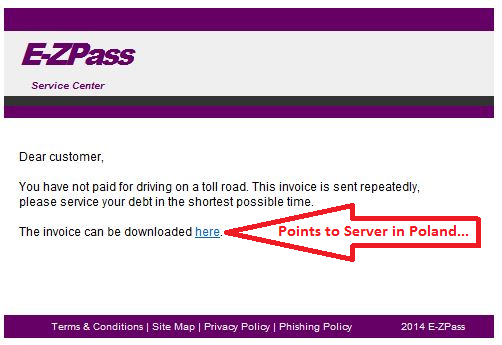
E-ZPass phishing scam
Over the last couple of days, we have been seeing a number of quite credibly looking phishing emails that impersonate toll-road providers in the US. The agency affected by the current wave is E-ZPass, a toll charging system used mainly in the Northeast. Adapting the template to match the colors and fonts of other organizations, like Florida's SunPass, would be easy to accomplish for the scammers though, so chances are that we will see more of this.
Since toll road agencies can impose stiff fines for violations or if road and bridge charges are not paid in time, people might fall for it and click on the link just to make sure. In the samples at hand, the link was pointing to www . ruckon . pl (spaces added to de-fang), and returned a ZIP with an EXE or directly an EXE. Hat tip to ISC reader Wayne for providing the latest sample.
If you receive similar emails that impersonate other toll road providers, please let us know.
The Internet of Things: How do you "on-board" devices?
Certified pre-pw0ned devices are nothing new. We talked years ago about USB picture frames that came with malware pre-installed. But for the most part, the malware was added to the device accidentally, or for example by customers who later returned the device just to have it resold without adequately resetting/wiping the device.
But more recently, more evidence emerged that everything from network gear [1] to inventory scanners [2] may be infected deliberately in order to penetrate otherwise hard to reach networks. Typically, there is little a customer can do to verify that a device is not infected. Standard practices, like malware scanners and verifying installed software doesn't always work if you don't have "shell access" or the ability to install software on the device.
This leaves careful network monitoring as one option to detect and disrupt command and control channels used by these devices. However, in order to do so accurately, it is important to characterize "normal" network traffic from the device, which can be challenging in particular if the device connects to cloud services for updates or intentional data exchange.
The large number of these devices entering our networks asks for a scalable solution. We can't add security devices and personal proportional to the number of devices deployed. The security features included in these devices (host based firewalls, encryption technologies, ability to manage and limit installed software/"apps") varies widely and frequently there are no enterprise configuration tools available.
What kind of network segmentation and on-boarding procedure do you apply to new devices introduced into the network?
[1] http://arstechnica.com/tech-policy/2014/05/photos-of-an-nsa-upgrade-factory-show-cisco-router-getting-implant/
[2] http://www.trapx.com/news/press/trapx-discovers-zombie-zero-advanced-persistent-malware/


Comments