Black Hat is coming and with it a good reason to update your "Broadcom-based" devices
Black Hat US 2017 is debuting and with it a potential concern to most of us. It turns out that one of the conference presentations, entitled BROADPWN: REMOTELY COMPROMISING ANDROID AND IOS VIA A BUG IN BROADCOM’S WI-FI CHIPSETS [1], will detail how Broadcom BCM43xx Wi-Fi chipsets can be exploited to achieve full code execution on the compromised device without user interaction.
“An attacker within range may be able to execute arbitrary code on the Wi-Fi chip”, says Apple about this vulnerability (CVE-2017–9417) in its latest security bulletin [2]. Google published the patch to fix the vulnerability on Android early this month [3].
Besides Apple, those chipsets are present on most smartphone devices like HTC, LG, Nexus and most Samsumg models as well. Make sure to have this vulnerability fixed in all your devices?—?especially if you are planning to be in Las Vegas next week.
References
[1] https://www.blackhat.com/us-17/briefings.html#broadpwn-remotely-compromising-android-and-ios-via-a-bug-in-broadcoms-wi-fi-chipsets
[2] https://support.apple.com/pt-br/HT207923
[3] https://source.android.com/security/bulletin/2017-07-01
--
Renato Marinho
Morphus Labs | LinkedIn | Twitter
Malicious .iso Attachments
We've been informed of recent malware campaigns that deliver .iso attachments (.iso files are CD/DVD images). These .iso files contain a malicious executable.
Since Windows 8, Windows will automatically mount .iso files when they are opened. Like this, these .iso files are like .zip files with malware.
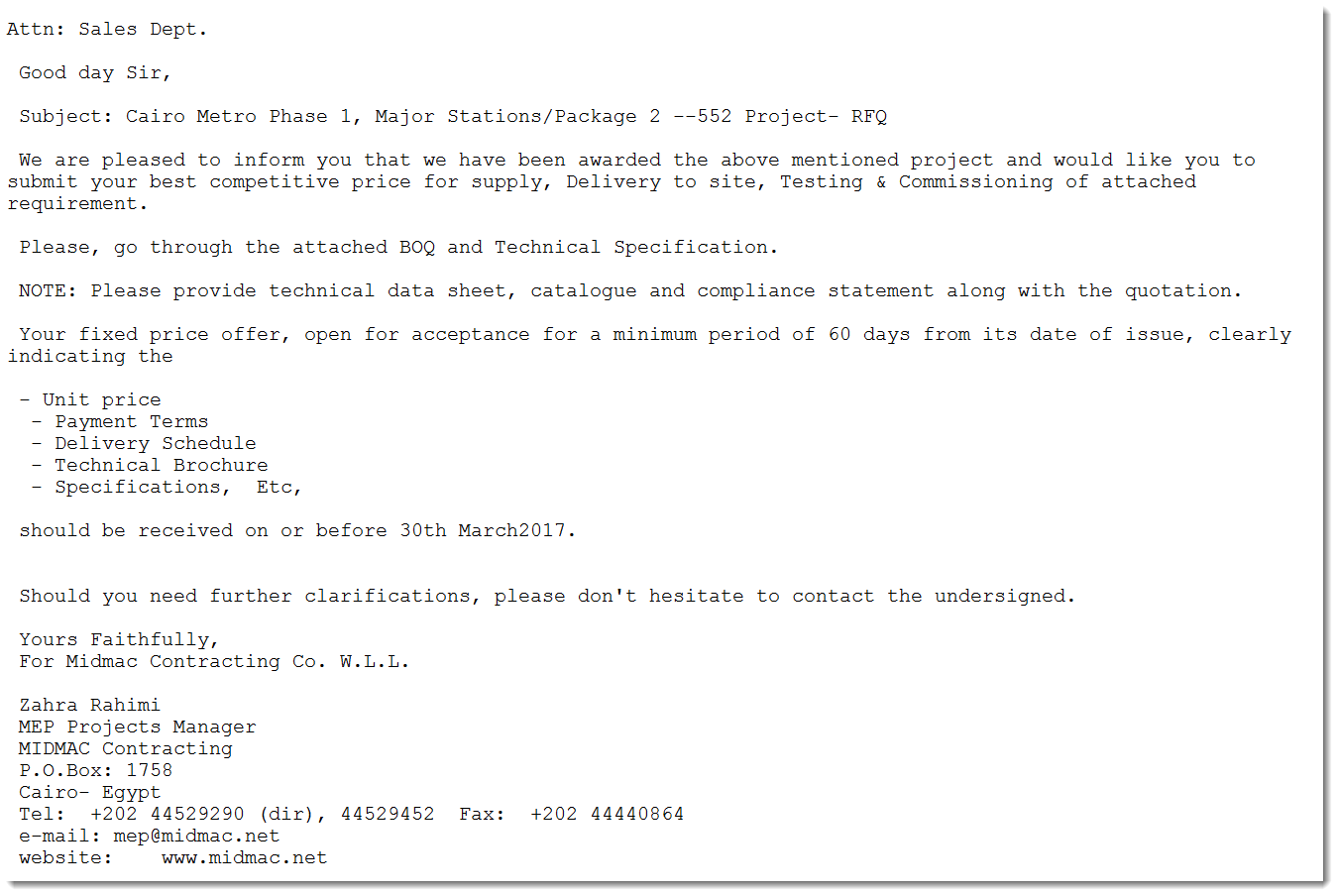
Here is an example of an email with .iso attachment:
This email file can be analyzed with emldump:
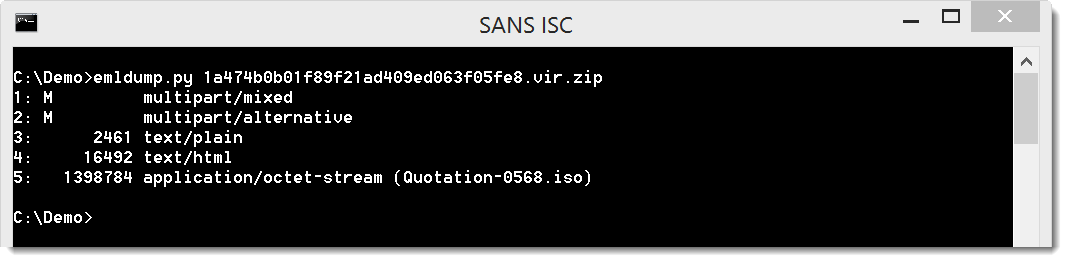
Part 5 contains the attached .iso file (Quotation-0568.iso), and can be extracted like this:
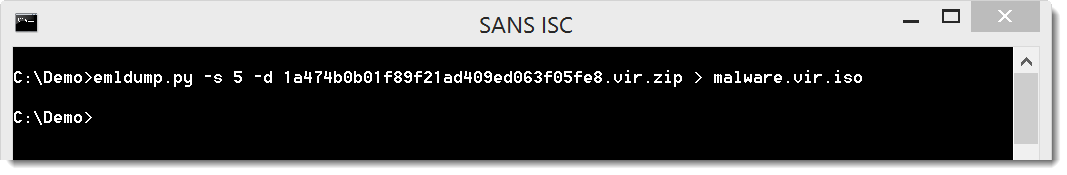
There are several methods to analyze .iso files, even with Python. Here we will use 7-Zip:
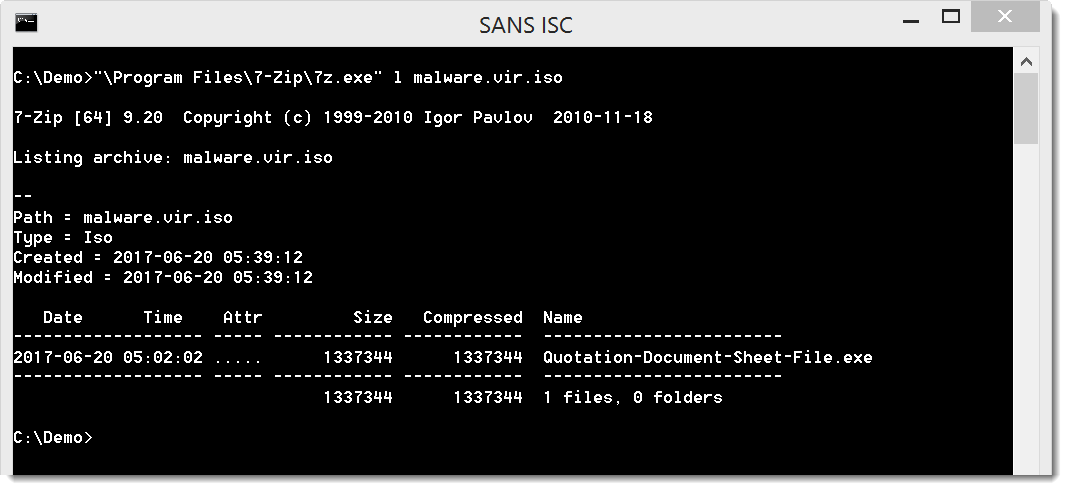
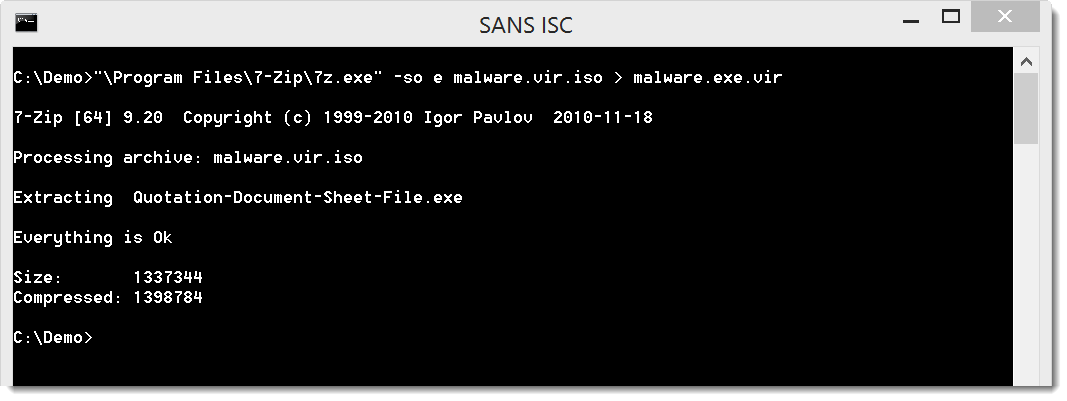
The executable can be extracted like this:
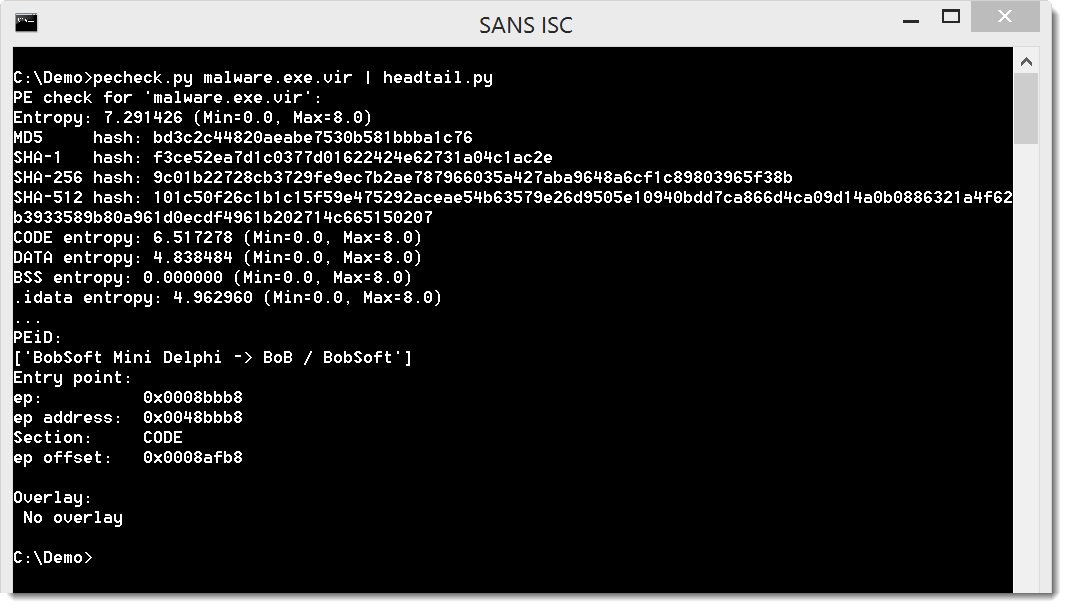
It is indeed a PE file:
Didier Stevens
Microsoft MVP Consumer Security
blog.DidierStevens.com DidierStevensLabs.com


Comments