RFC 6598 - Carrier Grade NAT
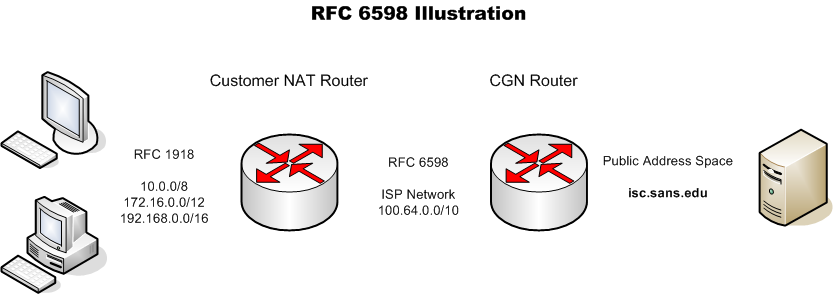
Three years ago Johannes published a diary on Reserved IP Address Space with a complete list of reserved IPv4 address that obviously included the well-known as well as some new one such as RFC 6598 (released in April 2012) "[...] to accommodate the needs of Carrier-Grade NAT (CGN) devices."[1] The address space reserved for CGN is 100.64.0.0/10 which is used to counter the IPv4 address shortage by putting multiple hosts in a private subnet behind a public IP address.
Here is a simplified illustration of CGN:
If you are curious as to whether you carrier is using RFC 6598 CGN addresses, you can check your logs or traffic (packets) for 100.64.0.0/10.
[1] https://tools.ietf.org/html/rfc6598
[2] https://isc.sans.edu/forums/diary/Reserved+IP+Address+Space+Reminder/13228
-----------
Guy Bruneau IPSS Inc.
Twitter: GuyBruneau
gbruneau at isc dot sans dot edu


Comments