Another round of "Spot the Exploit E-Mail"
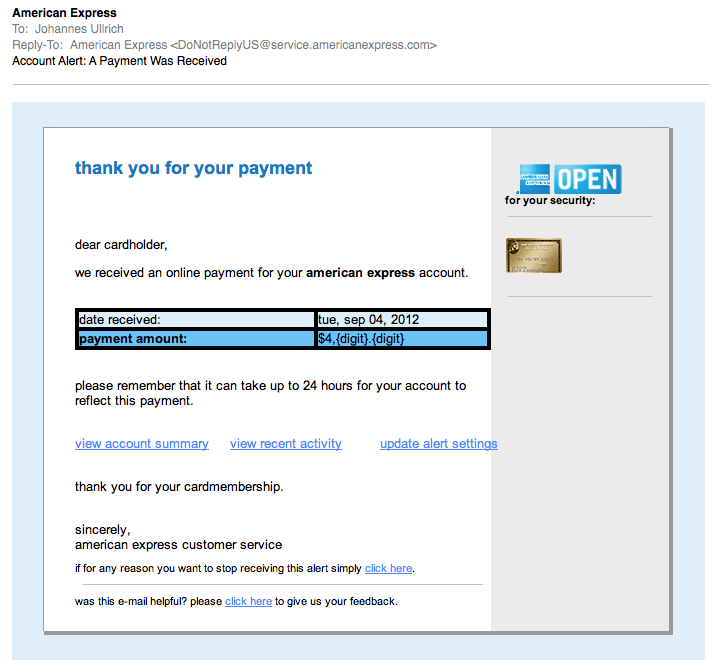
We have come to expect quality phishing/fake email work these days. In a recent diary I showed how well one crew impersonated Verizon e-mails to spread malware. So I was a bit disappointed when I got this e-mail this morning:
(click on image to see it full size)
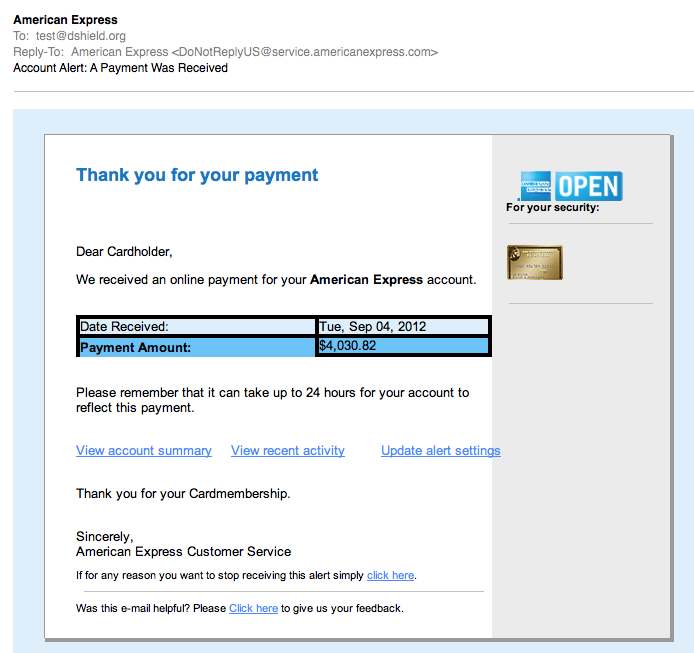
The e-mail has a number of obvious deficiencies. For example, the missing "digits" in the payment amount., and the fact that it is all lower case. But all wasn't lost. Looks like ACME Phishing was hard at work fixing the bugs, and the QA team shortly sent a second email (but to another account of mine):
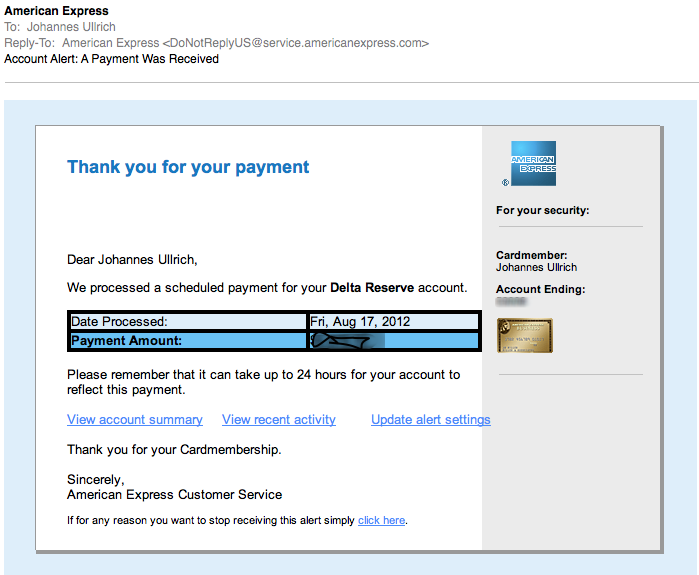
Finally, a real e-mail from American Express. I blurred the amount and the last few digits of the account number. I also replaced the image of the card. But as you can see, the real e-mail is VERY CLOSE. Probably the most significant difference is that the last digits of the account number are missing at the fake. But I doubt many people look for this.
So what is the fake e-mail trying to do? Imagine that: It will get you malware... In my copies, the initial link goes to hxxp:// vserver94 . antagus . de
That page then includes three javascript files loaded from these domains:
atriumworkcomp.com, mlegion.com , watchdogwebdesign.com . The javascript file name is js.js.
The javascript will then redirect the user to one of these two IP addresses:
96.47.0.163, 108.178.59.26
both IP addresses yield heavily obfuscated javascript. The wepawet analysis can be found here:
http://wepawet.iseclab.org/view.php?hash=3c550bbf81ebfcd7979f2147fb69729c&type=js
It appears to be the usual "what vulnerable plugin are you running today?" javascript.
------
Johannes B. Ullrich, Ph.D.
SANS Technology Institute
Twitter


Comments