Privilege escalation 0-day in almost all Windows versions
Today proof of concept code (source code, with a compiled binary) of a 0-day privilege escalation vulnerability in almost all Windows operating system versions (Windows XP, Vista, 7, Server 2008 ...) has been posted on a popular programming web site.
The vulnerability is a buffer overflow in kernel (win32k.sys) and, due to its nature allows an attacker to bypass User Access Control (UAC) on Windows Vista and 7 operating systems.
What’s interesting is that the vulnerability exist in a function that queries the registry so in order to exploit this the attacker has to be able to create a special (malicious) registry key. Author of the PoC managed to find such a key that can be created by a normal user on Windows Vista and 7 (so, a user that does not even have any administrative privileges).
The PoC code creates such a registry key and calls another library which tries to read the key and during that process it ends up calling the vulnerable code in win32k.sys.
Since this is a critical area of the operating system (the kernel allows no mistakes), the published PoC only works on certain kernel versions while on others it can cause a nice BSOD. That being said, the code can be probably relatively easily modified to work on other kernel versions.
We are not aware of any exploitation of this vulnerability at the moment and, since it can be exploited only locally, it obviously depends on another attack vector, but knowing how users can be easy on clicking on unknown files, this is definitely something we will keep our eye on and post updates if we see exploitation.
The PoC has been in the mean time removed from the original site but now that it has been published I’m sure that everyone who wants to get it can do that easily.
QUICK UPDATE:
I just wanted to confirm that the PoC works as advertised, as you can see below:
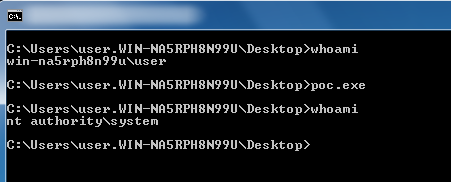
However, as expected (and stated by the PoC author), on my version of Windows 7, which has win32k.sys 6.1.7600.16667, it is unstable and causes a pretty nasty BSOD after couple of minutes (had even to restore the previous system state to get Windows to boot).
--
Bojan
INFIGO IS


Comments
http://www.h-online.com/security/news/item/Exploit-released-for-unpatched-Stuxnet-hole-1140196.html
Unbelievable that Microsoft's most "secure" operating systems (w7/w2k8) seem to use crc32 instead of a secure hash.
Bitwiper
Nov 24th 2010
1 decade ago
http://www.exploit-db.com/exploits/15589/
PHolder
Nov 24th 2010
1 decade ago
MS seems to be/may be aware of the issue acording to http://mobile.twitter.com/msftsecresponse/status/7590788200402945
Ottmar Freudenberger
Nov 25th 2010
1 decade ago
Are you sure this will work on Windows XP too? There's no HKCU\EUDC registry key...
Ottmar Freudenberger
Nov 25th 2010
1 decade ago
In the specific exploit, the publisher looked for a registry key that meets 2 criteria:
- it is writable by a non-privileged user;
- a kernel-mode OS function (GDI in this case) can be triggered to read a value from that specific registry key.
So the EUDC registry key is just one vector, others may exist.
Bitwiper
Nov 27th 2010
1 decade ago