Microsoft Patches appear to be causing problems
Just a heads up to our readers. We have received multiple reports of Microsoft patches causing machines to hang. There is also a report that Microsoft has pulled one of the patches. Specifically, we have had issues reported with the Visual Studio Patch. We will continue to monitor the situation and keep you posted. If you have any more information on this please leave us a comment.
Thank you
Mark Baggett
Detecting Mimikatz Use On Your Network
I am an awesome hacker. Perhaps the worlds greatest hacker. Don't believe me? Check out this video where I prove I know the administrator password for some really important sites!
(Watching it full screen is a little easier on the eyes.)
http://www.youtube.com/watch?v=v2IVRcktKZs
OK. I lied. I'm a fraud and I'll concede the title of greatest hacker to those listed at attrition.org's charlatans page. I didn't really hack those sites. But I certainly did enter a username and password for those domains and my machine accepted it and launched a process with those credentials! Is that just a cool party trick or perhaps something more useful? What happened to those passwords I entered?
The /netonly option for the runas command is used to launch a program as a user that exists on a remote machine. The system will accept the username and password for that remote user and create an authentication token in the memory of your LSASS process without any interaction with the remote host. With this option I can run commands on my host as the administrator of the microsoft.com domain without having to actually know the password for that account. Sounds dangerous? Well, it is not really. The command that you run doesn't really have any elevated access on your machine and with an invalid password it is not a threat to Microsoft. Windows doesn't try to authenticate to the Microsoft.com domain to launch the process. It assumes that the credentials are correct, calculates the hashes and stores them in memory for future use. At some point in the future, if you try to access a resource on that domain it will automatically use windows single sign on capabilities to "PASS THE HASH" to the remote system and log you in. But until you try to access the remote network, the passwords just sit there in memory.
The result is a really cool party trick and an even cooler way we can detect stolen password hashes being used in our environment. You see, those fake credentials are stored in the exact same location as the real credentials. So, when an attacker uses mimikatz, windows credential editor, meterpreter, procdump.exe or some other system to steal those passwords from your system they will find your staged "Honey Hash Tokens" in memory. It is worth noting that they will not see those hashes if they use "run hashdump", "hashdump" or any of the other commands that steal password hashes from disk rather than memory. However, that is not uncommon unless the attacker is on the Domain Controller and it will not raise suspicion.
Let's try it out and see how this deception might look to an attacker. First, I ran the following command to create a fake microsoft.com administrator record:
Then, when prompted for the microsoft.com administrator I can provide any password that I want. In this example I typed "superpass". Now, let's create an account for root on the domain linux.org. Yes, I know that is absurd. The absurdity demonstrates that you can put anything in LSASS you want. You can even use this to post snarky messages taunting the attackers if you want to live dangerously. (Not Recommended) Here is what you type to create those credentials.
Once again, when prompted for the root user's password, I can enter anything I want. For this example I choose "notreallythepassword". You will need to leave those command prompts running on your system to keep the credentials in memory. That is something a careful attacker might notice, but I'm betting they won't. Next, I ran mimikatz to see what an attacker would see and this is what I found:
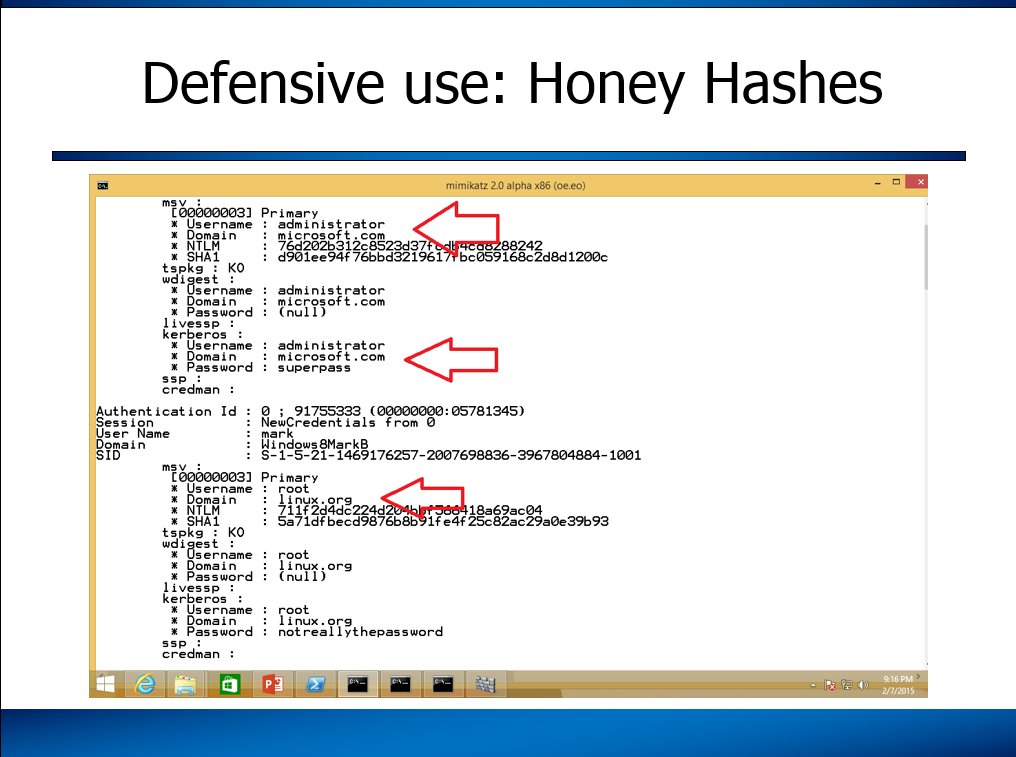
You can see both the hashes and clear text passwords sitting there just waiting for a hacker to find them. But these hashes, unlike all the others, will not get them anywhere on my network. This powerful deception can be exactly what you need to detect the use of stolen passwords on your network.
Here is the idea. You stage these fake credentials in the memory of computers you suspect might be the initial entry point on your network. Perhaps all the computers sitting in your DMZ. For a great deception my friend Rob Fuller (@mubix) is toying with the idea of putting this into the logon scripts to stage fake workstation administrator accounts on all the machines in your network. Then you would setup alerts on your network that detect the use of the fake accounts. Be sure to choose a username that an attacker will think is valid and will have high privileges on your domain. So rather than microsoft.com\administrator you might try
That's the idea. I hope it is helpful.
UPDATE: The name "honeytokens" was originally coined by Augusto Barros https://twitter.com/apbarros way back in 2003. Although I called them "honey hashes" there have been some other cool names suggested. I like Rob VanderBrinks name of "Credential Canaries". Other suggested names include "password phonies" ,"lockout logins" or "Surreptitious SATs" but in the end they are just another type of honeytoken.
Mark Baggett Follow me on Twitter:@markbaggett
Like this? Interested in learning how to automate this and other common tasks with Python? Join me in Orlando Florida April 13th Attackers and Defender will learn the essentials of Python, networking, regular expressions, interacting with websites, threading and much more. Sign up soon for discounted pricing.
Microsoft Update Advisory for February 2015
Overview of the February 2015 Microsoft patches and their status.
| # | Affected | Contra Indications - KB | Known Exploits | Microsoft rating(**) | ISC rating(*) | |
|---|---|---|---|---|---|---|
| clients | servers | |||||
| MS15-009 | Security Update for Internet Explorer (ReplacesMS14-080 ) |
|||||
|
Microsoft Windows,Internet Explorer
(39 CVEs. Too many to list here) |
KB 3034682 | . | Severity:Critical Exploitability: 0 |
Critical | Critical | |
| MS15-010 | Vulnerabilities in Windows Kernel-Mode Driver Could Allow Remote Code Execution (ReplacesMS13-006 MS14-066 MS14-074 MS14-079 ) |
|||||
| Microsoft Windows CVE-2015-0003 CVE-2015-0010 CVE-2015-0057 CVE-2015-0058 CVE-2015-0059 CVE-2015-0060 |
KB 3036220 | vuln. public. | Severity:Critical Exploitability: 2 |
Critical | Critical | |
| MS15-011 | Vulnerability in Group Policy Could Allow Remote Code Execution (ReplacesMS13-031 MS13-048 MS15-001 ) |
|||||
| Microsoft Windows CVE-2015-0008 |
KB 3000483 | . | Severity:Critical Exploitability: 1 |
Critical | Critical | |
| MS15-012 | Vulnerabilities in Microsoft Office Could Allow Remote Code Execution (ReplacesMS13-085 MS14-023 MS14-081 MS14-083 ) |
|||||
| Microsoft Office CVE-2015-0063 CVE-2015-0064 CVE-2015-0065 |
KB 3032328 | . | Severity:Important Exploitability: 1 |
Critical | Important | |
| MS15-013 | Vulnerability in Microsoft Office Could Allow Security Feature Bypass | |||||
| Microsoft Office CVE-2014-6362 |
KB 3033857 | vuln. public. | Severity:Important Exploitability: 1 |
Important | Important | |
| MS15-014 | Vulnerability in Group Policy Could Allow Security Feature Bypass | |||||
| Microsoft Windows CVE-2015-0009 |
KB 3004361 | . | Severity:Important Exploitability: 2 |
Important | Important | |
| MS15-015 | Vulnerability in Microsoft Windows Could Allow Elevation of Privilege (ReplacesMS15-001 ) |
|||||
| Microsoft Windows CVE-2015-0062 |
KB 3031432 | . | Severity:Important Exploitability: 2 |
Important | Important | |
| MS15-016 | Vulnerability in Microsoft Graphics Component Could Allow Information Disclosure (ReplacesMS14-085 ) |
|||||
| Microsoft Windows CVE-2015-0061 |
KB 3029944 | . | Severity:Important Exploitability: 2 |
Important | Important | |
| MS15-017 | Vulnerability in Virtual Machine Manager Could Allow Elevation of Privilege | |||||
| Microsoft Server Software CVE-2015-0012 |
KB 3035898 | . | Severity:Important Exploitability: |
Important | Important | |
We appreciate updates
US based customers can call Microsoft for free patch related support on 1-866-PCSAFETY
- We use 4 levels:
- PATCH NOW: Typically used where we see immediate danger of exploitation. Typical environments will want to deploy these patches ASAP. Workarounds are typically not accepted by users or are not possible. This rating is often used when typical deployments make it vulnerable and exploits are being used or easy to obtain or make.
- Critical: Anything that needs little to become "interesting" for the dark side. Best approach is to test and deploy ASAP. Workarounds can give more time to test.
- Important: Things where more testing and other measures can help.
- Less Urt practices for servers such as not using outlook, MSIE, word etc. to do traditional office or leisure work.
Mark Baggett Follow me on Twitter:@markbaggett
Join me in Orlando Florida April 13th Attackers and Defender will learn the essentials of Python, networking, regular expressions, interacting with websites, threading and much more. Sign up soon for discounted pricing.


Comments