Resources: Windows Auditing & Monitoring, Linux 2FA
Some useful resources for your reading pleasure and implementation:
1) A recently published Windows 10 and Windows Server 2016 security auditing and monitoring reference: https://www.microsoft.com/en-us/download/details.aspx?id=52630
From the reference abstract, you can expect:
- Detailed technical descriptions for most of the advanced security audit policies that are included with Windows 10 and Windows Server 2016.
- Monitoring recommendations for security events to include in advanced security audit policies.
- Recommendations for Group Policy settings for advanced security audit policy for domain controllers, workstations, and member servers.
2) A great Linux.com article on setting up two-factor authentication for login and sudo: https://www.linux.com/learn/how-set-2-factor-authentication-login-and-sudo
From Jack Wallen's article:
"What if I told you could take the login to your Linux servers and desktops one step—nay, two steps—further? Thanks to the Google Authenticator, you can. On top of that, it’s incredibly easy to set up. I am going to walk you through the process of setting up two-factor authentication for use on login and sudo. I will demonstrate this on a Ubuntu 16.04 desktop, but the process works for the server as well. To handle the two-factor side of things, I will be making use of the Google Authenticator..."
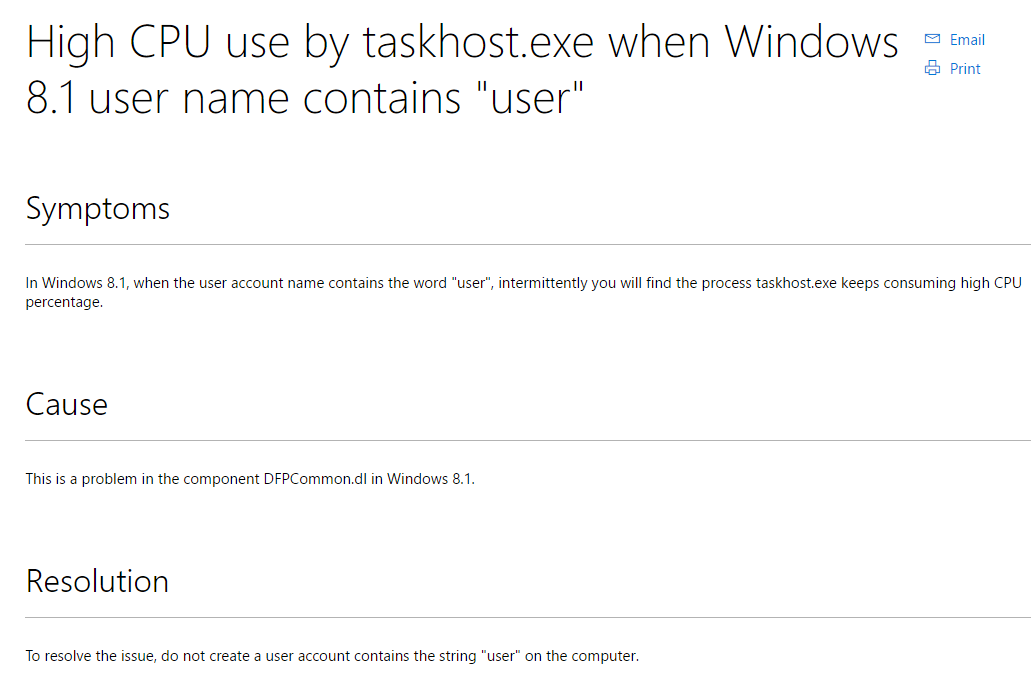
3) In the "this speaks for itself" and "too good not to share" categories: https://support.microsoft.com/en-us/kb/3053711
![]()


Comments