Some Logs and/or packets please?
Hi, if you have some logs from the following subnets to your infrastructure and you are able to share, could you?
- 61.174.51.0/24 (although I'll take /16)
- 218.2.0.0/24
- 122.225.0.0/16
- 112.101.64.0/24
- 103.41.124.0/24
- 61.240.144.0/24
If you can't share logs or packets, maybe you could send me a source IP and Destination Port. (just use the contact form or send them direct to markh.isc (at) gmail.com )
The above are all active on SSH and DNS, just trying to see if there is anything else and if so what and in which part of the world.
Regards
Mark
NOTE: Thanks for all the info so far, very much appreciated, keep it coming. If sending a file please email direct to markh.isc (at) gmail.com as the contact form file facility is having a challenge. It is being looked at, but in the mean time please use the email address. - RESOLVED
Update: Firstly thank you all for providing information. The response has been great. I've spent the last 5 hours sending thank you's and getting the info down :-).
A first look at the data is already providing some interesting info. I'll hopefully get the first cut of some info out later today. If you have devices in the Middle East, Africa, Asia, Europe, South America or Australia I especially interested in those. Also if you have a packet capture for allowed connections from 61.240.144.64, 65, 66, 67 or IDS/IPS capture of the initial request (allowed or denied) and you can share, great.
Some of the log shared so far include firewall and router logs, honeypot logs (one especially interesting as it is using P0F to passively finger print the source), but also some really interesting netflow and argus info. So again thanks to you all.
Thanks M
Microsoft advanced notification service changes.
Quite a few of you have written in to let us know that Microsoft is changing the way in which they provide information (thanks to you all). You can read the full blog here --> http://blogs.technet.com/b/msrc/archive/2015/01/08/evolving-advance-notification-service-ans-in-2015.aspx
In a nutshell if you want to be advised in advance you now need to register, select the products used and you will then be provided with information relating to the patches that will be released. If you are a premier customer your technical contact can provide information.
The main point for me is this one
"Moving forward, we will provide ANS information directly to Premier customers and current organizations involved in our security programs, and will no longer make this information broadly available through a blog post and web page"
Now a lot of us do look at that information to plan their next patching cycle. So you will need to look at that process and see what needs changing. You'll have to rely on the information in your patching solution, or register.
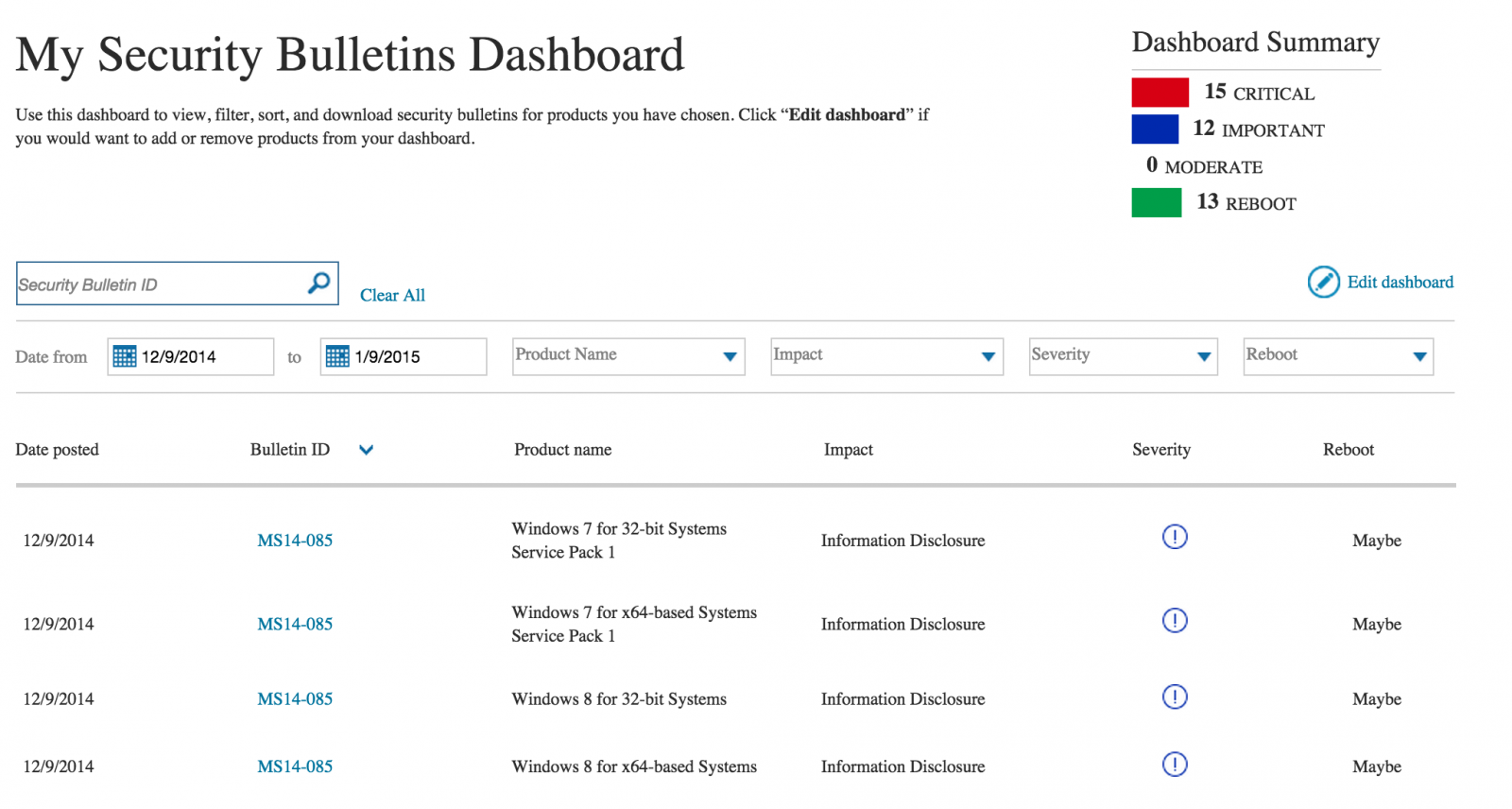
You can register here: http://mybulletins.technet.microsoft.com/
The dashboard that is created in the end looks nice, but for me to early to tell how useful it is at this stage, although it was slightly painful to review each bulletin. It will take a few patch cycles to sort it all out I'd say.
So going forward you will need to adjust how you identify the patches to be applied within your environment. If you do not want to register you can just visit the main bulletins page here --> https://technet.microsoft.com/en-us/library/security/dn631937.aspx
This page has a list of all release bulletins.
Cheers
Mark H


Comments