A .BUP File Is An OLE File
Yesterday I mentioned that McAfee quarantine files on Windows (.BUP extension) are actually OLE files.
I'm going to write a couple of diary entries highlighting some file types that are OLE files, and I'm starting with .BUP files.
OLE files can be analyzed with my oledump tool. Here is an example with a .BUP file:
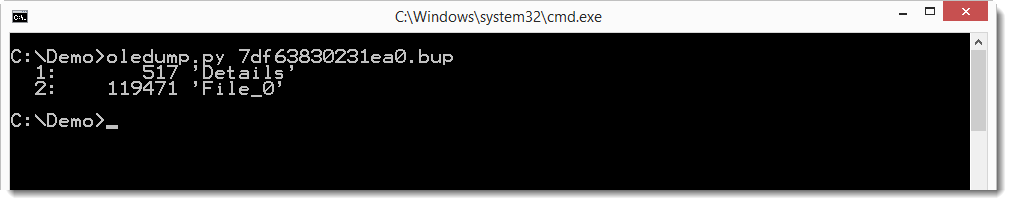
As you can see, this quarantine file contains two steams: Details and File_0. Details is the McAfee anti-virus report, and File_0 is the quarantined file. Remark that quarantine files can contain more than one quarantined file, they will be numbered File_0, File_1, ...
If we look at the Details stream, it doesn't tell us much:
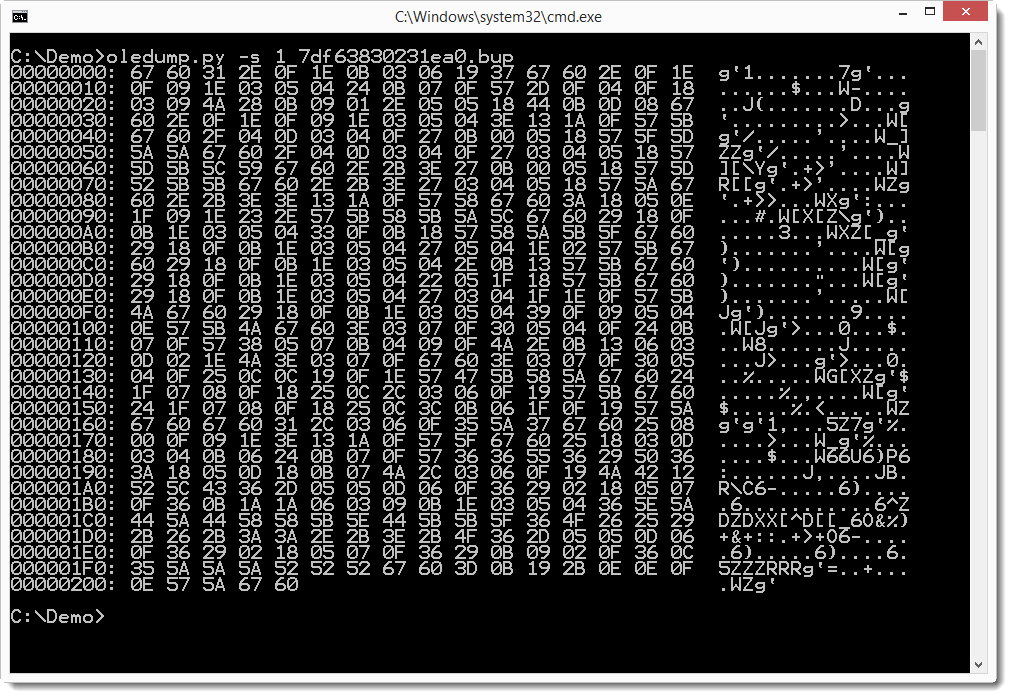
That's because it is XOR encoded. The key is 0x6A (BTW, 0x6A is j and I always wondered if that was a reference to John). We can use an oledump decoder to decode this:
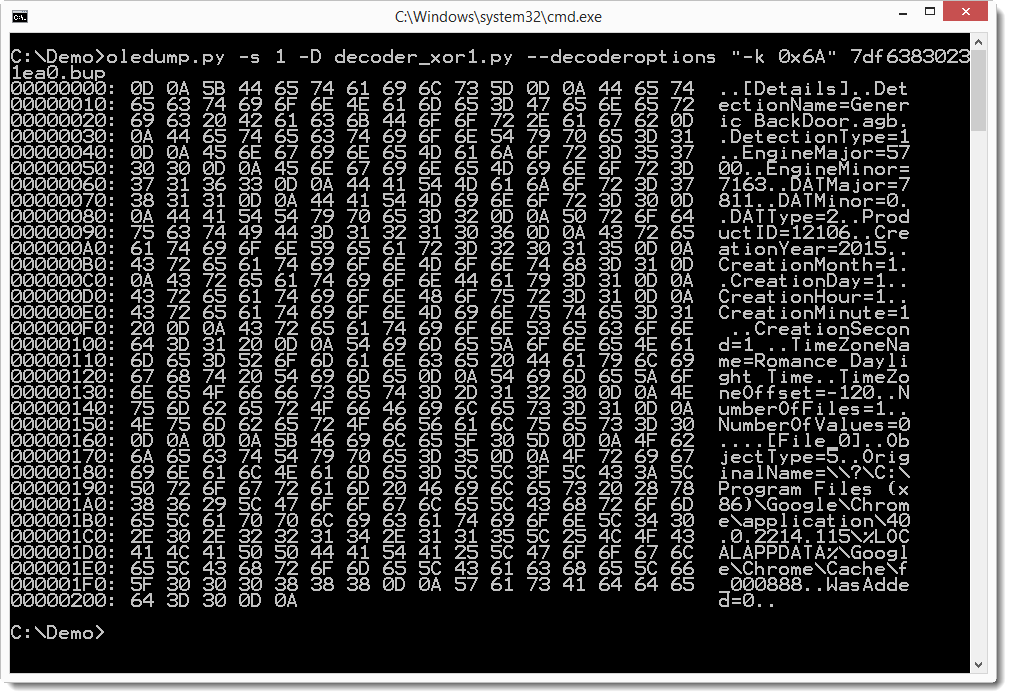
That's readable, so let's dump it:
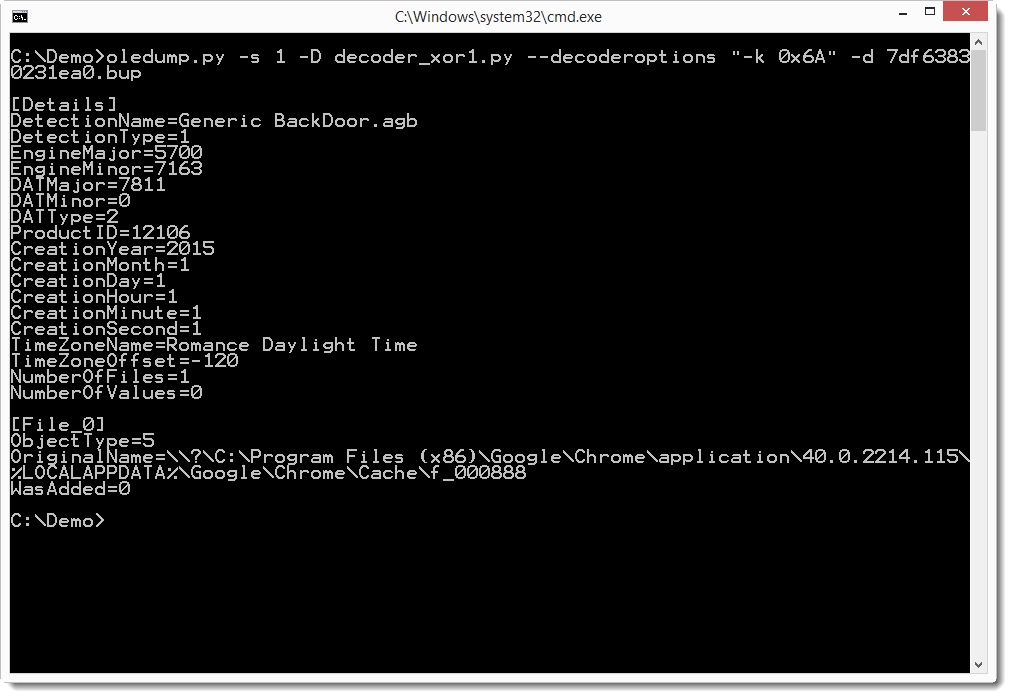
Generic BackDoor.agb doesn't tell us much, but if we look at the beginning of the quarantined file, it becomes clear:
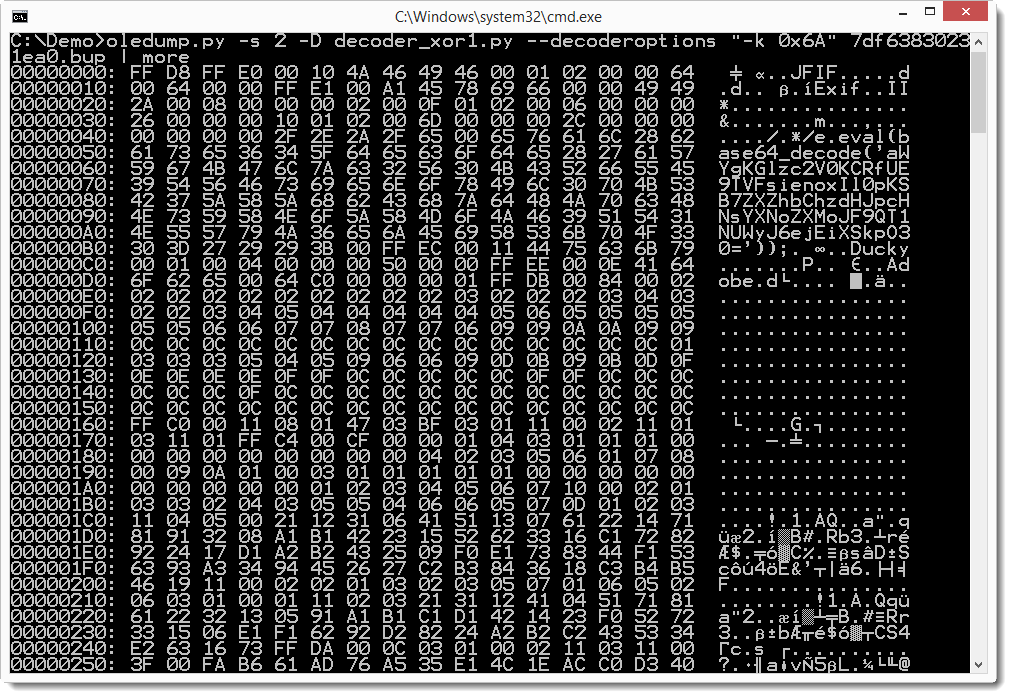
This is a JPEG file with an eval statement in the EXIF data.
Didier Stevens
Microsoft MVP Consumer Security
blog.DidierStevens.com DidierStevensLabs.com


Comments