Knowing where to look for the owner of an offending IP address
by Manuel Humberto Santander Pelaez (Version: 1)
We often see how attackers try to exploit our information assets in our company, coming from inside and outside the company. When you locate an internal IP address trying to affect things, it's easy to locate if you have information security controls like Network Access Control (NAC), Dynamic Host Configuration Protocol (DHCP), Firewalls and Network IPS. Problem is: what should we do if the offending ip address is outside in the Internet?
There are five Regional Internet Registry (RIR) entities in the world. For their region, they assign IP address for IPV4, IPV6 and autonomous system numbers:
Source: IANA web site
- AfriNIC: Covers the Africa Region
- APNIC: Covers the Asia Pacific Region
- ARIN: Covers the North American Region
- LACNIC: Covers Latin America and some caribbean islands
- RIPE NCC: Covers Europa, the middle east and central asia
All RIR provides a tool called whois. This tool is able to tell you who is the owner of an IP address or a netblock. All contacts listed in RIR are required to provide an abuse contact. This contact is meant to provide point of contact for any required actions of stopping an attacker or to request evidence for a criminal investigation if you are a law enforcement agency.
Let's see an example. If we look for ip address 66.35.59.202, we can start using ARIN to look up for it. In the main ARIN website (http://www.arin.net), there is a text box after the "Search Whois" string. After entering 66.35.59.202, you obtain the following:
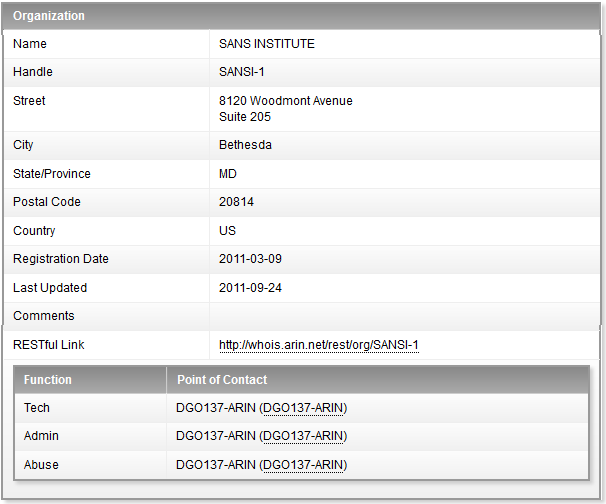
The Abuse contact information is a URL following the contact ID pointing to the specific information needed to contact the SANS Institute regarding abuse from their IP address range.
Let's see another example. If we look for IP address 200.13.232.33, we find the following:
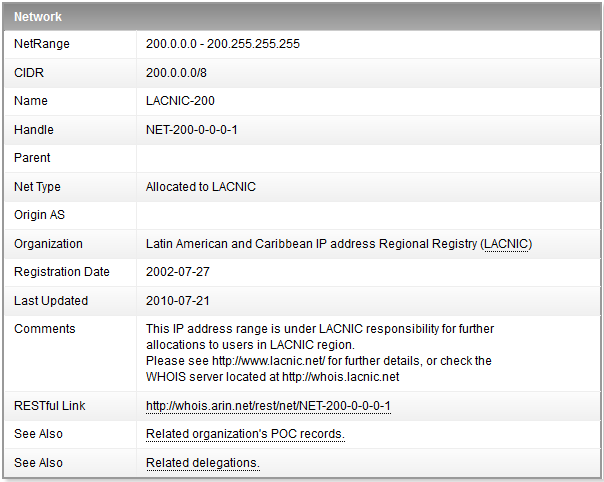
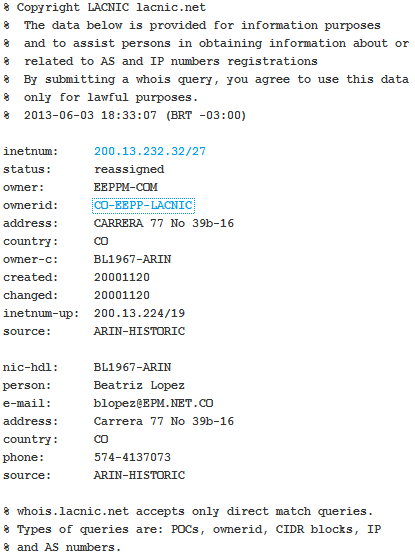
This information means that the IP address is not within the ARIN scope and the information must be looked up at the LACNIC RIR. After looking the information into the LACNIC whois, we obtain the following:
Using google to lookup information for owership of an specific ip address is definitely not a good idea, as it looks for the IP address string inside all webpages indexed. The information google will give you will provide a lot of false positives and will delay you in your incident response process execution and / or your criminal investigation.
Manuel Humberto Santander Peláez
SANS Internet Storm Center - Handler
Twitter:@manuelsantander
Web:http://manuel.santander.name
e-mail: msantand at isc dot sans dot org


Comments