Querying the DShield API from RTIR
A few days ago, Tom wrote a diary(1) about RTIR(2) and its REST API. He explained how the tool can be fulfilled with external data. Being a DShield contributor for years (I submit my firewall logs), I like to search for IP addresses information in the DShield database. By default, RTIR extracts IP addresses from tickets and has an interface to query services like WHOIS servers, to perform a traceroute or to query any third-party website. RTIR being extremely configurable, why not extend it to query the DShield database using the ISC API(3)!
If IP addresses can be queried via the URL "https://isc.sans.edu/ipinfo.html?ip=x.x.x.x", don't do this. First of all for performance reasons but the page cannot be displayed in an iframe (that's the case in RTIR) because it sets the 'X-Frame-Options' to 'SAMEORIGIN'. To query details of an IP address, use the following IP API call:
https://isc.sans.edu/api/ip/x.x.x.x
Results are returned in XML. To integrate DShield lookups into RTIR, follow this procedure.
1. Create a new page called "isc_ipinfo.php" in your Apache server running RTIR (or any available HTTP server). This page will receive the IP address, query the DShield API and reformat (basically) the XML output:
$ip = $_GET['ip'];
if (!filter_var($ip, FILTER_VALIDATE_IP)) {
echo "Invalid IP address!";
exit;
}
$d = simplexml_load_file('https://isc.sans.edu/api/ip/'.$ip);
?>
<table>
<tr><td align="right"><b>IP Address:</b></td><td><?php echo $d->ip; ?>(<a href="https://isc.sans.edu/ipdetails.html?ip=<?php echo $ip ?>" target="_blank">Details</a>)</td></tr>
<tr><td align="right"><b>Network:</b></td><td><?php echo $d->network; ?></td></tr>
<tr><td align="right"><b>AS:</b></td><td><?php echo $d->as; ?></td></tr>
<tr><td align="right"><b>AS Name:</b></td><td><?php echo $d->asname; ?></td></tr>
<tr><td align="right"><b>AS Size:</b></td><td><?php echo $d->assize; ?></td></tr>
<tr><td align="right"><b>Country:</b></td><td><?php echo $d->country; ?></td></tr>
<tr><td align="right"><b>Count:</b></td><td><?php echo $d->count; ?></td></tr>
<tr><td align="right"><b>Attacks:</b></td><td><?php echo $d->attacks; ?></td></tr>
<tr><td align="right"><b>Min Date:</b></td><td><?php echo $d->mindate; ?></td></tr>
<tr><td align="right"><b>Max Date:</b></td><td><?php echo $d->maxdate; ?></td></tr>
<tr><td align="right"><b>Last Updated:</b></td><td><?php echo $d->lastupdated; ?></td></tr>
<tr><td align="right"><b>Abuse Contact:</b></td><td><?php echo $d->asabusecontact; ?></td></tr>
<tr><td align="right"><b>Comment:</b></td><td><?php echo $d->comment; ?></td></tr>
</table>
2. Edit your $RTIRHOME/etc/RTIR_SiteConfig.pm and add the new service in $RTIRIframeResearchToolConfig (pointing to your URL):
1 => { FriendlyName => 'SANS ISC IP Info', URL => 'http://xxxxxxxx/isc_ipinfo.php?ip=__SearchTerm__' },
3 => { FriendlyName => 'Google', URL => 'https://encrypted.google.com/search?q=__SearchTerm__' },
4 => { FriendlyName => 'CVE', URL => 'http://cve.mitre.org/cgi-bin/cvekey.cgi?keyword=__SearchTerm__'},
5 => { FriendlyName => 'TrustedSource.org', URL => 'http://www.trustedsource.org/query/__SearchTerm__'},
6 => { FriendlyName => 'McAfee SiteAdvisor', URL => 'http://www.siteadvisor.com/sites/__SearchTerm__'},
7 => { FriendlyName => 'BFK DNS Logger', URL => 'http://www.bfk.de/bfk_dnslogger.html?query=__SearchTerm__#result'}
} );
3. Restart your RTIR instance and enjoy! You can now query the DShield API:
.png)
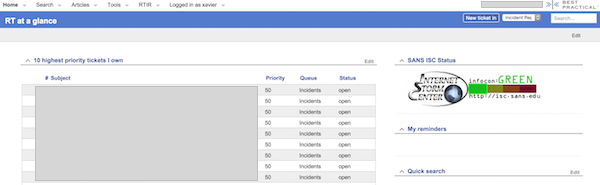
It's also easy to create new "portlets" to be used in dashboards. As a bonus, let's display the ISC Infocon status in a RTIR dashboard.
1. Create the new portlet in $RTIRHOME/local/html/Elements. Let's call it "InfoconStatus":
<table>
<tr>
<td>
<img src="https://isc.sans.edu/images/status.gif" alt="SANS ISC Infocon Status">
</td>
</tr>
</table>
</&>
2. Enable the new portlet in $RTIRHOME/etc/RTIS_SiteConfig.pm:
QuickCreate
Quicksearch
MyAdminQueues
MySupportQueues
MyReminders
RefreshHomepage
Dashboards
SavedSearches
InfoconStatus
/RTIR/Elements/NewReports
/RTIR/Elements/UserDueIncidents
/RTIR/Elements/NobodyDueIncidents
/RTIR/Elements/DueIncidents
));
3. Restart your RTIR instance and adapt your favorite dashboards:
(1) https://isc.sans.edu/forums/diary/Automating+Metrics+using+RTIR+REST+API/20087/
(2) https://www.bestpractical.com/rtir/
(3) https://isc.sans.edu/api/
Xavier Mertens
ISC Handler - Freelance Security Consultant
rootshell.be
truesec.be


Comments