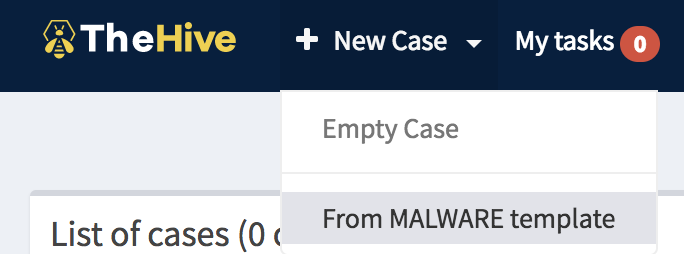
To create a new cause using a template select new case and the template you want.
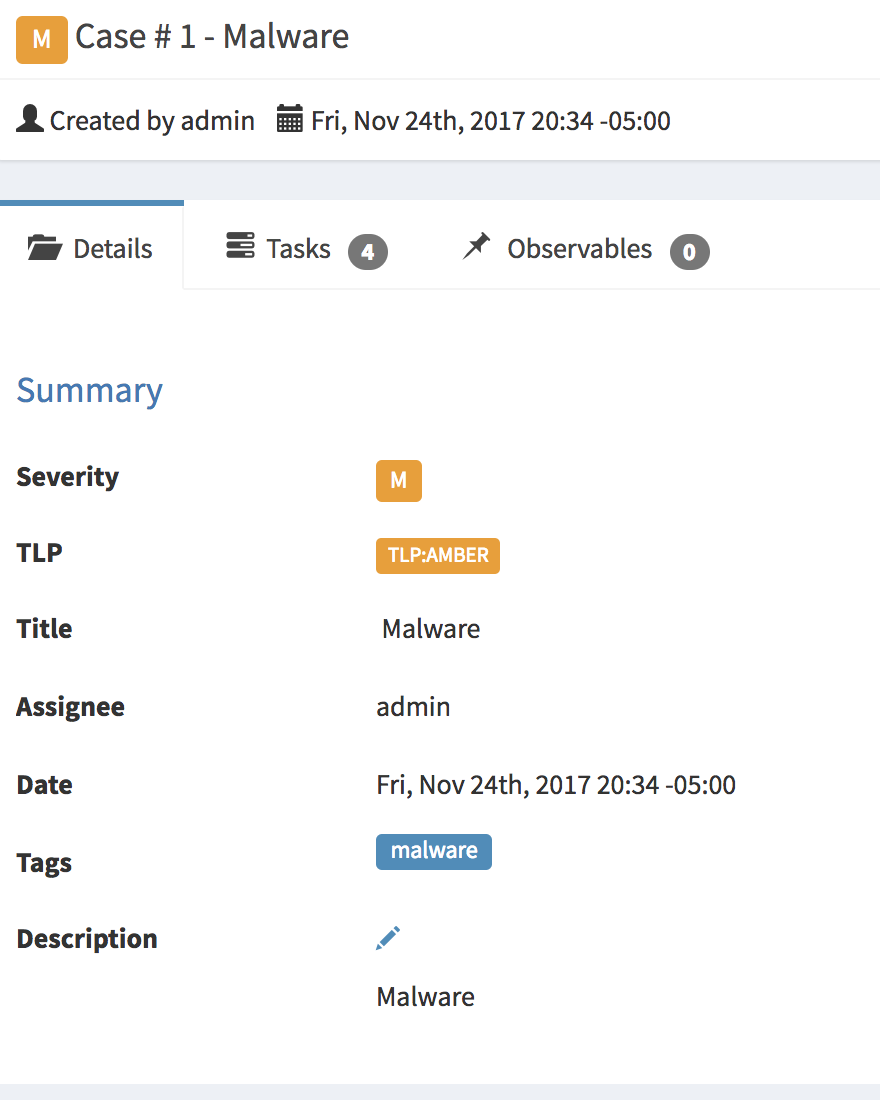
The initial details page is filled with whatever you set up for the template, new tags and any additional information can be added.
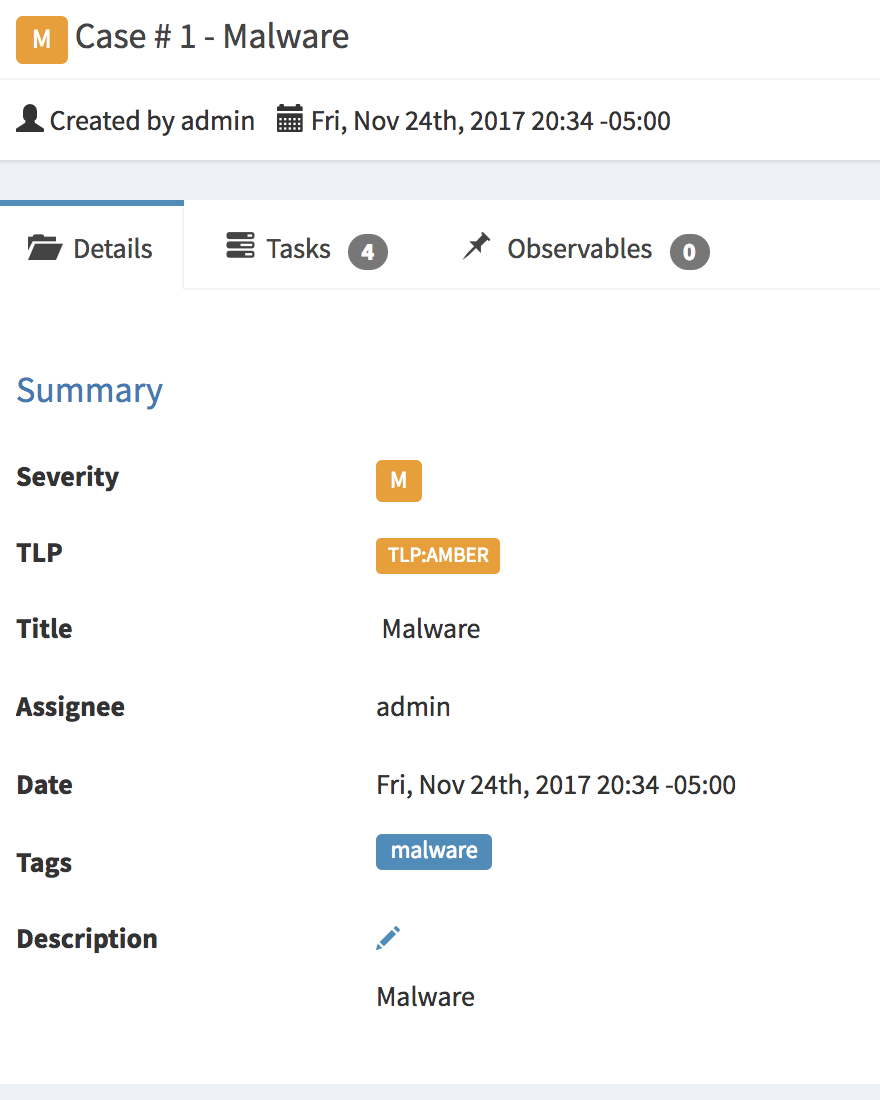
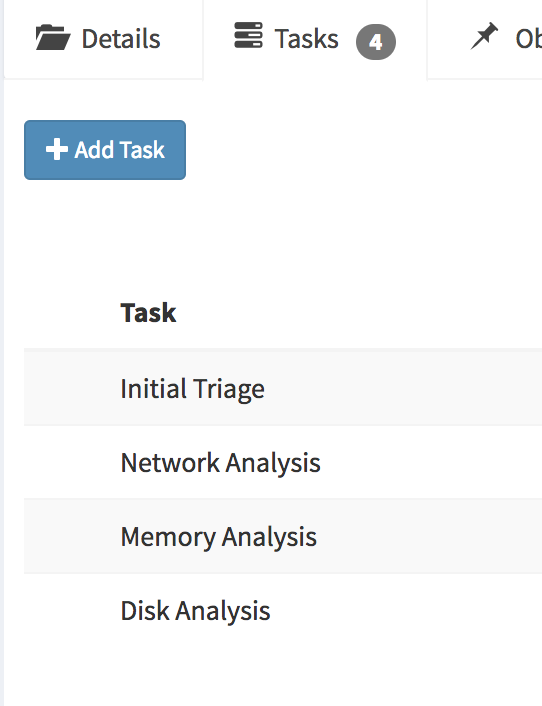
Tasks is where you put your case notes. You can have it broken out by the 6 stages of IR, by tools, or playbook processes. Within the tasks you can have the IR processes documented to go along with the task itself.
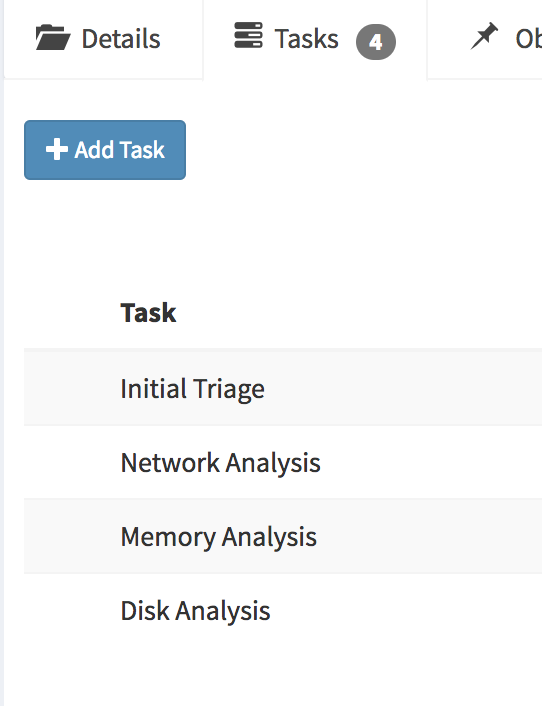
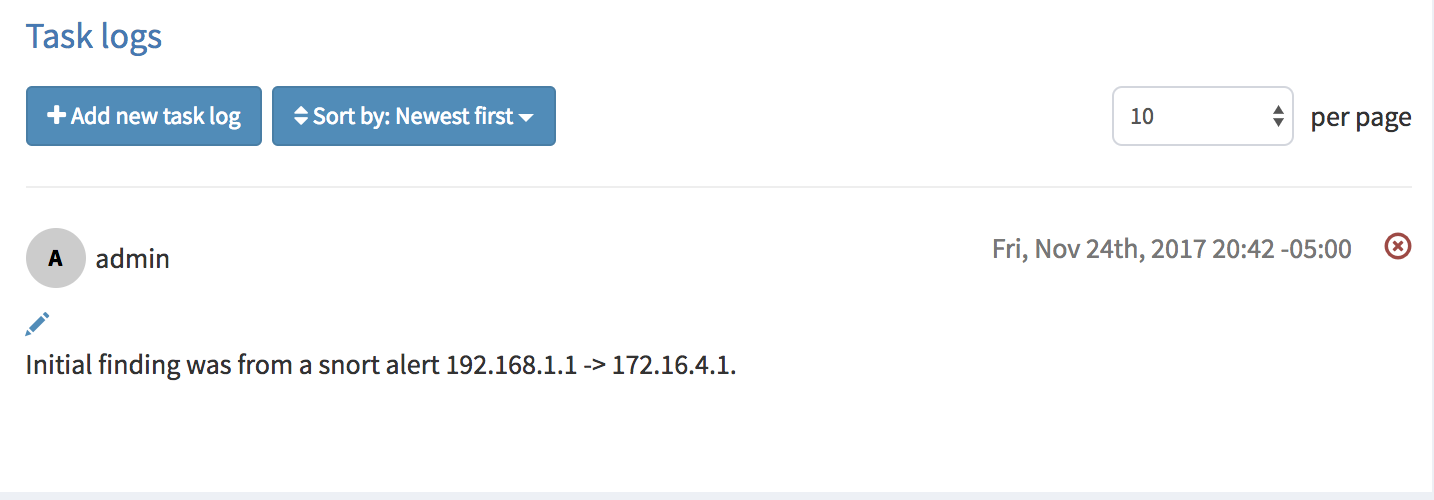
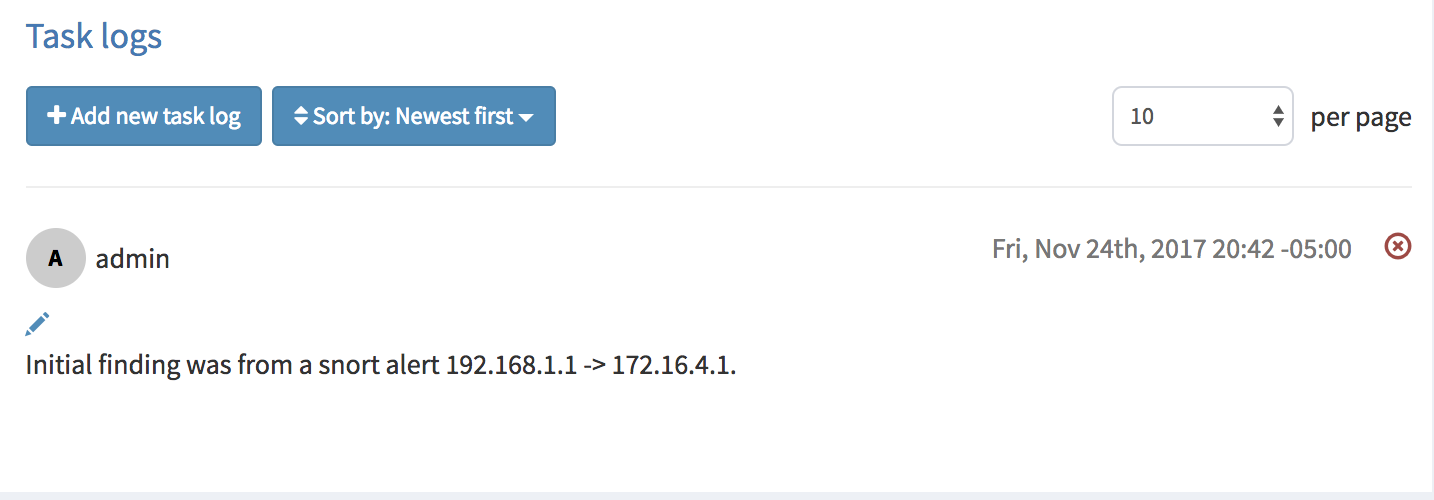
Select the task you are working and then add a new task log to document your findings.
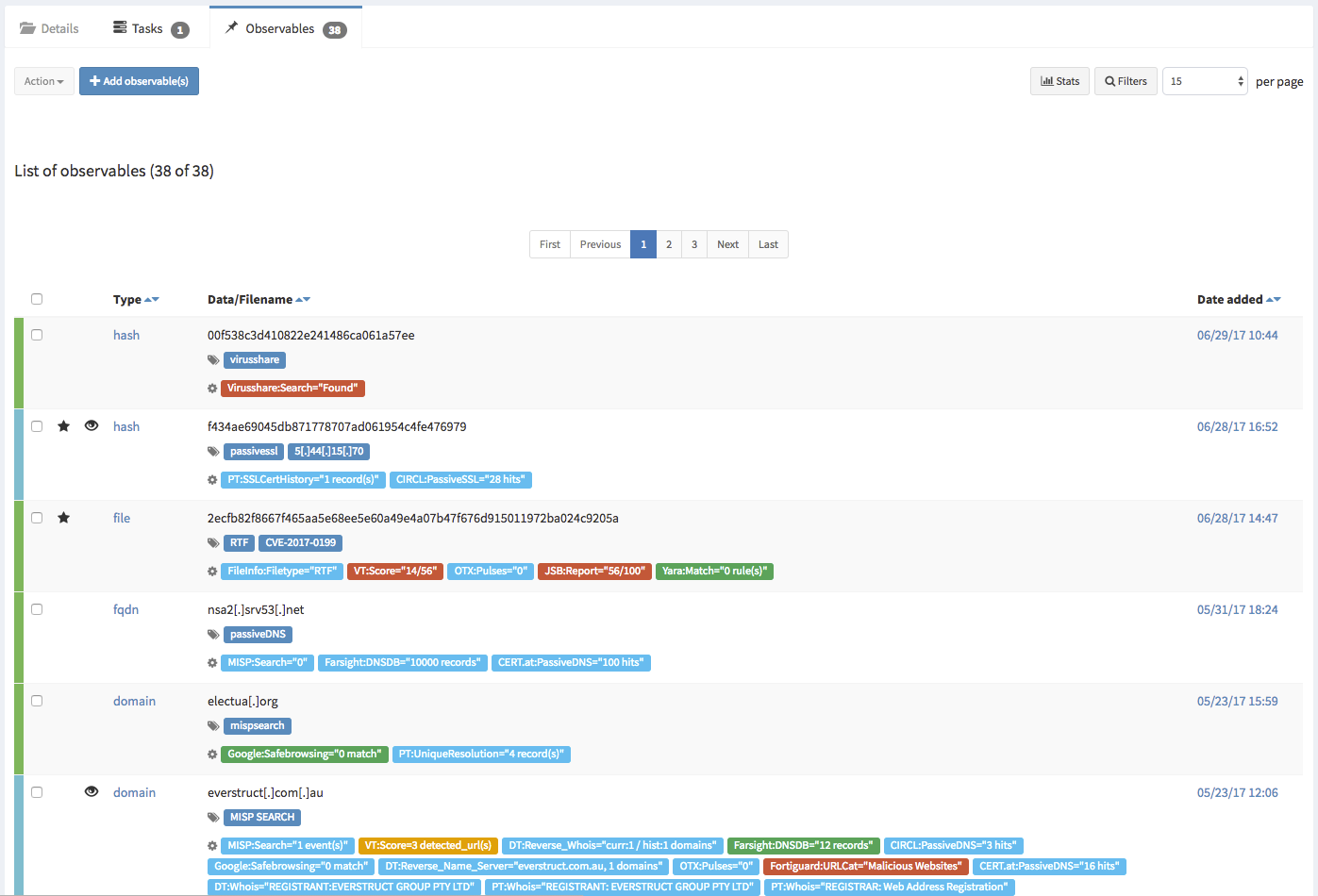
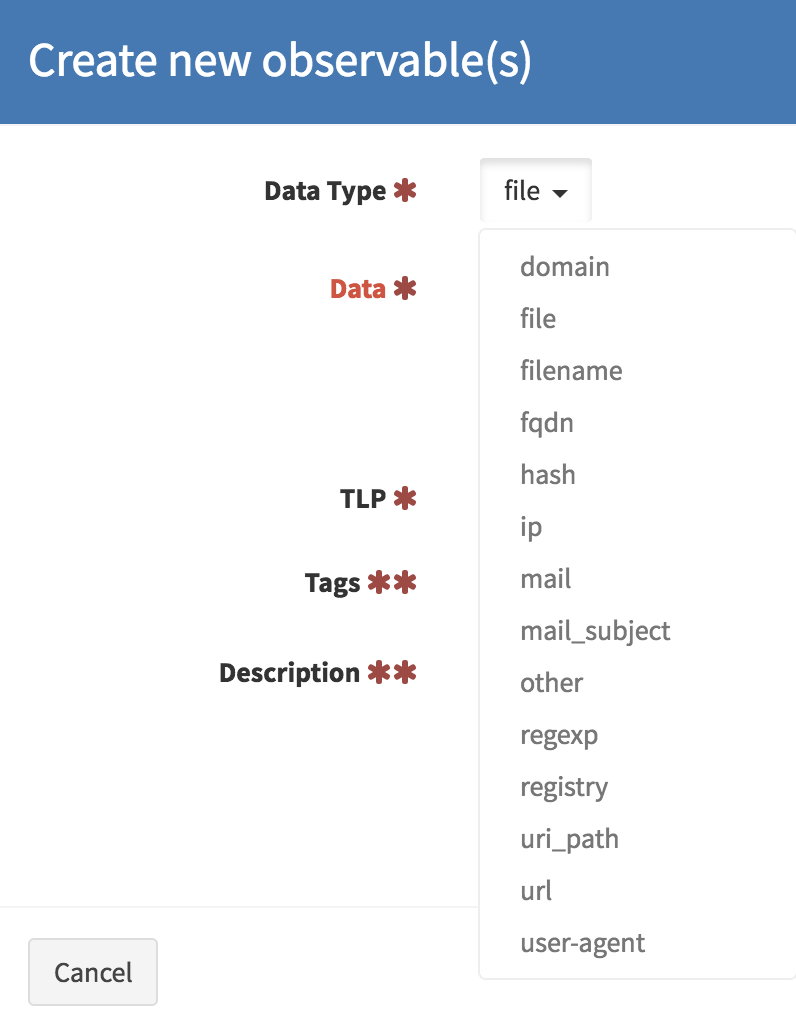
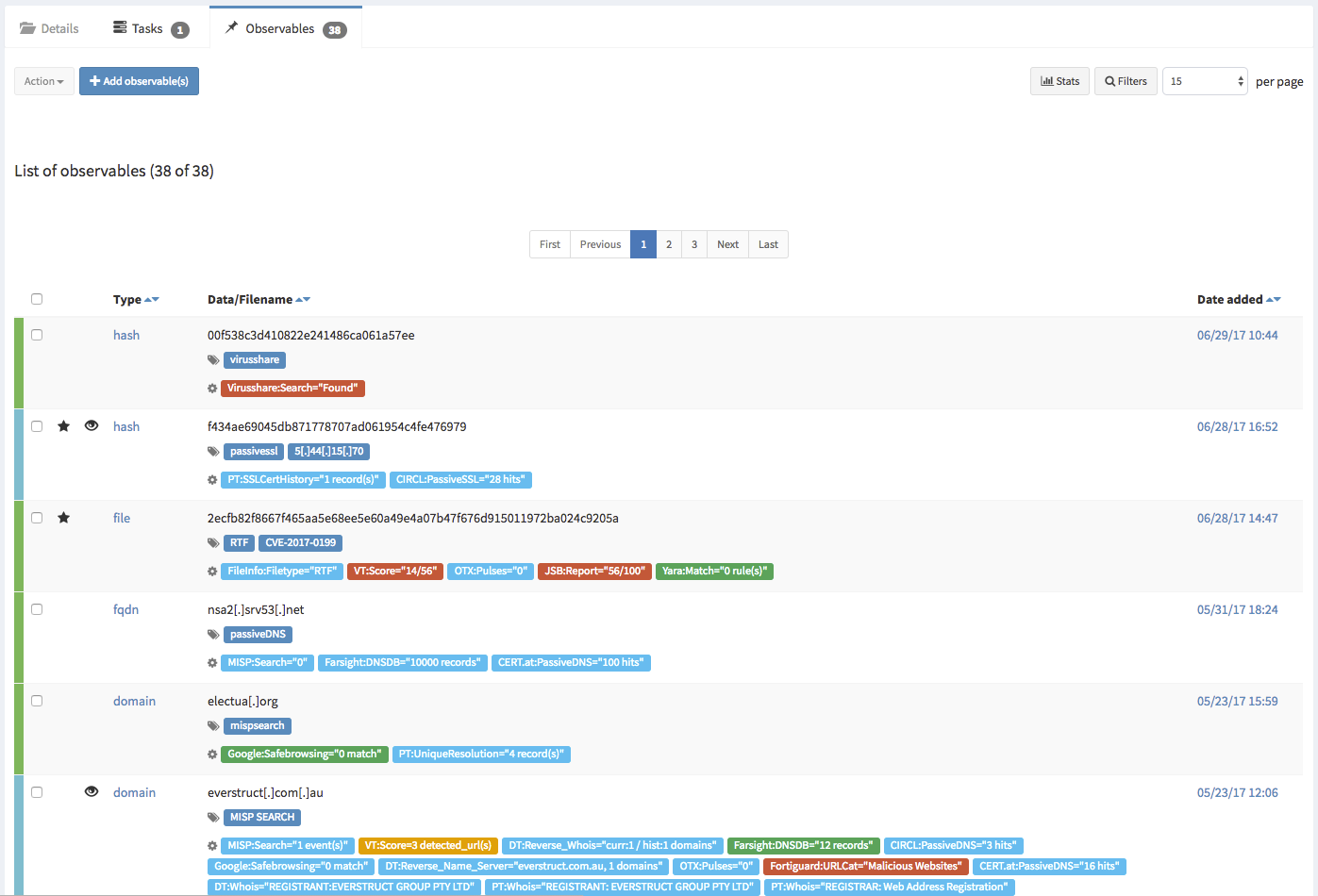
TheHive definitely meets the requirement for for logging,tracking, tracking. You can also add metrics that are required before the case is closed. What make this system great is the ability to add your IOC’s into the case, additionally if will tell you any other case that also has this IOC’s for better tracking.
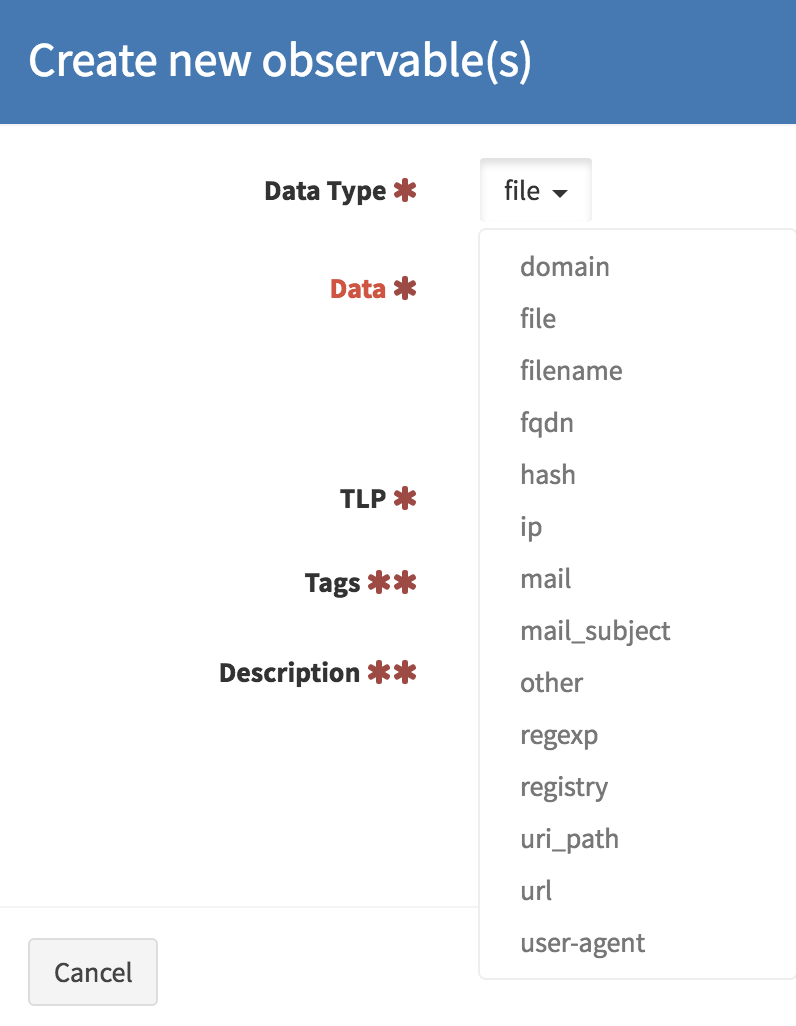
Once you add in your IOC, you can ran analyzers in Cortex against the data and it will automatically be added to the case. They have 30 analyzers currently you can setup and use.
I have just scratched the surface of the tool, they do a great job of documentation and you should check out their blog https://blog.thehive-project.org for lots more information.
--
Tom Webb
@twsecblog


Comments